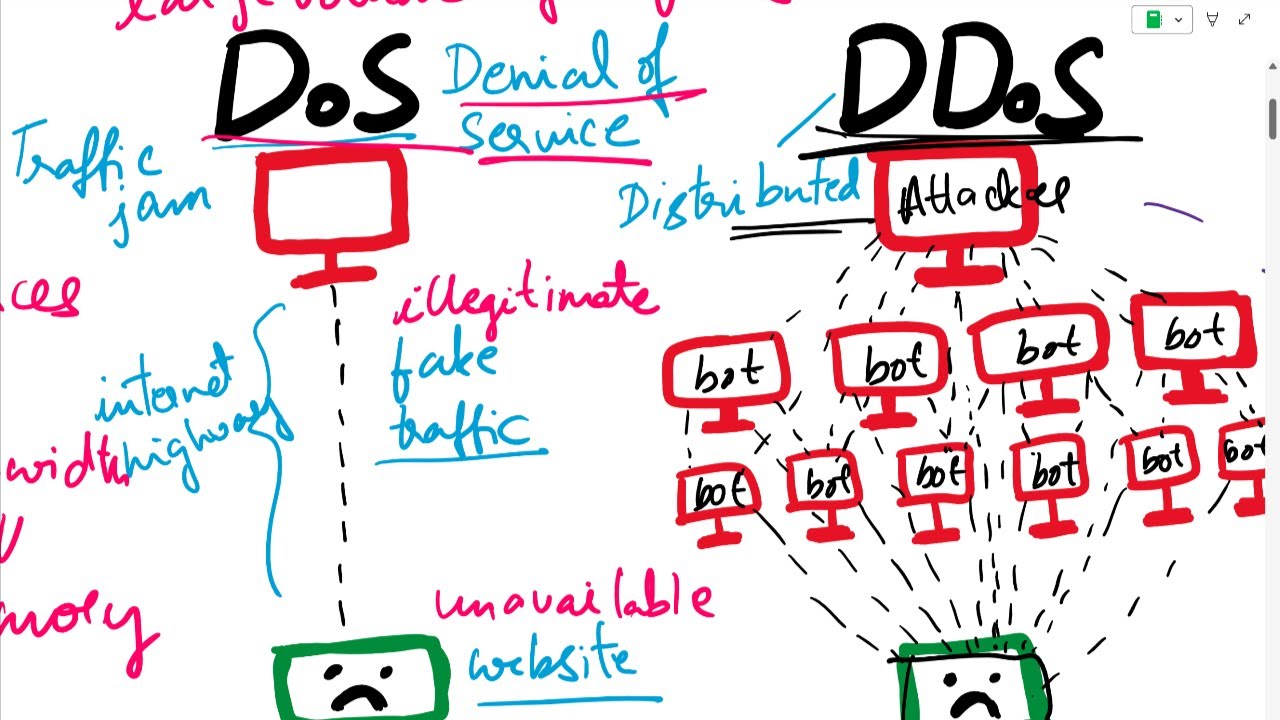
your systems are up in smoke or at least it seems like that nothing is working the CPU is a hundred percent and you don't know why you can't get anything done well what's happened is you've been dosed that's a denial of service attack in a previous video I talked about the CIA Triad in particular one of those aspects was this business of availability a Dos attack or denial of service is an attack on the availability of the system let's drill into that in a little bit more detail and find out what could be well it
turns out not all dos attacks are the same most people tend to think about one particular type which I will talk about toward the end but in fact there are different classes of denial of service attacks so the first one I'm going to talk about is sort of I'll refer to it as a ninja attack it's a surgical strike it's a Magic Bullet whatever analogy you'd like to use but it's a very targeted strike and in this case what we do is we have a particular system here that's operational and the bad guy comes along
and sends a specially crafted message so he's taken advantage of some rule that he's going to violate in the protocol or he's using a buffer overflow which is he's allocating he's sending more information than was expected in the particular buffer where it was going to be received in some way this packet has been specially configured and specially manufactured so that when it is sent to the Target system the target system Goes Up in Smoke it's one strike and the system is down that's a type of denial of service that not a lot of people think
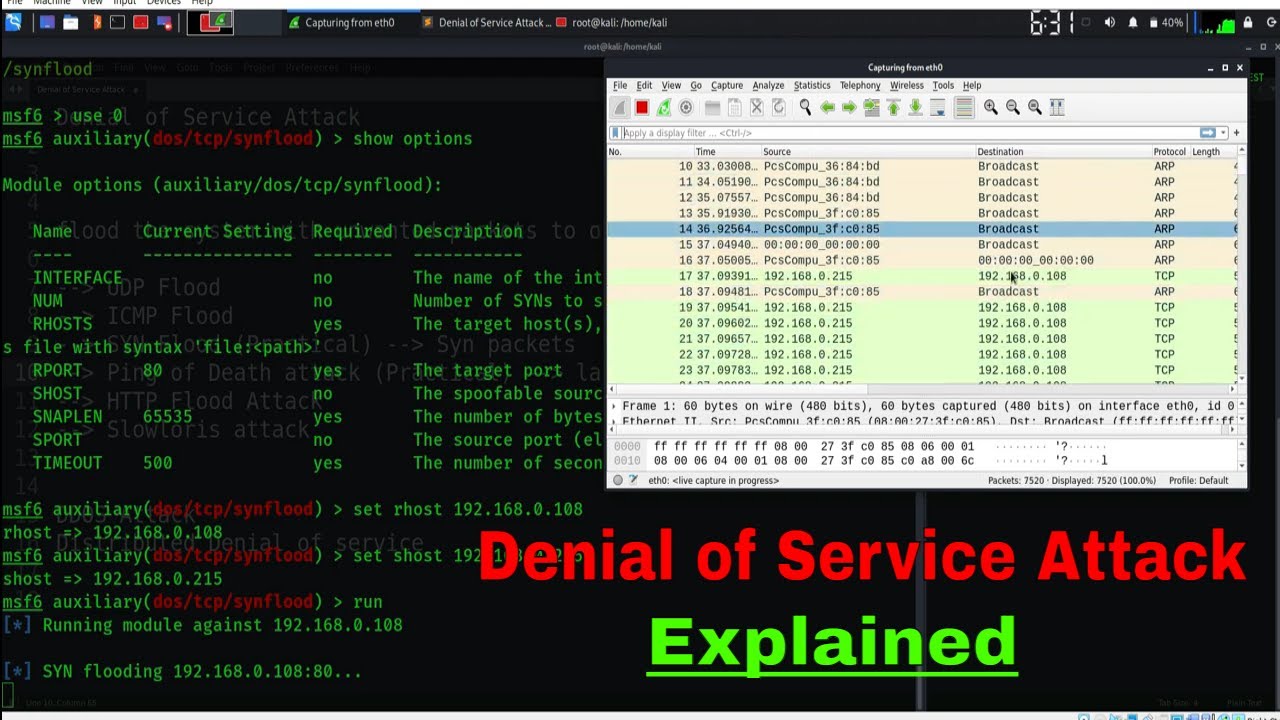
about they generally think about overwhelming with more volume and we'll talk about that that's the next type I'll refer to which is what I'll call the death by a Thousand Cuts type of attack in these attacks and there's a number of different types that can happen here but for instance if here is our system that's operational I'll give you an example of an attack that dates back to about 1996 which was one of the early versions of this kind of attack and it's called a synack or a sin flood what happens is a bad guy
wants to take over this system so what he's going to do is start by sending a packet what's called a sin in TCP terminology this is starting what is a three-way handshake to begin a session he sends the sin message and what's supposed to happen in a normal case is he puts in his address so that the server responds with what's known as a sin act a sin acknowledgment but in fact what he does instead of having it come back to him he sends the sin acknowledgment to someplace else he fakes out an address and
says don't send it to me send it to someplace else so he's lying about who he is now in the meantime what happens is this system starts a timer and it allocates some resources for this new session that it's starting and it waits now on an acknowledgment to come back from this place well this place down here is unsuspecting it doesn't know anything about this it just got a random syn act message that it's going to discard so it will never respond in the meantime this system is holding resources the bad guy sends another sin
and another sin and another sin doesn't have to send a ton of these but enough of these where it's a death by a Thousand Cuts no single one of these took the system down but collectively each one of them is reserving resources on this system until finally it's out again this was called a sin flood attack and we have fixes for this now people have have adjusted but the original TCP protocol did not take into account that someone might try to do something like this there are other versions of this type of attack things that
do reflection things that do amplification you can look up if you're interested in something called a Smurf attack which was of similar era again we have ways to defend against these things now but there are lessons to be learned as we look forward so these are two different types of Dos attacks how about the third major type of attack that a lot of people are pretty familiar with and with this one what we have is uh we start with uh this is basically a death by a Thousand Cuts times in where n is the number
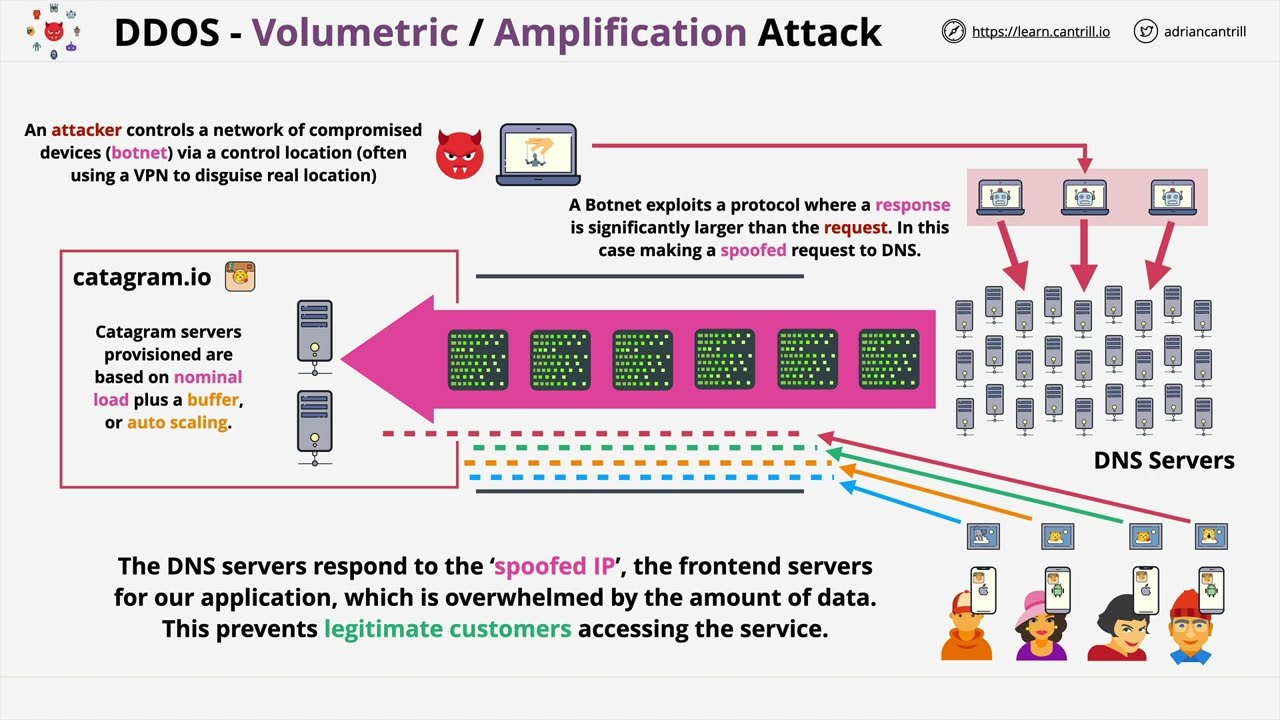
of users that are involved in the attack and in this case it's going to be unsuspecting users so we start off with one regular user who comes along and they would access a system and everything's fine in the meantime a bad guy over here though is starting to take over systems he has sent out some malware or he's hacked into a bunch of systems and he's building what is now effectively an army of unsuspecting users that he's going to later use in his attack we call this a botnet or they were called zombies at one
point but these are basically systems that are sitting here that the user has no awareness that they have latent code that could be exploited then when the bad guy wants to start his attack he sends a message out to all of the systems in his bot Army and then they all start bombarding this system with traffic until it is way too much for anyone to deal with this is what's called a distributed denial of service attack a DDOS attack it's distributed in that unlike these the attack was in one coming from one place in this
case this guy is just sending the command to start the attack but the attack is really emanating from a lot of different places so that's why we call it a DDOS attack and there are botnet armies that sit out there right now today that can be used by a bad guy all he has to do is wake them up and send them on their task for a particular Target okay that's the scope of the problem and there are many other types but that gives you a general sense what can you do about it well it
turns out there's a number of things so let's look at some defenses here first of all the number one defense for any sort of denial of service attack and I'm going to say this facetiously is infinite capacity unfortunately nobody can afford that so if you had infinitely capable systems then you could throw as much as you wanted to at them and they would be able to withstand the attack but that's too expensive what's the next best thing redundancy if you have only one system then one system is a single point of failure if you have
multiple systems if for instance in most cases we use what's referred to as a rule of three where you want to have at least three of everything so if one goes down you're not at fifty percent capacity you still have what is a usable system so redundancy is another important part to have here adds to expense but it's necessary pacing that is looking at the traffic as it's coming in and limiting how much we will accept over a specific interval of time or traffic going out which also comes to the point of filtering now in
some cases we want to filter traffic coming in from certain locations from certain IP addresses we want to be able to turn these filters on when we know we're under attack and we and it's very difficult to do that in a DDOS attack because the attack seems to be coming from everywhere we should also as responsible citizens be looking at doing egress filtering or filtering the data that's going out of our systems for instance if the ISP for this guy was looking and seeing that he was sending lots of sins that were referring to an
address that's not him they could have blocked that at the source so the right kind of filtering as the egress helps everyone if we do that kind of thing other things you could do would be Harden systems that means remove unnecessary Services remove IDs that are not needed remove capabilities that are not going to be used every one of those is something that a bad guy could ultimately exploit later so we don't want to have anything that's not absolutely necessary on the system we also want to change default passwords and user IDs if at all
possible patching is another making sure that all the systems have the latest software on them it's software fixes that took care of a lot of these earlier dos attack scenarios so there there will the vendors will continue to find ways to fix their products and we need to keep our capabilities up to that level of where those fixes are monitoring being able to look over the whole system and understand when this is happening and when it's not understand is our system really under a load because we're being Ultra successful right now maybe we just put
some new product on sale and everybody's there or is it because a bad guy has decided to try to take the system down we need to be able to understand the difference between the two so monitoring and the Technologies I've talked about in other videos the the Sim security information event management xdr extended detection and response give us that kind of monitoring capability and then finally it's incident response or also called soar security orchestration Automation and response it's the ability to once we realize we have a problem what are we going to do we need
Dynamic playbooks that guide what our responses should be so that we can respond quickly the organizations that don't have that in place are the ones that suffer the most from denial of service attacks don't be one of those victims