all right so welcome everyone this is the home lab for Splunk sore Phantom it's going to be fun because we are going to learn about what is sore what is plunk sore and how to set up in our own home lab environment this video will be divided into two part in the first half we will learn about uh different capabilities of sore spun sore what is sore basically and what are some practical use cases and what are the prerequisite to set up the home lab next part we will actually practically deploy it I'll show you
what are the steps require to set up the home lab for Splunk s yourself all right so without taking much time let's get started so in this video we are going to learn about four things first what is sore second what are the capabilities of Splunk Phantom SAR next practical use cases of Splunk s and then home Lab First what is s but before we even talk about it let's understand why do we need it okay what problem it it basically solves so you you see uh you know as per uh as per a lot
of research and reports as well security analyst in the sock envirment spend around 70% or 60% of their time just in triage activity just in the initial uh false positive related activity and they they keep spending their time on more and more recurring stuff that could be avoided that's where sore add of value okay the full form of sore is security orchestration Automation and response okay this is entirely a single product remember now orchestration the purpose of orchestration is to orchestrate all the different tools in the network because you see in the cyber security uh
organization uh large Enterprises might be having multiple security tool right multiple tools and these all tools are Silo in nature that means one tool is from one vendor another tool from Cisco another from Paulo Alto another from Azure anything right so all different tools have their different uh format or way of communicating maybe in terms of logs uh the way they they they generate the log alerts and everything right so sore basically has a capability of understanding that format and can perform the orchestration among them okay next is the automation automation plays a very very
important role in terms of you know Bringing Down the number of repetitive task the manual activity done by the sock analyst for example sock analyst spend time in uh identifying the false positive identifying the real threats looking at maybe fishing uh fishing you know email identifying if it's really a fishing email or maybe a false positive so maybe manually going into the actual domain name or URL trying to perform the lookup to get the IP address looking at this reputation on virus total and everything or maybe looking at the maybe if there's any file in
the email so verifying the file hash if it is malicious or not so all those things is done in the automation I mean manually done but SAR can do it itself through the automation next is response now response is about incident response so when this happen what action need to be done so it's trigger and response if this happen this is the entire set of process you have to follow maybe isolating the end point if the ransomware occur if there's a Dos what action or what firewall rules should be created based on source and destination
IP address everything that that's all part of response you see this actually solves a lot of time lot of valuable time for a sock team and at the end as a as a value sock team can actually then work on something which is more relevant which is more worth solving okay now let's talk about the Splunk s Splunk Phantom uh capability okay Splunk has multiple uh ways of Splunk Phantom has their own jar of managing sore capability first is the app app is like you know just just the way Splunk Sim has multiple apps to
perform the integration so this plays a very important role in the orchestration because you see multiple different kind of a platform or security tools might be having their own app maybe Paulo Alto will be having its own app maybe uh Windows def Microsoft Defender crowd strike will be having its own app so that solves the problem of orchestration The Silo behavior of the security space you can also have app editor where you can customize the default Behavior you can also have Playbook now this is the entire this is the heart of sore because this is
how you actually create the automation so Playbook is sort of automating the security and it actions based on trigger and response so you can create a playbooks basically execute a sequence of action based on your tools based in seconds probably an hour as well by it has most of the security tools or the sore platform provide pre-built uh you know playbooks even Splunk Phantom also has got 100 plus I think 200 plus pre-built uh inant uh playbooks for example ransomware Playbook if you see any end points with this specific malware or ransomware family so these
are the the steps you have to take it for example you can inform the inpo EDR to re isolate the machine you can add the IP address in the reputation in The Blacklist you can inform the team in the slack or maybe on the Microsoft teams and then maybe you know you you can then guide the team about what action to be done uh so similar to that there are multiple playbooks can be created so you don't have to manually work on each and every activity you got it so this is Playbook then we have
case management option as well which is like creating tickets and you know keeping track of every activity event management is all about incident types of incident you receive so this is all being handled by the Splunk Phantom next is practical use cases what are some practical use cases with sore or Splunk Phantom first very important one is of course automated and incident response process for example as I said earlier if you identify any fishing suspicious email flag them flag flagged it as the uh potential fishing email so you can search uh search for the copies
of these email throughout the network and delete or quarantine them by itself block the source IP address or the URL that might prevent the malicious email from reaching to employee inbox so this this in this way our spun sore can integrate with Solutions like proof point or minecast or Microsoft solutions to perform those actions right uh so this is pretty much possible next we have another capability is threat hunting now threat hunting this is more of reactive threat hunting right so if this happen so these are the action you could take you can actually look
at if the the system has been compromised or this looks suspicious then it can actually take the hash of the file it can actually take the hash of a sample of the file and then you can perform a lookup in the entire network if the similar hash file exist in any of the other machine in the network then it can give us the report and then we can take a decision then we can create an incident automatically and inform to the you know team dfir team or sock analyst level two team in the Microsoft teams
or maybe in the uh slack as well so this is all can be done in the reactive basis okay priority priority for uh PR pen testing test as well so you see uh penetration testing is a manual stuff but we can help in uh we we can use sort platform to prioritize the pen testing how basically uh you can actually prioritize uh you can actually assign a value to every asset secure uh security scans and based on that CVSs score then you can actually create a new report and you know what CV what vulnerabilities uh
should we really work first on right so threat classification prioritizing a different task into the network this can all be done through the soul vulnerability management is of course a very very powerful uh spun swur can be integrated with multiple vulnerability scanning to like enable quales and with that the moment you add a new device into the network by platforms like info blocks or maybe any maybe in the active directory itself the moment a new device has been onboarded or system has been onboarded or any new asset has been onboarded the it can the S
can actually uh talk to or send a request to our teable as a part of Playbook okay so in the Playbook itself we can create a Playbook saying that a new asset has been added that will be our trigger new action would be to send a request to tenable or maybe qual is to perform a scanning of this machine so we can get a pro proactive vulnerability scanning and then we can prioritize our activity accordingly all right so this is practical these are some of the Practical use cases finally to set up the home lab
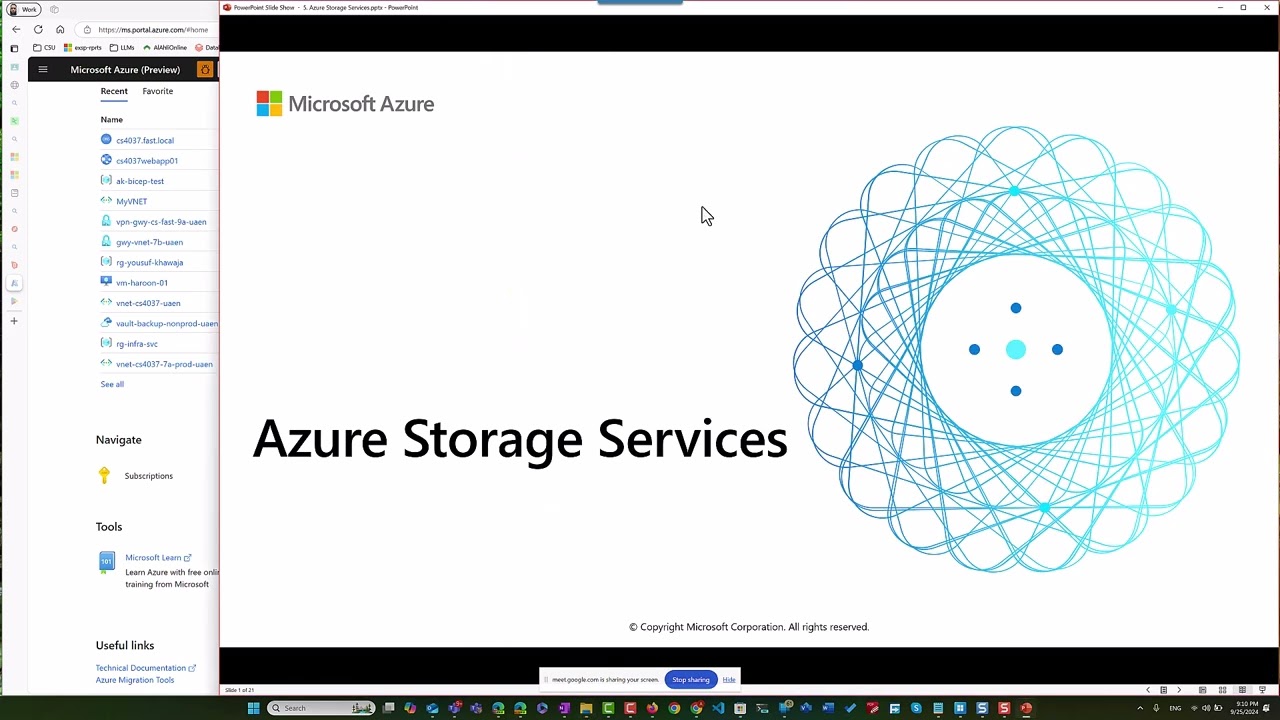
you need Santo version 7.0 I personally recommend you go visit their official website it and download the iOS image you can turn up the machine on the VMware or VMware Workstation or maybe on Virtual box all right so this is the entire idea about Splunk Phantom in the next uh the next part we will go through the home lab all right so let's get started with the home lab setup on your right you can see a GitHub page I created this guub page for spun s Phantom home lab setup uh I've created multiple steps in
it and um first thing first if you look at the step one it's just clearing out any you know uh cleaning the system sentos and then we have to update the uh packages okay so that's what you have to do update the packages I've already done it and then next step is step two is to download the Phantom package you can visit spun store create your trial account and under the download option you can find uh two options you can get it uh Splunk for sent eight and seven I personally find seven is more stable
you can go and uh download that um I prefer you use the W gate command so click on the Wate command and you will get the Wate link I've copied the link and pasted it here this is the Wate command you get it so once you get that just paste it here and the package will be downloaded you see this the package will be downloaded here and the next once it's downloaded you can see the package here okay once it's been downloaded you have to extract the package by tar minus XZ VF okay this way
you extract the package and then you you know you save it in the opt uh Phantom uh folder usually if you don't have it uh that's a requirement by this plunk okay installation itself you have to keep all the you have to keep all the packages in the op directory only otherwise uh this will not work so if I go to the opt uh you can see the Phantom package somewhere over here um where it is yeah Phantom you see this so this is where I have stored all the files okay can you see this
so this is where I have stored all the file after we extract the packages once it is done then you can prepare the installation uh by using unprivileged user installation okay uh this way you actually create an unprivileged user who don't have all the permission uh for accessing the network um and then give me one second yeah and then the it will ask you couple of questions so the moment you perform the pre-installation like uh so you see this file sore prepare system right sore prepare system the moment you hit enter uh it will ask
you first question which is install prerequisite uh RPM package required you just have to say yes I've written everything one by one uh gluster then it will you can skip this then next question this will ask is configure this plun sour of course you have to say yes enable the ntp uh ntp uh Services say yes create a an a non-privileged user this is where you have to create a new user okay I've created a new user myself so the moment it will ask you this question you have to create a new username and a
password for it okay once it is done then you it will ask you the last question about system resource limit say yes and the pre-installation process will be complete finally when the pre-installation process is done then you can perform the final installation process by executing this file sore install file the moment you do that it will perform the entire installation and it would be done it will not ask you any further question on it okay um it's all easygoing installation you don't have to worry about quite a lot of stuff once it is done you
can access the uh Source system on the local IP address or maybe the remote uh IP by using the uh you know the system IP address or maybe by using the Local Host IP address as well okay I can what I can do is I can run https 127.0.0.1 the default port for uh sore is 8443 and uh this should ask me username and password okay because I I've already logged in so it didn't ask me but if you are logging in for the first time it will ask you a username and password the default
username is it's written here you see this SAR local admin this is the default username and the default password is password the moment you enter this this will ask you to change the password okay and this is the prompt you get it usually let me maximize it a bit yeah this is the prompt you get it it will ask you to change and update the process and it will help you complete the entire uh onboarding process and once you complete the onboarding this will ask you this is the dashboard you get it and then next
you can go to the API Source indicator cases Playbook all the apps in the app sections then you can actually integrate different apps for from Splunk from different EDR service now everything to together uh the first thing that I would personally recommend is to integrate the spun Sim first you can get the app from the marketplace and then you can integrate more about it and probably in uh uh you know future videos if you want me to take it ahead to the next level and you know integrate other tools as well write it down in
the comment section below I'll make sure I'll come up with a new video in the same series all right thank you so much for watching the [Music]