This guy is a scammer from India pretending to be with Microsoft and he is peacefully trying to steal some money. But what he doesn't know is that I'm on the other end of the phone and I'm about to open my camera right at his front door. Going to a scammer's house in real life and confronting him might require some context.
This all started when I managed to gain access to this guy's computer, meaning that I'm able to see his screen, listen to his microphone, which is always interesting. Interesting. I'm also able to follow every button of his keyboard being pressed.
And I can even look the guy that tried to scam me right in the eyes by accessing his webcam. The first thing that stands out when watching his activity for a couple of days is that he is constantly staring at personal information of American citizens and on the phone to these people trying to gain remote access to their computers. Uh can you see your desktop icons?
What? Uh okay, no need to worry. Can you see there is a icon with a name ultra viewer?
A blue icon. Can you please open it? I don't know what I'm 80 years old.
I don't understand this. I'm not sure what you're asking me. Our fraudster over here is running this scheme from a residential building.
But he is not the only person in this apartment running the spiel of pretending to be with Microsoft. It is actually a group of guys somewhere in a penthouse in India and they run a scam that I have never really seen before. When opening the microphone, it is clear that this is not just a one-man operation.
Good morning, Helen. beside John your computer technician. Let me tell your security question and answer so that you can Hello.
Hi, good morning Miss Morin. Yeah, this is Sam Thomas ma'am your computer technician. How are you?
These scammers are very cautious and scared of getting arrested by the police. We can see some translated chat messages here about them saying that Jill is not an option as that will ruin their operation. To avoid detection from police, they are working in multiple smaller groups in multiple separate apartments in different buildings nearby to each other.
We will find the exact hideout soon and pay the scammers a visit there. But first, I wanted to see what exact scam they are running and how they steal money from innocent people. And the thing that helped me discover their scam is this text file called cold pitch from daddy in which they display their script for the outbound cold calls they make to American citizens.
It all starts with them introducing themselves as Microsoft technical support. If you remember, we have worked on your computer yesterday and you pay paid us amount for the services we have offered you. This is regular feedback called to make sure that everything working fine on your computer.
Security is working fine but few of softwares we installed yesterday is not compatible with Windows. We have to initiate refund for that particular softwares right instead of this voice clone. Let's see how the actual scammers take people's money in this very unique scam.
And ma'am, uh some of the drivers which we installed along with the network firewall security in your computer, they are not compatible with your operating system. But don't worry, the security will work absolutely fine. Yesterday as I check here, you paid us $199.
So for the drivers which are not compatible, the company is going to reimburse you $120 back. Okay. Okay.
Thank you very much. You're welcome, ma'am. And within next 5 to 10 minutes, you will receive the call from the refund team manager to complete your refund process of $120.
Okay. Okay. So, let's sum up their script.
These scammers get personal information from people that have already been scammed the day before by tech support scammers. Our group of scammers then say that they need to see if all the securities that the victim paid for are working on their device. The conclusion is always that the securities are not completely compatible with their computer.
And because it is, the victim is going to receive a part of their money back, a refund from a refund manager. The low-level agent script stops here. But once the victim gets on the phone to this refund manager, that person will play up the traditional refund scam where they give the victim a fake refund with too much money by accident and they now need to send that overpayment back to the scammers.
Sir, at this stage, we we need your help. We need your cooperation and your helping hand. All right.
I keep it for myself. You got to understand one thing. Uh it's better.
It's better you do one thing. I'm afraid this conversation is over. You don't.
Sorry. I I can hear like your wife is like laughing from behind. Okay.
I will put the dick I will put my dick in her mouth. Okay. I will put my dick over her mouth, [ __ ] That is how things could go if someone doesn't want to cooperate with a refund manager.
But that call was old and unrelated. I don't have access to the refund manager of this campaign quite yet. The notes of the guy I do have access to clearly show that he doesn't go any further than just cold calls and transferring the victim over to the refund manager for the real scam.
This guy is an opener and not a closer. The notes also show that not everyone is willing to cooperate with the cold calls as we can read things like customer said you are not Microsoft. I don't trust you guys.
Don't call me again. Customer abused and hung up the call. and you are scammers don't call me.
The average amount of cold calls per day in these nodes is about two or three. And all this guy ends up doing is remoting into the victim's computer plus transferring the call. His shift is usually about 10 hours long.
So with only three calls per day, most of the time I see him chatting to his wife on WhatsApp or video calling her to see his kids, video calling friends, watching Netflix, and a whole load of burping. Yeah. H, how charming.
So, how will I watch them scam people if I only have access to this opener? Well, I guess I will have to use some hacking magic to get access to the closers of this operation. But before I do so, I can already get a summary of the scam based on pictures being sent around in their group chat.
It starts with a Microsoft refund form, then a fake error message. Oh my god, we have sent too much money. $75,000 of our money is now in your account.
Give that back by buying gift cards, cryptocurrency, or sending a wire transfer to a totally legitimate location in some obscure third world country. The result is people's entire bank account balances being wiped. Most people unfortunately realize that too late.
This message is for Mike Butler. Please call. Hello, Mike.
I would appreciate if you could call me and I want my money back. Bye. This is for Mike.
Have fun with what you did. You better call me. I want my money.
I'm calling the police. I want my money back. I'm taking every step to get it back, [ __ ] Wow.
Anyways, I did manage to perform some hacking magic and pivot my access to the computer of a refund manager. The first thing that I found on his device was an ID card picture of a victim and tons of credit card information, too. Since these guys work together with tech support scammers to buy victim information and scam them a second time, it wouldn't surprise me if they go on to sell this credit card data as well to another third party of scammers to drain even more funds.
On this one scam computer alone, I already found the data of over 12,000 people. Scammers sell and abuse personal data, but they're not the only ones. Data leaks are also common with huge companies.
See here, for example, a data breach from Bank of America that was kept silent for months. Luckily, I have a long-running partnership with the sponsor of today's video, Aura, that offer an amazing product to protect your information from ever getting in the hands of the wrong people. Aura will alert you if they find your phone number, email, or social security number in any data leak, including information shared on the dark web.
On average, it takes a company almost 300 days to report a breach of information. Meaning that your information could be floating around on shady marketplaces right now without your knowledge. And trust me, you do not want to give these criminals a 9-month head start, which is why Aura is so important.
They will let you know fast if your information was found or is being misused. And worst case scenario, they cover you with up to $5 million in identity theft insurance. This, along with a bunch of other online safety features, is available on aura.
com/scambbator, where you can try Aura 14 days for free and see if your information is currently being exposed. Let Aura do the work for you by going to my special link in description, or aura. com/scambbather, to try 2 weeks for free.
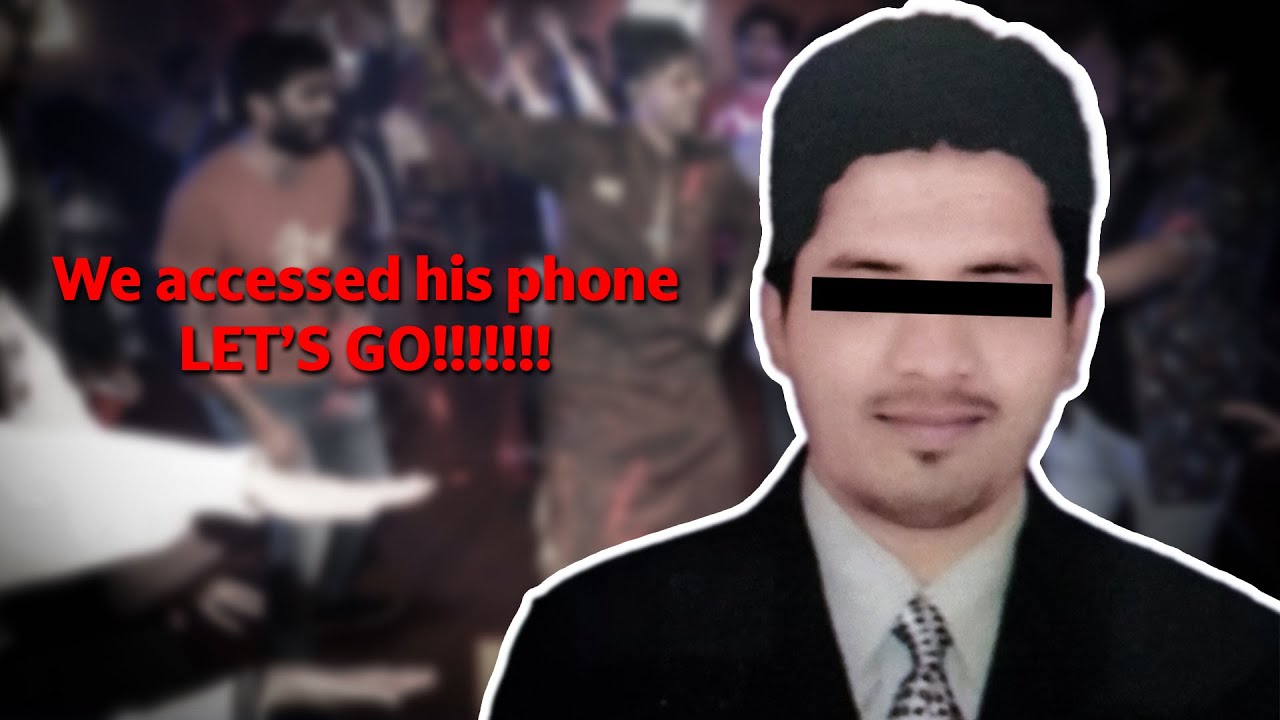
Anyways, I was just talking about getting access to the computer of a closer. I found out that this guy's name is Rajender. This is what he looks like.
He has a webcam through which I can see him too. But the calls are made from his phone, not the computer. And he has been smart enough to strip away all audio devices from his machine.
So I have been unable to capture him actually scamming people. As explained before, the scam itself is nothing crazy. It's the typical overpayment refund scam with some Oscar worthy acting that would probably go something like the following.
Now give a click on submit, sir. now request you to submit the form and you will see the transaction has been processed and you will see the amount how much you got in your end. Okay, that says 14,990.
What? Are you serious? Just hold on, Mr Martin.
Let me check it. Just hold on. It says server error 404 and it says a refund transaction of 14,990.
Oh my god. Oh Jesus Christ. Oh my god.
Sir. Oh Jesus. While you were filling up the form, I was a person who was helping you out.
Right now it's a totally it's a matter of my job. The extra money sir which you are going to get in your account you have to help me out to get that extra money back to the account. You have to help me sir because it's a matter of my job and I'm the only person working for my family.
Okay. The victims of our group of scammers that cooperate and listen to the refund manager will end up selling all their money to India for the scammers to take. Well, actually, the way that these guys launder and receive their stolen funds would probably mean that the victim's money is going to China.
Pretty much any method that these guys used to steal money is through a middleman. And all of these middlemen are Chinese people that work in call centers specializing in money laundering. Hi, friend.
This is a cash pick of $23,000. Look, this is the root cash picture. [Music] Yeah, the driver is prepared.
If you need it, please connect to me. Shout out to my friend Merwin for obtaining that video. His channel will be in the description.
He even managed to get one of these Chinese scammers to show their office to him on a video call. Hello. Hello, bro.
Hello. Nice to meet you. Hello.
Look at Hello. Hello. Our group of scammers also work with these Chinese people to launder stolen funds.
But the scam itself is being ran from apartment buildings in Gurug, India. As seen before, one of the scammers in those apartments is this opener. He provided a lot of information and also has a webcam which gave me more of a visual insight into their scam campaign.
He loves to call himself Sam Thomas, but his actual name is Hassin. Not so smart to leave your health insurance card on the same device from which you steal a bunch of money. He also provided me his high school results from 2006, showing he is 35 years old, but more importantly showing that he scored below 50 out of 100 on all his courses except for drawing.
No wonder he became a scammer. All the other files were pretty much just hundreds if not thousands of people he has called and potentially scammed in recent years. Besides his files, I also managed to access his bank accounts from which I could see that some of the money was deposited to him by a company named A3 Infoch.
And I recognized that name because I had seen it before in file names, notes, WhatsApp chats, and the name of their phone system. A3 Infoch is actually one of three companies that run these sorts of virus alert pop-ups. They scam people with the tech support scam and then sell their victims over to Hassen's group for the refund scam.
From the files, notes, payments, and WhatsApp chats. It is clear that the three tech support merchants providing leads to Hassen's group are A3 Info Techch, Cap or Capital, and Info, also known as InfoGen. I wanted to make sure that Hassin and his buddies put an end to this thievery.
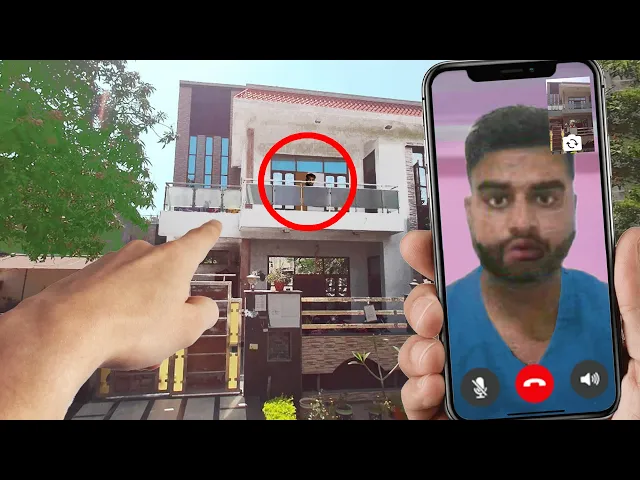
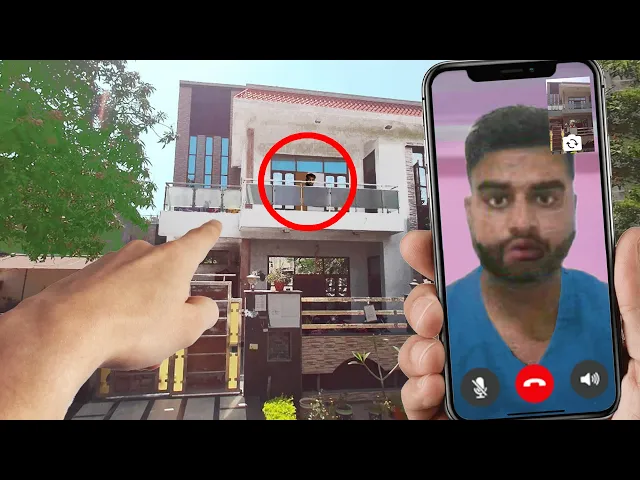
And what better way to scare them off by paying a visit to their exact location in real life. To do this, I need their location. From the IP address, we can see a general location somewhere near New Delhi.
But since he's using a laptop, I can just collect all the Wi-Fi points around Hen's device and get his exact location based on Wi-Fi signal strengths. This leads me to a luxurious residential township located in sector 103 in the west of Gurugram by the name of India Bull's Centrum Park. This township has 15 towers.
But if we draw a circle on the coordinates of 16. 3 m wide, we can see that only one building is left, tower number one. It just so happens that the scene revealed in his chat logs that he is in the penthouse of G1, aka tower 1.
I sent somebody local to the scammers to go and film the G1 tower. so that I can confront his scene with his own location. And not just confront him, I have created a fake phone app that he will see once he connects to me.
And I will make him believe that I'm right outside his scamming hideout. Let's give him a call, pretend to be one of the victims on his list, and scare the living yes out of him. Thanks for calling support and decide.
How may I help you? Yes. Hi, this is Peter.
I I had a missed call from you about my computer. Yeah, I was trying to call you uh because yesterday we work on the computer and I just need to complete my pending work. Are you available right now?
Yes, I am available. Yes, and that is the name is ultra viewer right? Yes, I see that one.
The password is 6459. Okay, give me moment. All right, Hassin, how are you doing, buddy?
I know you're in India, Bull Centrum Park, Tower G1, apartment four. Okay, I'm currently outside of your building. So, I want you to speak to me, okay?
Otherwise, I'm coming upstairs with the police. You can see my phone. Can you see your building?
Tower G1. Hassin, can you speak to me? Hassin, can you speak to me?
I'm right outside of your building. Okay, you just seen my phone. I'm here with the police.
Okay, so just talk to me. Otherwise, you're getting arrested. I know.
He immediately covered the webcam as soon as he saw the the phone. Let me call him. He's going to shut down.
He's shutting down. He has his finger on the wait. I didn't even say anything and he immediately covered the webcam.
He he recognized the building like first second he connected. The person you're calling is unavailable. Come on, pick up your WhatsApp, buddy.
Let's have a little chat. Yeah, you can come downstairs. I'm downstairs.
At least that's what you think. This guy must be so scared right now. This guy is not picking up.
He's packing his bags, mate. He's getting ready to escape through the fire the fire exit. He's picking an Uber XL right now.
He's not going to pick up his phone. Wait, I just tried to call him. Can't place call because this number is not registered on WhatsApp.
He already got rid of his phone number. He shut down his phone. Wait, let me call this other number.
Number you have dialed is currently busy or not reachable at this time. The number you have called is unreachable or busy. That is crazy.
After this, Hine never came back online. I hope you guys enjoyed this video. If you did, make sure to like and subscribe before clicking off.
If you want to buy me a coffee, I have a PayPal and Patreon link in description. I hope you guys have a nice day. Stay safe, stay cautious.
Bye-bye.