it's important for you to know that all Network information flows through switches and routers including such things as authentication information and data attackers can use a variety of switch attack methods to gather valuable information that they can use later to exploit the network in this lesson we'll go over the following attack methods Mac flooding ARP spoofing VLAN hopping STP manipulation double tagging and Max spoofing in regard to layer 2 switches remember layer 2 switches understand ethernet frames at the OSI data link layer the first attack to examine is Mac flooding switches maintain Mac address tables
sometimes called content Access Memory tables or Cam tables to track workstations and ports associations switches learn which workstation is connected to each port and that information is stored in the MAC address table and used when switches forward information for example let's say that workstation a wants to send information to work station D the frame has a source address ending in A's and the destination address is the address ending with D's when a sends the information the switch examines the destination address and sends the data out Port one to its destination workstations B and C aren't
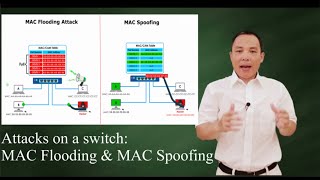
involved so they never see the information suppose an attacker wants to see all data passing through this switch considering that a switch's normal operation only sends data to the intended recipient the the attacker would only be able to see data destined for his or her workstation which is very unlikely but the attacker can flood the switch with fake Mac address information and fill up the MAC address table once the switch can no longer store any more mac addresses the switch enters a fail open mode and behaves the same as a network Hub or layer one
device this means that any packet coming in now goes out to all switch ports the next switch attack is called ARP spoofing also known as ARP poisoning but let's first talk about address resolution protocol or ARP which works similarly to DNS DNS resolves a fully qualified domain name into an IP address while ARP Associates a device's MAC address with the IP address assigned to that same device to Aid in this process a switch creates and stores an ARP table in memory for easy lookup knowing this an attacker sends commands to the switch to overwrite the
contents of its ARP table by replacing a good and known Mac address in the table with the MAC address of the attacker's device this is the ARP spoofing or ARP poisoning as a result data that was intended for the legitimate device is now sent to the attackers device in many cases the attacker captures the data and sends it on to its rightful owner this is known as an onpath attack another attack method you should know about is VLAN hopping since each VLAN is its own Network a device on one VLAN can't communicate with a device
on another VLAN without a router there are a couple of techniques attackers can use to take advantage of this VLAN separation the first is VLAN spoofing VLAN spoofing takes advantage of a switch that's using its default settings which allows for dynamic trunk negotiation depending on the switch this default setting is known as Dynamic Auto or dynamic desirable this means that if you have a switch connected to the original switch the ports connecting the two are automatically configured as a trunk connection a trunk connection allows data from one switch to pass to another a spoofing attack
takes advantage of this by fooling the switch into thinking the attacker is connected using a trunk line although there are several ways to carry out a spoofing attack such as adding a new Switch we'll look at how someone could accomplish a spoofing attack with just one switch our switch here is configured with two vlans VLAN 10 and VLAN 20 with both having several computers connected to it our attacker a disgruntled employee is connected to VLAN 10 and wants to steal sensitive information from the company's chief executive officer but as mentioned VLAN 10 is a separate
network from VLAN 20 so as is the attacker can't access the CEO's computer by using a tool like Yia our disgruntled employee can send the switch a packet that tells the switch the port he or she is using is really connected to another network switch this is done using a dynamic trunking protocol frame or dtp frame since the switch is configured to Auto negotiate for a trunk line it assumes the attacker really is a switch and opens his or her Port as a trunk line with the attacker's port now configured this way he or she
can easily capture packets from the CEO's computer keep in mind that the best way to protect your network from this type of attack is to disable the switch's auto negotiation setting for all ports except those to which an authorized switch is attached another method attackers use is called double tagging this VLAN hopping technique is used when the attacker's computer is on one VLAN switch and the target computer is on a VLAN attached to a separate switch in addition the switches must be configured to use what's called native vlans when a packet is sent to a
switch it includes what's known as a VLAN tag this Tag's purpose is to indicate which switch should process the frame for example you'll notice that both users are on VLAN 10 if user a wants to send data to user B the frame would include the VLAN tag indicating that the frame was intended for VLAN 10 when the data reaches the switch the VLAN tag is removed and the packet is sent to its rightful destination double tagging is accomplished by manipulating the frame being sent to include two VLAN tags so one for VLAN 10 and one
for switch 2 or VLAN 20 when this type of frame is received by VLAN 10 switch the first VLAN tag is removed but seeing that the second VLAN tag is referencing VLAN 20 the frame is forwarded to that switch then as it normally would this switch strips off the second VLAN tag and sends the frame to the victim's VLAN successfully hopping from one VLAN to another to prevent double tagging it's important to make sure that your switches aren't configured to use native vlans this is because trunk ports configured with a native VLAN won't apply their
own VLAN tag when sending these frames which lets the attacker's tagged frames to continue as I just described another common switch attack is known as a spanning tree protocol or STP manipulation attack STP is normally configured on a network with several switches the primary purpose is to prevent switching Loops often whether intentional or not there are several paths data can take to get from its source to its destination STP dynamically turns off certain switch ports to ensure that data can't get stuck hopping from switch to switch without ever reaching its intended target while STP configuration
is beyond the scope of this lesson it's important to understand that a single switch is designed as the root Bridge the root bridge is an optimized data path's primary source this is necessary because some switches often connect to other switches to form redundant connections to ensure Communications continue even if a switch or Port fails the root bridge is used to pass data from switch to switch since all switches that participate in the tree know where the root bridge is located so the root bridge is responsible for calculating the spanning tree from topology changes advertised by
non-root Bridges if an attacker can become the root Bridge he or she is then able to see a variety of frames that they normally wouldn't see to perpetrate this attack the attacker inserts their switch into the tree and manipulates it to a point his or her switch as the root bridge by doing this he or she can use a sniffer to collect data traversing the network an attacker accomplishes this manipulation by sending Bridge ID frames or B ID frames with a lower ID than that currently being used by the legitimate root Bridge there are several
steps you can take to mitigate this type of attack first make sure that attackers can't easily guess which Bridge ID number is being used by the legitimate root Bridge most switches have a default root Bridge ID ensuring that your Bridge ID is considerably lower than the default one if your switch supports it a second option is to set up Bridge protocol data units guard or bpdu guard this feature allows an interface to put itself into blocking State when it receives a bpdu packet meant to change the root Bridge switch your third option is to enable
root guard on the ports not being used as trunk lines this keeps ports in their assigned roles if one of these ports receives a bpdu frame a error is logged and that Port is blocked thwarting the attacker's attempt to change the root Bridge the last common switch attack to discuss is known as Mac spoofing Mac spoofing is the process of sending out data from a computer using a MAC address that's different from the MAC address physically hardcoded on a network interface card or Nick although you can't physically change your Mac address there are tools like
Windows Network and Sharing Center and control panel smack for Windows and others that can make an operating system believe that the Nick has a different Mac address there are several reasons attackers may use this method to attack a network such as to defeat switch Port security for example in some networks part of a switches security is the creation of an allowed list of Mac addresses only devices with a Mac address in the allow list can be processed through that switch if an attacker can use a network sniffer to find a MAC address that's being used
by a legitimate host attached to the switch he or she can change their Mac address to a valid one on the allow list then they've successfully gained access to the switch and any data being transmitted through it that's it for this lesson in this lesson We examined several methods attackers utilize to exploit switch configuration weaknesses such as the ones shown here with each of these attacks one of the primary goals is to collect information that can be used to exploit vulnerabilities at a later time