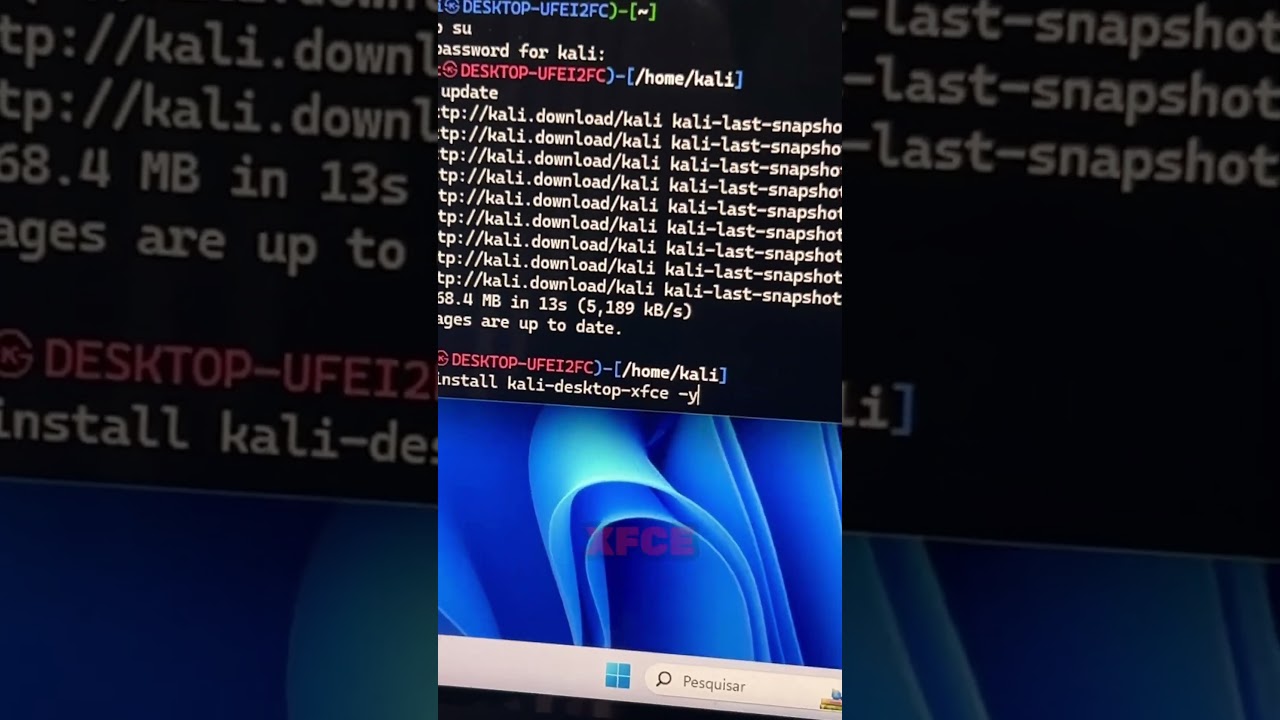
e meninos bem vindos mas um vídeo que o canal caveira tech meu nome guilherme nesse vídeo nós vamos fazer então é pedida onde sql injection o manual na mão na munheca né porque assim há por que fazer com ravij é coisa de lama que eu sei o que é que quer aprender a fazer na mão bom pessoal calma lá não é bem assim nenhum hacker nenhum faz sql injection na mão a não ser que seja um caso especial que lhes mostrar aquilo pra alguém ou em algum caso que alguma ferramenta não está funcionando aí ele vai desenvolver né alguma ferramenta alguma automação para fazer isso porque porque o sql injection quando é feito na mão é porque ele cai no canal caso mais simples é que o um beijo ou no máximo um erro bes de sql injection e aí o cara consegue fazer na mão fora isso tem que ser feito uma ferramenta né porque são centenas muitas vezes milhares de requisições que você precisa fazer para conseguir capturar o banco de dados e aí você precisa automatizar isso né então tem que ser feito uma ferramenta não tem jeito você pode saber tudo como foi total no final você vai ter que desenvolver uma ferramenta e é por isso que existe o sql mapa por isso que existe um abismo existem muitas ferramentas de automação é um processo trabalhoso na maioria dos casos com blends querem jackson é um time b de baianas que ele injete também é e você precisa de ferramentas para auxiliar nisso um caso simples com esse caso que eu vou mostrar agora que a união beijo você pode tranquilamente fazer manual né mas é nestes casos qualquer outra ferramenta básica vai conseguir fazer porque não tem nenhum então é importante você saber fazer manualmente porém você nunca vai conseguir se livrar das ferramentas né então todo jeito desde que você saiba fazer manualmente você não vai conseguir se livrar das ferramentas é falsear mas então o que quer ser um carro de verdade tal hoje se você quiser dominar né você precisa dar muito mais a fundo você precisa entender como é que é feito na união beida e rubezhni time b o time inglês the blind sql injection o band sql injection também em comum então você precisa entender é pelo menos esses quatro tipos principais aí de sql injection entender como eles são feitos como que é feito dentro da ferramenta é do sql map uma grande fonte de estudos pode ser o sql máquina já que ele é 11 já que ele é open source e você consegue dentro do sql mapa é entender como isso funciona né e aí que a partir daí caso você utiliza uma ferramenta não deu certo e mesmo que você perceba que existe uma possibilidade sql injection você vai conseguir fazer otani ou se vai conseguir fazer ali é algumas modificações manuais em algumas modificações que vão direcionar a conseguir fazer que eles querem gente naquele local é principalmente protegido por um órfão web application firewall ou tiver algumas limitações que as ferramentas muitas vezes não perceber né mas a inteligência humana assim vai perceber e você vai conseguir contornar tudo isso né é pra isso você precisa ter conhecimento de que fazer o sl injection na mão né mas tudo tem que ter um começo então vamos começar aqui do básico que é e união beast sql injection né mas gostaria de um recadinho se você quiser se profissionalizar em segurança da informação que conheci meus cursos aqui na soja só de ponto com ponto br barra treinamento ontem alguns cursos aqui profissionais em segurança da informação em hacking que o ministro baratinhos nos cursos mais completas e baratos do brasil na área são realmente muito barato sai pra quê piso para que qualquer um pudesse fazer né e ao mesmo tempo o curso me possibilitam trazer essas vídeo aulas aqui pra vocês né mais freqüentemente e aí vamos lá pra aula né tanto que no no site que teste php com ponta coletivos pontocom né pegar a mão da crítica pontocom e search é um site fornecido pelo politics primeiro se você tá vendo a solo não sabe nem quer se querem gente não pode parar por aqui voltar às aulas anteriores né então vou deixar a lista é um playlist e das aulas sobre neutralidade é para você aprender que o sql injection que é um banco de dados como funciona o sql injection o centro só vai poder ver a solo que depois com centers e background e se assim esse esses conhecimentos prévios se não você não vai conseguir entender muita coisa né tá beleza tão bom aqui no site aí tem diversos diversas vulnerabilidades colocadas propositalmente aqui pouco netflix e vamos procurar que o sql injection tão tenha se quebrou os categories né tem q posters porque imposters aqui aqui em cima eu já vi que tem uma passagem parâmetro aqui pela por el qat maps para muito quente aqui né ele está passando um tão thales estão nos produtos de categoria 1 que só os posters né se eu posso aqui o 2 ele ainda está os produtos de categoria dois sons penitentes nexon as pinturas aqui né se eu passar o 3d mostra nada provavelmente só tem essas duas categorias mesmo né não vou falar por 1 a 1 e se eu passar o máximo simples aqui em vez do número um da um enter ele vai dar um erro de sintax sql ou seja é ele o o site não conseguiu entender o comando sql que era pra ser passada por o banco né eo banco respondeu com erro né e esse erro foi mostrado pra gente aqui eu vou ter uma ptax mais kelly serve próximo às 3 aspa sakineh se você colocar aqui além só aqui pode vir um porcentagem 27 onde coloco mapas é alguns jogadores nem vai depender e vamos transformar isso em um hexa desse mal né então isso é o equivalente hexa pra aspas simples se eu passar um espaço ea pode ver que vai preencher também ontem um porcentagem 20 né então se o equivalente prática simples é porcentagem 27% e o equivalente para espaço a porcentagem 20 alguns caracteres aqui sendo que se não for em letras e números deixa eu ver aqui é o coisa não foi transformando né se não for letrada número muitas vezes ele é transformar este formato é o url em cold nem o paex à de simão então o que pode ver que ele parecia que ó né então o que a gente percebe que a gente consegue injetar comandos sql né então já está caracterizado aí uma vulnerabilidade sql injection a gente colocar aqui um novamente para funcionar a beleza ea primeira coisa que a gente precisa fazer num sql injection pelo menos no union beijo é tentar descobrir quantas colunas é existe nessa tabela dos das categorias aí né então como a gente pode fazer isso a gente pode usar o orbe order bike que significa que a gente quer ordenar essas informações estão sendo mostradas aqui né os quatros posters aqui ó por uma determinada como uma casa com uma informação nem tão uma coluna pode ser o nome da coluna pode ser é o pintor outro problema pode ser a data pico não pode ser a url da imagem outra coluna pode ser lá a descrição daquela pintura né então se em cada comuna vai ter uma informação diferente sobre essa pintura então a gente pode ordenar que é ordenado em ascendente ou descendente na ordem alfabética ou o contrário disso né então você pode ordenar pelas informações né então no poder há pouco não order bairro né pode ver que ele substituiu o que faz os espaços por porcentagem de 20% vinte por cento e vinte e aqui eu ordenei pela coluna não ele me mostrou que beleza eu posso nem falar o cordeiro pela coluna 2 deu certo dentro pela coluna 3 eu posso fazer isso até encontrar o número de colunas nem eu tenho que fazer um grupo forte aqui né por tentar 14 567 pode ver que toda vez vai mudando a ordem que os corpos aparecem porque ordenando uma coluna diferente que cada como não tem a mínima idéia enquanto né 8 9 e 10 e 11 e 12 então isso pode ser chato às vezes você já entendeu porque é utilizada a ferramenta porque muitas vezes você tem que ficar fazendo isso 12345 isso aí dependendo as querem gente é fazer isso milhares e milhares e milhares de vezes é realmente é por isso que existem as ferramentas né e quando eu coloquei 12 colunas ele deu erro no colo ou seja como um desconhecido o número 12 não quer dizer que não tem 12 colunas tem 11 aqui embaixo ele já deu um outro um outro erro que ó mesmo erro só que aqui embaixo ele conseguiu mostrar uma informação pode ser importante né open test que é o caminho completo na aplicação que é o bairro hj barra bárbada barra deste produto ponto php por isso aqui pode ser que você utiliza no futuro do seu pet então isso é uma informação a ser guardada em duas colunas outra maneira também de gente descobre que tem tem contas colunas tem utilizando e unión select não posso em colocar se uniam select ou seja eu vou unir a primeira consulta é fazer o que deixou escrever todos não fica confuso e união select é assim vou falar só se pega primeira consulta aqui na categoria 1 o único uma outra consulta consulta posso escrever porém essa kessy que ele tem que ter o número primeiro o mesmo número de colunas que essa primeira consulta que foi buscar na categoria 1 então se eu falasse união select e um neto selecionando e juntando com seu poder se á a com a qualquer coisa e entra que ele vai dar lá ó é é o select esteticamente chefe é diferente op colonos ou seja é eu tô indo duas duas kers select porém elas têm números diferentes de colunas então tem que igualar esses números como nos pra não dá erro né então ainda não tem um jeito a gente descobrir quantos colunas tem né então basta eu vim colocar aqui mais colunas né tipo bebê cecê vírgula é tão que por exemplo três com um nome com três colunas e deu errado né então vou fazer de um jeito mais fácil é com números em vez de com strings 11 2 3 4 5 6 7 8 9 10 11 e 12 com 11 o acerto é uma uma consulta uma coluna mais aqui né uma informação a mais um quadro mais né se eu tirar esse união select só categoria 1 ó ele vai até o 31 uma união ele passa do 3 e ter uma informação mais porque une né isso daqui então pareceu que como uma informação a mais pode ver que apareceu com os números a que apareceu o primeiro set o número dois o número 9 né então daqui são as informações que conseguiu puxá lá de dentro da minha consulta né o 123456789 não posso ir no lugar dos 7 por exemplo escrever alguma coisa por exemplo oi pessoal e pareceu que foi pessoal se eu quiser assumir com as todas as informações que estão originalmente eu posso ficar aqui no lugar de um aqui colocar ao menos um né aí ele vai descartar essa primeira dessa primeira esse primeiro select e vai mostrar somente apenas 11 segundos eléctrica 1 2 3 4 5 6 7 8 9 10 11 né beleza ela mostrou né sumiu todo o resto ficou só essa parte aqui ou seja aqui ó a gente consegue está vendo que ele está mostrando aqui pela aplicação mesmo tudo que a gente quiser ele pode mostrar que nós às vezes se fizer umas consultas maliciosas de dentro do banco ele vai começar nem foi mostrar a informação sigilosa aqui do site mesmo né eu vou conseguir ficar pegando pequenos vão conseguir pegar essas informações de dentro do do banco e ele vai mostrar que mesmo na página né é esquecer o tipo de gadget mais fácil porque ele vai mostrar que directamente não é pra mim né através dele vai imprimir na tela pra mim né existem muitos sql injection que ele não imprime né ser feito através de erros né e acerto então a gente faz uma consulta que se der certo beleza gente descobriu que ele está certo se der errado vai dar um erro a gente fala mal não é isso a gente tem que chutar outra coisa né então vai ser chutes e acertos né então vai dar bem mais trabalho nesse caso a gente não precisa ficar faltando a gente pode roubar informações direto do banco de dados e mandar lhe perguntar aqui na tela e aí lugar do set eu já vi que eu posso escrever mais coisas do mesmo coisa que eu poderia escrever um lugar 29 simplesmente escolheu 7 que está aqui em cima delas culinaire preferência que até 11 ele apareceu hoje em simon 11/11/11 poderia te pegar outro por cima também porém é vamos fazer pelo set mesmo vai deixar 11 aqui e aqui eu vou colocar o set o que eu percebi que eu já posso pegar algumas informações então tem algumas funções dentro do mais quero eu posso usar aqui no lugar do set eu conseguir roubar algumas informações desse banco por exemplo a versão do passat version lá e vai mostrar que a gente está trabalhando com mais química a gente já sabia nem quero mais que ele para os erros ea versão é 5. 1 1. 73 né é que a gente vê também que ele está usando uma versão compilada por o ubuntu 10.
04 netão que a gente descobre qual é a versão mais kelly ea versão do sistema operacional ubuntu 10. 04 tamanha tim e aí é gente é pode pegar outras coisas que por exemplo se eu colocar aqui uma função chamada rouba rouba da tarde a pasta onde estão armazenados os bancos neto mais kelly nem é em formato de arquivos no sistema de arquivos do linux está aqui no bar barra de barra mais quente se eu colocar aqui por exemplo um vai mostrar o usuário a corte arroba local host uma conexão local e o nome de usuário ea corte se eu colocar que da tam bém se descobrir qual é o nome desse banco de dados é a corte então pronto pessoal a gente conseguiu pegar várias e várias informações descobrimos com o nome do banco é a corte e descobrimos que é a versão descobrimos também que o usuário tamanhão a corte está rodando localmente o nome do banco é importante para a gente pode descobrir de outras maneiras né aí a gente pode colar tentar pegar informações de dentro de si desse banco é de dentro de desse banco mas que jeito bom toda a instalação de mais kelly possui alguns bancos bancos do sistema do sistema do mais quer ontem o banco mais kelly tem um banco information o esquema são dois bons que vem por padrão né é e nos bancos mais novos mas que ele tem uma performance esquema né alguns não tenham mudam mudam um pouco esse padrão não vai depender da versão por isso que você souber versão saber se uma coisa boa né você consegue filtrar mais com mais mais informações cada versão de banco né cada tipo de banco mas que ora como vai ser se tiver um ataque de sql injection um pouco diferente né então é importante você conseguir identificar qual é qual é o banco está sendo utilizado ele qual dbms né que a gente fala então a gente pode tentar pegar informações dentro do information o esquema que um banco o padrão é do mais kelly vanessa information esquema e traz uma série de informações de todos os bancos é daquele daquele sistema pra deixar o o sistema mais quer ele organiza o sistema mais quer é de excluir uma performance melhor tal ele que organiza tudo lhe então tem tudo lá dentro de si informei esquema o nome de todas as tabelas nome de todas as de todas as colunas etc de lá a gente vai conseguir pegar o nome das tabelas dos bancos das colunas e aí pegar as informações de dentro dessas colunas né vamos lá pegar o nome do dos dos bancos dentro do information esquema então a gente pode vim aqui é o lugar dos 7 a gente vai querer o esquema name esquema nem me né aí depois do 11 que eu faço from a gente vai querer saber se o esquema nem de onde de dentro da information o esquema esquema ponto na tabela esquema mata e beleza pode ver que ele mostrou busco dos entrada sakineh ou seja tem dois bancos de dados no sistema informático o esquema ea corte aliás podem haver mais de dois mil candidatos nesse sistema porém nosso usuário que o usuário a corte só tendo acesso a esses dois né dentro de um fermento esquema ele só dá acesso a esses dois bancos né pode ser que existam outros bancos itau porém lá dentro information esquema que a gente está tendo acesso é só do accord e do information esquema a gente pode tentar pegar o nome das tabelas de dentro do corte ou seja tem tabela de usuário tem tabela de produtos tem tabela de sei lá a categoria tem tabela de artistas como vê que tem lá dentro né e aí a gente pode ver e pegar um lugar do esquema nem a gente já sabe se que ela nem a corte vai querer o table name né numa das tabelas e aí dentro da tabela formation o esquema tem uma outra tabela a chamada ons e aí a gente conseguiu pegou todos os nomes de tabela dentro da tabela tables né olha só o tanto de nome de tabela aqui só que aqui a gente pegou todas as tabelas de todos os bancos de dados a gente pode filtrar a gente pode filtrar mais informações né então a gente fala se eu não quero todos os nomes tabela só quer as tabelas que forem do banco é é a corte que é o banco que do dessa aplicação aqui é decido este site e aí a gente pode filtrar fazer o seguinte a gente coloque um é um esquema é igual à corte que é isso mesmo beleza é isso mesmo e aí o que eu consegui fazer filtrem né então peguei aquelas mesmas informações só que dessa vez eu peguei phil 3 se você não está entendendo isso aqui é porque você não sabe sql é importante você estudar o oeste quer pelo menos o básico para entender como funciona a linguagem sql você pode procurar na internet vai encontrar diversas informações sobre isso é gente filtro aqui e pegou só aos nomes de tabelas né pertencentes ao a corte então que têm os artistas carrinhos né pictures produtos e users legal a gente tem uso aqui né então é uma tabela assim que a gente vai focar o ss users né e aí pra gente só que agora a gente precisa descobrir qual os nomes das colunas dentro do users né ou seja dentro do usuário que tem nome tem senha tem nome de usuário e mail etc a gente pode escutar o nome dessas colunas porém seria mais interessante a gente descobrir quais são todas as colunas que tem lá dentro né quais são os nomes delas né ou também há muitas vezes pode ser feito ataque bruto força em causa não foi possível descobrir o nome das colunas diretamente volta sendo que aqui a gente pode descobrir mas tem casos que não dá para descobrir e você pode chutar fazer o que for sim você sabe ser parte do princípio que vai ter uma coluna chamada e usa como como é chamada pés ou pés wd o ps word você pode chutar isso né é que a gente quer pegar todas as colunas de dentro da tabela e users aí é que eu posso venho colocar o seguinte em vez de ter bom nem me quero colo nem né nem from the formation que é um ponto com londres então agora a gente vai querer a gente vai pegar todos os nomes de colunas dentro da tabela colamos do banco e formei um esquema que pegar uma que todas as colunas né só que como disse aqui são todas as colunas a gente já filtrou pelo banco à corte nesta filtrado aqui ó table esquema igual a corte porém a gente no filtro ou ainda pelo nome da da tabela é que aí usa né então a gente pode filtrar aqui o apelo ter bom nem é igual a 3 só pela tabela e usos né ele me trouxe as seguintes colunas e o name pés cc adwares e meio nem me fone e kart então ele me trouxe todos os nomes na então posso aqui no tá né o ney me és e meio nem me fone kart é importante sempre anotando o nome da tabela mandou do nome da tabela que é bela e os verdes ponto é o nome da tabela o banco do b de banco de dados a corte tem o nome do banco de dados tenham na tabela e tem o nome das colunas pronta antes de mais nada né eu com essas informações agora eu posso pegar diretamente lá dentro dessa tabela as informações então que eu pagar tudo né igual a você tudo de novo né nunca chegou ontem aparecendo aqui se eu botar o cat igual - 1 - não vai sumir né o corsa união select 1 2 3 4 5 6 7 8 9 10 11 beleza e aí lugar do sétimo lugar dos sete que eu vou querer o que vou querer o o nome de usuário name né da tabela e users users então bota que o ney me eu posso aqui from e users pronto eu consigo pegar qualquer informação de qualquer tabela né então posso pegar o nome de usuário da tabela o usuário quiser eu peguei aqui o teste após pegar a senha também aqui eu só tenho um usuário por isso que só parece um quadro em espécie mil usuários e aparece mil quadrinhos aqui né é precioso mil usuários né posso colocar o pes vai ser o teste também posso colocar o cc lá né posso colocar o fone que o fone né acho que a informação toda inventada aqui é mais que tem que pegar o name e meio não pegar onemi nem me jonny né e mail bial hoje ponto com o nosso empenho é um produto é realmente pega um pouco mais e pode concatena isso não posso fazer um com kate e juntar mais coisa posso vou juntar por exemplo nem me colocar um delimitador possam entrar assim né ou 12 pontos vamos ver alguma coisa que vai separar um do lado do outro e vírgula posso colocar aqui pés e vou colocar o e mail também em meio à beleza que ficou com os fundos country assim vou colocar aqui dois dos 22 pontos o nome do usuário teste a senha teste e meio bem arroba ge. com né o que eu posso por todas as informações que eu quiser e que seria o estado todos os usuários né cara tivesse mais um usuário poderia desde o começo vim e chutar nem falar será que existe uma tabela será que existe uma coluna paz uma tabela e users pronto e chutavam software que ele tem o trabalho ia dar certo né eu faria direto é o sql injection direto não pegar em directo os pés e os usuários né só que ficaria difícil por exemplo aqui o nome de usuário é onemi que não é algo comum é utilizado geralmente user né então provavelmente descobrirá pés mas não ia conseguir descobrir o nome de usuário isso foi importante fazer todo esse trajeto completo pra depois pegar a informação certinho lá né é isso aí pessoal tem muita coisa a ser desenvolvida aqui em cima disso muitas e aprendido em cima disso né o início é pra vocês é entender em se vocês querem se aprofundar e conhecer ainda mais sobre segurança não só sobre vulnerabilidades é finalizado é também você pode ver e fazer um dos meus cursos aqui na soling né só de ponto br barra treinamentos e curte um vídeo da um jovem aí é curta e também a página no facebook ficava facebook.