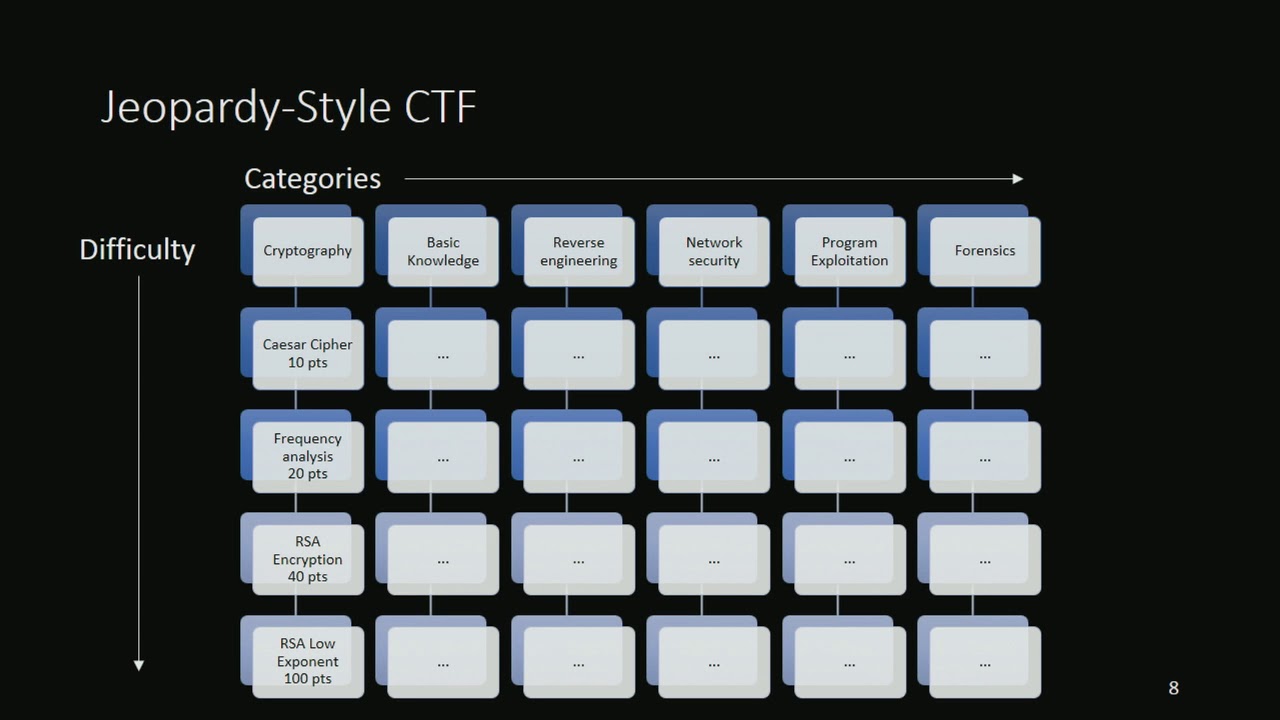
war is part of our Human Experience the way we fight it is changing technology is defining the future of warfare it's changing the way we think about making decisions in Warfare providing capabilities that were previously unreachable lessons from the past inform the future at every technological leap redraws the battle lines we once knew technology was once a spear today it is a Cyber attack the amount of interconnected technology has fundamentally transformed the operational environment familiar domains grow increasingly complex and the race to dominate the ultimate High Ground has begun in the same way we think about CPAP we need to start thinking about the strategy for space as machines take the reins the speed of warfare accelerates ever faster technology has always shaped War Evolution has always happened in war and in society it will continue to in war has always shaped Humanity in this age of hyper connectivity Our Lives rely on technological systems like never before we are entangled in the tentacles of the internet and our data is prone to invasion conflict now happens in the virtual domain for the push of a button beats the squeeze of a trigger bringing disorder without a single soldier setting foot on the ground the future of warfare is cyber [Music] what would happen if we all got up one morning and nothing was working there was no internet our public transport systems wouldn't work our roads wouldn't work everything wouldn't work and that's an interesting perspective when you look at what a military might do to shut down a jurisdiction before they go in and fight a battle two days before Christmas in 2015. the Lights Went Out in Ukraine hackers had infiltrated three electricity distribution companies and they'd done so with remarkable ease simply by attaching malware infected code to Word documents and PowerPoint presentations sent to company Executives by email the malware called black energy was attributed to a Russian cyber gang by the name of sandworm having infiltrated the electrical company's computer systems the hackers now had the ability to flip the power grid circuit breakers the electrical supply of almost a quarter of a million people began to Fountain but the hackers didn't stop there the next phase saw a utility company call centers inundated with a barrage of automated telephone calls multi-wave attack was underway chaos and confusion soon led to outrage as complaints from frustrated customers had reports from company response teams went unheard medical centers were overwhelmed Ukraine was plunged Into Darkness [Music] when light Shone again in Ukraine a new realization dawned was the first documented time a Cyber attack had directly targeted and taken down a nation's power grid the border between the physical and the digital had been broken down [Music] in 1969 the first message was sent across arpanet the advanced research projects agency Network and it was from this first step that the internet as we know it today was born now billions of people use the internet each and every day it is interwoven Into The Very fabric of our society internet has created tremendous access to information and technology for basically vast number of populations across the globe so as long as there is internet connectivity you can access everything that exists on the internet and as a result there's a tremendous amount of positive things that come out of it people can stay in touch people can have access to educational materials people can do business remotely and build collaborations but at the same time it creates a vulnerability service we used to go to the Internet when we think back to the mid-1990s now we live in the internet particularly Via Mobile smart devices and invariably the first thing we do in the morning is check our device the last thing we do at night is check our device and we're on it all day so it gives a range of options to a military to weaponize that aspect of it because it's so integrated in our day-to-day lives critical infrastructure supports our connected lives The Wider we drink the food we eat our banking systems GPS rely on transportation and transportation hubs government services communication networks our smart Vehicles Smart Homes smart offices and factories are smart cities all as cyber Reliant and being so all are prone to Cyber attack [Music] we have spent the last or so years really focusing on development of new technology we've developed a lot of this technology without barely any security or privacy baked in if we try to understand what cyber warfare looks like from the offensive and defensive aspects we have to take into account first the large number of computerized systems deployed in each country's armed forces and in the Civil sector of each country that Reliance creates vulnerabilities in just everybody's computer system and computer devices in cyber warfare the aim is to attack key weapon to attack key Civil infrastructure of the enemy to undermine their war effort and then we have to ask ourselves the question well how many unique computerized systems are there in the armed forces of the adversary country it is probably well in excess of 5 000 unique computerized systems in any military force and we're looking then at in excess of 10 or 20 000 unique computerized systems in the Civil infrastructure of any country foreign in most organizations and in most countries cyber security is weak to very weak and this gives huge potential for an attacker in cyber warfare and imposes huge burdens on the defender the amount of effort that it takes to secure a computer system essentially continues to grow exponentially whereas the amount of effort to penetrate a computer system is linear because all you need is one vulnerability cyber warfare is disruptive Warfare and it Heralds a new era of military operations reshaping the combat zone into a multi-platform digital battle space where data is the loaded gun it can enable whichever side you're on it can also disable whichever side you're on so it really is the length and breadth of every aspect it allows you to manifest organizations that may not have existed before because the connectivity between the AC and land forces is potentially very very tight and you're able to command operations and make changes in much more quicker timeline than has been possible in the past [Music] the potential for cyber attacks to impact the physical world had been realized as early as 2010. when the natan's nuclear facility in Iran was attacked a malicious malware computer program stuxnet often referred to as a worm had infiltrated Iran's nuclear enrichment facility someone physically brought in the code and we don't know how really that happened there's been suggestions of a USB thumb drive just being plugged into the front of a device stuxnet was a malicious computer worm that is widely understood although not confirmed to have been an American and Israeli operation deployed in an Iranian nuclear reactor undetected the stuxnet worm worked its way through the facility's industrial control system once the code was injected into the facility we saw that the Siemens Control Systems sped out of control and subsequently not work anymore stuxnet took out one in five centrifuges at the reactive where it was deployed and you think previously that would have been Possible only through bombing or inserting people in the ground [Music] like a scene from a spy movie The stuxnet Worm also secretly recorded daily operations within the facility playing them in a loot to plant operators convincing them that nothing out of the ordinary was happening in fact the centrifuges were shredding themselves apart between 2009 and 2010 close to 1 000 centrifuges in the Iranian facility were destroyed that really resulted in the Iranian nuclear project being set back you know some months potentially some years I think really it goes to show what can occur using a line of code to actually break something physical [Music] the success of stuxnet at the natan's nuclear facility shifted the shape of traditional War methodologies and conventional military operations [Music] this notion of cyber attacks and notion of cyber warfare has evolved quite significantly over the last few decades I'd like to frame this in context of diversity of cyber attacks traditionally the notion of a Cyber attack was focused on Attack on essentially a computer system so attacking computers networks hard drives operating systems etc for example someone can send you a piece of malware which is a malicious piece of software that essentially encrypts your hard drive that is a type of attack that's typically referred to as ransomware so your computer system is now encrypted and you cannot access any information on your system in 2017 a piece of ransomware took the World by storm and demonstrated the true Havoc a Cyber attack could wreak upon Society Ukraine was again the target of a Cyber attack that seemingly came from nowhere not petya a ransomware worm that spread across 10 percent of all computers in Ukraine like before Transportation hubs Banks government agencies media outlets and utility companies were paralyzed not Petra then crossed borders Russia the U.
S France shutting down oil companies hospitals pharmaceutical and food production companies in Copenhagen it took the world's largest shipping firm molar mask offline the Havoc did not patch a caused was costed at approximately 10 billion dollars another type of Cyber attack could essentially be a denial of service attack essentially preventing people from being able to access the system by either generating too many messages or essentially fully utilizing the capacity of the central processing unit these are the cyber attacks that exploit the connectivity of our modern lives that can shut down our ports and airports expose private corporate and Military secrets and bring a society to its knees however like malicious malware that continues to reinvent itself so too does the way in which cyber attacks occur we use the term cyber everywhere but really it's information security which is at the heart of what we do and so in a future theater how you shape the use of the information whether that's winning the hearts and minds of people whether that's being disruptive to your enemy and their use of information and everything in between and it's the shaping of information that leads to some of the most Insidious forms of cyber warfare foreign Warfare is information greedy it feeds on and manipulates our Collective consciousness one person's truth is another person's fake news and the difference between can be exploited populations were once bombarded with propaganda dropped from planes above today our cyber world connects us to the infinite and immeasurable influence of others probably in the last five to ten years the notion of information Warfare has really emerged as another dimension of a potential offensive or defensive cyber capability what we're talking about is the conduct of political Warfare through cyberspace it's really the activity of one set of political leaders trying to do something quite nasty and quite serious to another country or another set of political leaders information is a valuable commodity in the cyber world exploited it can be used blackmail leaders cajole voters fan the Flames of discontent disseminate propaganda and create mythology today's society is so dependent on data that data makes it possible for us to organize our societies our political systems and even our private lives in the lead up to the 2016 U. S presidential elections the British firm Cambridge analytica unlawfully mined data from 87 million Facebook users with this State Republican presidential candidate Donald Trump's campaign team used psychographics to map voter personalities based on opinions values interests and more which then allowed them to surgically Target Facebook users with carefully sculpted advertisements for political gain do you think that you have an ethical obligation to notify 87 million Facebook users Senator when we heard back from Cambridge analytica that they had told us that they weren't using the data and had deleted it we considered it a closed case in retrospect that was clearly a mistake the Cambridge analytica Scandal where essentially a lot of the private data was used to Target election resources to private citizens and it wasn't obvious to the citizens as to what was happening social media has become an integral part of our Lives it connects us entertains us and it also informs us the Cambridge analytica Scandal highlighted just how important our personal data really is and just how much of it was being passed around behind the scenes but when it comes to social media it's not just our own information that matters the information passed down to us is just as important too if you can Master Facebook Instagram and Twitter then you've got 90 of the market covered we look at the various ways that cyber has shaped our environment and that's particularly where we get our news sources from now so because we have a couple of dominant sources if you want to radicalize people and it's been proven in the past you start winning those hearts and Minds via that way and you start getting your messaging out there and when people just go to that one place for news they're going to start believing that to be the case we've created this environment where things like misinformation disinformation and propaganda can be Amplified through the scale of the communication technology we essentially are at a point where there's a potential to compromise freedom of thought if someone's very much interested in manipulating how you think they have access to Broad amount of information around you but has just existed out there privacy is just recently now becoming a concern and neither regulations nor Technologies are are keeping up with the potential space of vulnerabilities information Warfare can be understood as either that narrow cyber domain or what's emerged more recently around the political Warfare the countries like China Russia and the United States are actively engaged in something that intentionally creates misinformation so false information things that are more formally malicious where there's a malicious intent where there's a desire to change people's minds or create confusion can be another type of an attack leveraging interconnectedness of infrastructure to manipulate populations into thinking or acting a certain way states are non-state actors that want to use information Warfare capitalize on the idea that if you can disrupt a society from within by creating more factions by creating more conflict between parties you'll be able to prevent that other Society from responding effectively to you either to your political threats or to your military threats so they're relying on the assumption that a breakdown in Social trust is beneficial to them the 2016 U. S presidential election was the hot spot for yet another cyber event fake social media accounts targeting Democratic presidential candidate Hillary Clinton sowed seeds of confusion and Discord amongst the U.
S electorate there was a lot of accountants on social media that were purposefully generating falsified information to often just create confusion in the population leading to impact on U. S elections the U. S intelligence agencies concluded that there was Russian interference some of it could be traced to the internet research agency which is a Russian organization which was essentially focused on infiltrating the trust of American public no Enterprise I sort of see that the moment that we're living in right now is essentially a new Sputnik moment that was the first space satellite and the United States was very much surprised by this event and then during the U.
S election essentially the manipulation of a lot of The Social Network Technology took the U. S completely by surprise it's a similar feel as it was during this Sputnik era and I think part of the reason that occurred is that you know we weren't really paying attention to how Technologies were being used the epidemic of malicious fake news and false propaganda that flooded social media over the past year it's now clear that so-called fake news can have real world consequences governments militaries and civilians have come to understand that technology can be used to mask the source of real threats distracting us with the trivial the cute the scandalous and conspiratorial while military Maneuvers take place there's there's stickers underlying lying understanding of Technologies is vital to understanding the threat landscape but really to understand the threat you have to understand the geopolitics and the human interactions with it [Applause] the Russians the same as everybody else seem to have expected Hillary Clinton to be the incoming president and what they were trying to do is as best we can work out was generate disruption and Chaos for a very limited period of time in order to allow them to move in the physical domain in a number of places around the world through November and December of 2016. Russia showered Syria with heavy air and cruise missile bombing their objective to drive out anti-government Rebel forces in eastern and southern Aleppo Syria [Music] start a clock at the moment that the U.
S election happened on November the 8th 2016. in the next month the Russians moved in and captured Aleppo City in Syria they then immediately launched an offensive into Eastern Aleppo province and at the end of that month they launched the advika offensive in Ukraine all of that happened in a two-month period after the election all of it had to have been prepared at least six months out [Music] several months before the fdfgo offensive began very Forum popular with Ukrainian military personnel had heavily promoted an Android application claiming to vastly improve the data processing speed of D30 Howitzer field guns the field guns used data for targeting the speed would be reduced from minutes to seconds huge numbers of Ukrainian artillery forces installed the app without a second thought [Music] the Ukrainian military were using a very old soviet-era artillery piece in order to make that more accurate they used Android cell phones to generate an app that would give you a precise firing solution for an individual gun and that allowed them to disperse and hide the weapons coordinate the firing remotely linking to GPS devices I gave them a dramatically higher level of precision little did they know the application had been implanted with malware known as hexaging Russian cyber militia by the name of apt-28 otherwise known as fancy beer working for Russian intelligence hacked the app created a back door that allowed them to figure out exactly where every Ukrainian gun was that was using this device so it was pro-russian Rebel troops surged toward the stronghold area of of divka a Cyber attack was already underway 20 minutes before the start of the advika offensive in January of 2017 russian-backed artillery started knocking out every Ukrainian gun that was using the device so they coordinated a Cyber attack with a social media campaign with a physical attack into a single unified operation in order to achieve a lethal physical effect on the ground so it's kind of like a one-two punch right where you've got a cyber operation that positions you for your next move which is physical and that then sets you up for your next cyber move in a sort of integrated maneuver the benefits of that approach are so profound that I think people are going to start jumping on that bad work and we're going to see more and more of that going forward [Music] cyber technology is advancing at an exponential rate [Music] a cyber warfare capabilities are realized by more and more adversaries the cyber security apparatus must develop simultaneously in 2020 the U. S Department of Defense requested just under 10 billion US dollars to continue to improve their cyber capability and lethality and to evolve cyber safeguards at the same Pace at which Cyber Technology develops the United States is the wealthiest most scientifically Advanced country in the world it has the best cyber security capability in the world but it's admitted many times that it's largely incapable of Defending itself in cyberspace in conflict the technical literacy of an average more fighter really needs to increase to match the capabilities that exist this is something that there's a lot of discussions certainly in the U.
S military about the need for training to keep up with availability of technology technology training a cyber security training fundamentals of a lot of the Technologies really need to be included in essentially military training cyber warfare changes the Rules of Engagement exists in a new warfare space a borderless environment making it difficult for friends or foes to determine both how to engage in or respond to a Cyber attack if we think about the more traditional Warfare sort of the kinetic engagement and things like nuclear positioning space positioning Etc there are significantly more Geographic boundaries the key thing about interconnectivity of today's world and essentially Reliance on interconnected systems that reside in the virtual space these are essentially borderless environments it's almost impossible to imagine two States going to war and fighting the war exclusively in cyberspace it won't be limited exclusively to cyberspace there'll be a whole range of kinetic activities going on there'll be economic Warfare there'll be cyber warfare there'll be information Warfare there'll be traditional kinetic operations as well change the organizations that we currently have across defense entities we are still very heavily armies navies and Air Forces but in the future as we go down this path where we need to undertake more influence operations and operations in the non-physical space we need to rebalance our organizations [Music] in future warfare kinetic domains will increasingly rely on Cyber operations working in Union will add a complexity to conflict which extends throughout a broader combat Spectrum when we think about cyber warfare about a decade ago many cyber warfare theorists were focused on cyber warfare as if it would be kind of a stand-alone form of conflict what we're seeing now is actually something different rather than being a standalone separate form of conflict what we're seeing is that as a force moves into a physical fight it's not only operating in the Land Air electromagnetic spectrum Maritime environment but it's also operating in cyberspace cyber warfare is really this combination of all these different techniques of warfare that we've been used to over time but with this very new powerful asset added so in a major political crisis or real war between two major Powers one country will try to hit another country in such a way that its war effort almost stops dead on the spot what we're looking at is wide-ranging what's called in the literature cyber paralysis [Music] I would suggest that in the context of how we understand military domains typically and classically defines through land Maritime and air increasingly the character of War will speak to the Cyber domain and the space domain and I would submit to you that any future military operation it doesn't account for itself on these non-physical emerging domains we'll lose so the idea is in peace time develop as many weapons packages as you can to attack any vulnerable system that the enemy might have especially attack their command and control with the expectation that not all of those attacks will succeed but with the intent that they'll be sufficiently focused and sufficiently targeted to have a very big retarding effect on the ability of the enemy to actually even get to the start line it's called of combat the potential of cyber warfare is devastating but with such a wide spectrum of possible effects ranging from Espionage to city-wide shutdown gauging the correct level of proportional response can be difficult and determining whether something is an act of war or not is an important distinction to make there's actually a significant body of work that's gone into deciding at what level does a Cyber attack rise to the point at which you can consider to be an act of War versus just an act of espionage when we look at Warfare we've had the Talon manual which gives us the rules of the road for how nation states should operate when it comes to cyber warfare operations in 2007 the Estonian city of talent became an unlikely cyber warfare hotspot Talon is the capital of Estonia which is one of the first environments where we saw a very significant Russian cyber warfare attack [Music] Estonian authorities had relocated a bronze statue of a World War II Russian soldier as well as remains from several Soviet War Graves from Central Talon to the outskirts of the city for the Estonian people the war memorial represented Russian occupation for estonians of Russian descent it represented Liberation from Nazi forces moving the statue to a lesser pedestrianized location was symbolic to both groups its relocation fan polyethnic outrage fueled by Russian media it triggered protests and riots between estonians and Russian descent Estonian populations which then culminated in a Cyber attack said to emanate from an enemy state the Cyber attack disabled estonia's highly dependent digital infrastructure government websites Banking and the media industry were hit hard detecting an attack is not the hard part the hard part is attributing responsibility for that attack to a particular actor and then figuring out what that actor's intent might be and that's extraordinarily difficult and I think something that we're going to see more of as a problem set as just the access to cyber capability grows Estonia was quick to pin blame on Russia foreign Ministry produced a document linking Russian government internet addresses with the attack Russia has repeatedly denied involvement when the Estonian Cyber attack took place a new form of warfare was launched non-state actors could strike unnoticed with no need to insert militaries and equipment [Music] as the burgeoning threat of cyber warfare grew NATO quickly stepped in to independently assess and report on the Estonian Cyber attack the massive waves of cyber attacks which have hit estonia's websites are a security issue which concerns NATO therefore ladies and gentlemen cyberspace must be protected just as we protect Land Air and sea thank you barely a year later during the European summer of 2008 the Republic of Georgia a pro-western neighbor to Russia fell victim to a series of cyber attacks the disabled government websites crippled Banks Communications and transport companies Cyber attack created an informational vacuum allowing Russia to control the war narrative and smoothing the pathway for their invading forces [Music] by 2009 NATO along with academics and international lawyers had composed the Talon manual an academic study on how international law applies to cyber conflicts and cyber warfare NATO has actually stood up a cyber warfare Center of Excellence also in Estonia thinking about how do you counter hybrid Warfare in cyberspace generally speaking an attack on a state entity that involves or could involve loss of life or Serious injury or could involve damage to a major State asset could potentially be considered an act of War [Music] as though from out of The Ether cyber warfare can come from an enemy state or a lone Rogue actor [Music] evaluating the impact of an attack is one thing but determining who is behind the attack and why they attacked then informs an appropriate level of proportional response one of the biggest conundrums of cyber warfare response is attribution determining who is responsible and where a Cyber attack came from can be like trying to retrieve a needle in space and retaliation on the wrong target could be calamitous it's an incredibly difficult technical problem because it is difficult to disambiguate what is the actual origin of a particular attack what we don't know in all of this is those cyber hubs and where they're based some are based in the no end jurisdictions like southeast Asia or Eastern Europe we don't know the proxies behind those people yes there can be that person in the basement that's just having a go and having a crack but we don't know whether they've been enabled by a state or they just learned themselves or there is a proxy in the middle there for someone else in a hands-off environment it's also a very difficult geopolitical problem because even in well-defined and well-studied attacks often attribution is not even stated explicitly cyber attacks leave no spent Munitions no military equipment no dog tags to identify dead soldiers we are now in a period where non-state actors can deliver devastating blows to the economy of the most powerful countries in the world self-recruited ad hoc networks that aren't beholden to any state that are sort of free-floating and willing to do their own thing in the service of a particular ideology we don't we necessarily that's equivalent to like a cyber DNA where you can identify a piece of information that's going to directly link to a particular state or a particular individual the attribution dilemma complicates the cyber warfare landscape and nullifies traditional ideas of deterrent strategies but States will still look to navigate the digital Minefield of cyberspace and enact their strategies to overcome any opposition in 2018 in response to the need for states to attribute cyber attacks the U. S and its allies launched persistent engagement at the Cyber deterrence initiative and under both those policies the United States and its allies have agreed to First attribute attacks to the countries undertaking them and warn them at the same time that if those attacks continue There Will Be retaliation either in cyberspace or outside cyberspace the United States in its 2015 law of War manual has said that it's okay to respond to a Cyber attack with a kinetic response as long as the kinetic response is proportional and necessary that's okay there's a recent example that suggests they believe the opposite is true as well so you could respond to a kinetic high power attack with a Cyber attack thank you in June of 2019 in the Strait of Hormuz off the coast of Iran an American drawn a broad area maritized surveillance demonstrator rq4 Global Hawk was shot down by Iran it was probably intentional as I said but regardless they targeted something without a person in it so we want to be proportionate U. S responded to this kinetic attack by launching a Cyber attack we've since learned through media reporting and some government leaks that the United States responded to the Drne being shot down with cyber attacks against Iran and they seem to have taken out missile launches and also to have targeted the databases of sumeranian government agencies Iran claimed the Drne violated their airspace the Americans argued the Drne was in international airspace [Music] assuming that the Drne was an international airspace that would probably give the United States the right to respond and if that's the case this is probably an example of what proportionality looks like when it comes to cyber attacks I think because the United States seems to have been taking out the capabilities Iran had used to conduct the original attack and arguably I think it shows restraint on the part of the United States and seems to have been part of an overall strategy to de-escalate things in the street of Hormuz so to use operations that fall short of conventional definitions of Armed Force [Music] operations that fall short of these conventional definitions of armed attack blur the lines between wartime and peacetime and take full advantage of the attribution dilemma such operations are conducted in the gray Zone not fully sacred not fully covert or clandestine but certainly not overt sort of Surfing With The the edge of detectability in that liminal maneuver space [Music] The Gray Zone non-geographic borderless outside of any real jurisdiction highly exploitable by adversaries where the very definition of Confrontation can be contested there is many definitions as you've got fingers and toes that's how people are seeing Gray Zone at the moment you're seeing once again the rise of influence operations political Warfare information Warfare these things are at the heart and soul of what are currently considered Gray Zone operations so in terms of where things go from here I would think that you would see States operating in the gray Zone and taking advantage of legal uncertainty because it allows them to conduct effective operations until the costs of that approach outweigh the benefits and it's not just legal uncertainties that Gray Zone operations take advantage of they also exploit the difficult ethical and political choices surrounding escalation of a crisis into a full-blown War some of the examples that we talked about before Russian interference in the 2016 American presidential elections stuxnet under existing definitions they fall short of the use of force or an armed attack but I think they highlight that there's a lot you can achieve in terms of preventing a state from conducting its Internal Affairs and that in and of itself is an important part of sovereignty and it's an important right in international law so you can prevent or obstruct a state from doing that without resorting to violence or using an armed attack and if the walls of the peace War Paradigm have been broken down the potential to win a war without firing a single shot is an incredibly desirable outcome to many states cyber warfare can balance the scales of traditional military power placing power back into the hands of the underdog it has incentivized countries that were once considered not particularly cyber literate to rush toward enhancing their own cyber capability many of the countries that you might think are not particularly significant military threats are actually quickly becoming cyber superpowers you don't need a huge amount of resource to generate very significant capability North Korea is a great example it's put a lot of effort into cyber warfare the Chinese have very capable cyber troops that were stood up in the early 21st century in response to their lessons learned from watching us in the period since the Cold War what we're seeing is that boundary between peacetime and wartime is evaporating we've seen the fact that new Cyber military capabilities and information Warfare capabilities have opened up a new space of political conflict between countries like China and the United States between Russia and the United States cyber capabilities have opened up a new Arena of conflict below the level of armed conflict Revelations that have come out in September 2019 about a Cyber attack on Australia by China Russian interference in the United States presidential elections in 2016.










![Vigilante Hacker Outsmarts Cyber Mafia [4K] | Web Warriors | Spark](https://img.youtube.com/vi/Db4MBkX6Rtw/maxresdefault.jpg)