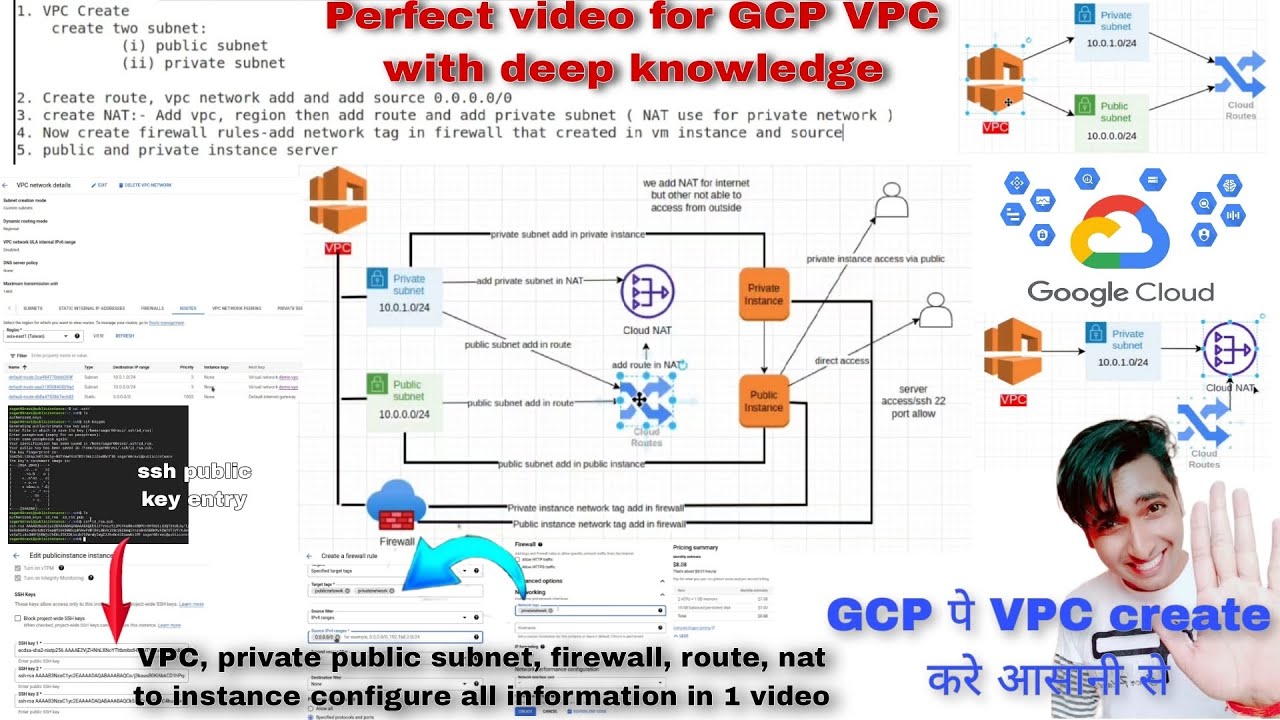
[Music] hello everyone my name is pius sajdeva welcome back to another video in the series namaste google cloud in this video i will go through the virtual private cloud in gcp how to set it up what are the subnets firewall rules and so on it is important to understand the concept before implementing it that is why i have included a presentation to give you a walkthrough of vpc edit component followed by a demo on how to set it up please watch the complete video as i will be doing some knowledge checks at the end with some sample exam questions if you are planning for associate cloud engineer certification if you are new to my channel please hit the subscribe button below and don't forget to hit the bell icon to get notified about all my upcoming videos without further ado let's get into it vpc network is a logically isolated network on google cloud platform you can think of a vpc the same way you would think of a physical network except that it is virtualized within google cloud a vpc is contained in a project which again is a part of google cloud platform each vpc network consists of one or more ip range called subnets or sub networks for instance us west one could have one subnet which is subnet one and us east one could have two subnets subnet 2 and subnet 3. subnets are regional resource and have ip addresses associated with them for example over here if you could see subnet 1 has this ip range and subnet 2 and 3 has their own ip ranges please make sure you select the ip ranges carefully if you like to know more about how to calculate ips in a subnet range and what is a subnet mask then feel free to check out the video that i published for the same i will put the link in the description section as well as in the title bar also you can use this online tool i'll put the link again in the description section and there is a utility called subnet calculator along with it so you can just put in your ip range over here let's say our subnet one's ip range which is 192 168 1. 0 and we have selected the subnet mask as slash 24 so here it is you can select any subnet mask so again this calculation how you can calculate it manually i have given in the video that i was talking about slash 24 will have 256 ip addresses you can select any other range as well and when you enter it just hit calculate so it will populate the ip range for you the first address being 192.
168. 1. 0 and the last one would be 192.
168. 1. 255.
even though it says it has 256 ip addresses but there will be few ip addresses in this range or in every cidr range that is reserved by google cloud for future purposes so please make sure you understand that as well okay so this is the way how we can check our ip range all right so we have selected the ip range of all three subnets if later on the ips get exhausted because you see each of these range that we have selected would have 256 ip addresses let's say in future at some point of time you would need more ip addresses to a particular subnet or one or more subnet you could just edit this subnet or any subnet and extend the range let's say currently it is slash 24 mask you could just edit it to have more ip addresses slash 23 subnet mask you can use or anything less than that it will give you more ip addresses just keep in mind you can only extend the ip range but you cannot delete it and you cannot shrunk the ip addresses now when you provision a compute instance you select the zone in which it must be provisioned and the region that you select for a resource determine the subnet that it can use so in this example when you provision two gce instance in zone u. s west a it determines that the region is u. s west one and this u.
s west one region has only one subnet with this ip range so these two instances will have the ip in this range let's say it could be 192 168 1. 5 for this instance and for this instance it could be 192 168 1. 12 so this is how the ipv will be selected for these two similarly when you provision instances in us east one they will be part of subnet 2 and subnet 3 and they have the ip from that cidr range that they are part of if you are confused about the difference between zone and region so just keep that in mind that zone is nothing but a collection of data centers in a geographical location and region is a collection of multiple zones that are located miles apart but why do we need region and zone separately so we deploy a workload in multiple zones and regions to attain high availability and fault tolerance so let's say we have deployed our workload in this region as well as this region let's say due to some natural disaster or anything this complete region goes down then your application will still be available through this particular region so this is how we have attained high availability and fault tolerance with deploying our workload in multiple regions so after you create a network you can create firewall rules to allow or deny traffic between resources in the network such as communication between vm instances you also use firewall rules to control what traffic leaves or enter the vpc network to and from the internet firewall rules are defined at vpc network level but you can associate it with one or more instances there are two types of rules you can create an inbound rule or an outbound rule which is also referred to as ingress or egress rules inbound as the name suggests restrict the inbound traffic on a certain port from a certain source or from the internet and the same way outbound restrict the outbound traffic on a certain port to a certain destination by default there are two implied forward rules created one which allows all outgoing connections and another that denies all incoming connection again these two rules have the lowest priority of 6 5 35 so you can easily override these rules by creating a lower priority rule let's say 65400 and this rule will be evaluated first and then this will be evaluated so let's say this rule has allowed the outgoing connections with this particular priority right and you want to deny that rule so you could just create a deny rule with this priority and this rule evaluated first and the connection will be denied this rule would not even be evaluated but you can just override these rules by creating a lower priority rules and you cannot edit or delete these rules as these are implied rules by default instances a same vpc can talk to each other with their private ip so these all instances can talk to each other using their private ip they don't have to access their public ip because they are within the same network like every instance has the connectivity with each other but you can also create a firewall rule to deny the connection let's say between the instances of subnet 2 and subnet 3.
now there is another important thing which is vpc routing vpc routing defines the network path that packets take to travel from source to destination any incoming traffic like what is the destination of it what would be the next hop how it will traverse from one location to another right and how would the outgoing traffic would go from one location to another so this all will be defined with the help of vpc routing and entries would be created in route table for the same right we will have a look at this routing in the next video where we'll be discussing about vpc pairing let's head over to the demo and see everything in action all right so let's head over to your google cloud console and search for vpc networks over here click on that and you will see there is a default vpc already created for you when you have provisioned your project and you will also see there are subnets created in each of the available region over here right so this is what a default vpc does it by default creates the subnets in all the regions that is available and they have a unique ip range you could use this vpc as well but there is a caveat to it if you have an on-prem server or if you are planning on connecting your on-prem server in the future with this particular project or if you have other vpcs or you will be creating multiple vpcs then there is a chance that these ip ranges could overlap with your other ip ranges so this default vpc and default subnet range are good for your you know learning and poc purpose but it is not recommended to run your production workload so this is the default click over here create vpc network once you do that you could just give it a name let's call it my vpc description this is not a mandatory field so you could just leave it blank as well and then if you scroll down it says subnet creation mode so there are two type of creation mode with vpc custom or automatic if you select the automatic mode then again it will do the same thing it will create subnets in each of the available regions which is what we don't want and you can choose the custom mode as well so with custom mode you could add your own subnet there is no subnet created for you so you could just click on new subnet give it a name let's call it subnet one select the region i'll select the same region us west one and us each one for the other one us west one there is the ips tag mode so subnet works in both the modes single stack or dual stack single stack it'll only have the ipv4 address range and for dual stack it'll have ipv4 and ipv6 range as well so for now i'll just select the single stack and provide the name that we have already selected 192 168 1. 0 slash 24 will have 256 ip we could additionally create secondary ip range as well done so our first subnet is there let's create second subnet subnet 2 this time i'll select the region as usfest1 i'll give the ip range as 10. 1.
0. 0 24. done and i'll create my third subnet as well region is again us west one we can create more than one subnet in a particular region one is already created by default if we are using the automatic mode but because we are using the custom mode there was no subnets created automatically so 10.
2. 0. 0.
24 all right i'll click on done right so we have specified three subnets to be created now firewall rules so there are some default ipv4 firewall rules created for you first one is the ingress rule which allows incoming connection from all the ip ranges that we have locally so these are all the private ip ranges that we have set that means all the vms within our vpc will have incoming connection between each other on all the ports again the priority is the lowest you can override this priority if you want to deny any access then second one is icmp allowed from outside the internet that means anyone over the internet could ping your instance anyone could rdp your instance if they have the keys and anyone could access to instance if they have the login credentials and then we have a vpc deny all access that means all other ports are denied other than these that have been specified because you see the rule priority is the lowest first these rules will be evaluated which has the higher priority and then these two rules will be evaluated so this will deny the axis on all other ports that have been specified so this will just deny the access on the ports that have not been specified over here and then there is a egress allow that means instances within your vpc can connect to the internet then i'll just leave these fields as default and hit on create now this will create a vpc it will take couple of minutes if you go down your vpc is getting provisioned so i'll just pause the video till it's getting created all right my vpc has been created now so you see this is the vpc and three subnets have been created with the ip ranges that i have specified if you go to my vpc it has all the details so with vpc it comes with another few components so it will have some static internal ip if we have reserved it if not you can reserve it from here this is just like elastic ip in aws we have static external ips as well in gcp so you could just reserve static internal or external ip and associate with any of your instance then we have routes over here so it has a default local route to the subnet so that the instances can communicate with each other so there'll be three routes for that and there is one route to the internet so that all the instances within our vpc can communicate to the internet and these all details will look in the later sections when we cover vpc network peering so we have firewall rules over here because we did not selected any of the default rules that is why it's not there only the implicit rules will be applied which is not visible so we could just add the rule from here add firewall rule okay let's give it a name allow ssh and the network is my vpc network that is fine this is a type of ingress rule and action should be allowed then you specify your target tags let's give it a tag let's call it dev server so this rule will be applied to all the servers that have a tag called dev server i'll show you how it will match it then it has ipv4 ranges so source ipv4 and just let's give it to everything then allowed on a particular protocol let's call it tcp port 22 so that i should be able to ssh to it and that's it just verify everything and hit create right so now you would see the firewall rules created over here if you expand this this is allow ssh rule which is an ingress rule as i've mentioned before firewall rules applied at vpc network level but you can associate it with one or more instances so now let's go to our gce compute engine and provision a gce service hit on create instance if you are not familiar with gcp i have also created a video for that so feel free to check that out i'll again put the link in the description section as well as in the title bar so let's call it svm one i use the default zone i use the small machine type something like e2 micro and then i'll go down so the rest of the section i'll just keep it default for now and the main is this one advanced option and that networking okay here you mentioned the network tag so i'll just mention dev server then you select the network interface which is the default one attached to it so you select the network myvpc this is the custom vpc that we have created and then you select the sub network now you see this is what i wanted to show you it says no sub network in this region so you don't have anything and it is grayed out you cannot select this is why because we have not created any subnet in us central one region right so this region if you remember i have told you if we select the zone it will determine the region based on that and based on that it will determine which subnet the instance should be part of but because we don't have anything in this particular jono region that is why it is giving us the error so let's just select region as us west one oregon region and zone is us west one a okay and now if you scroll down you see it auto populated the subnet one details okay so that's it you click on done and hit create all right our vm has been provisioned and if you see the internal ip this is within the range that we have selected for that particular subnet so let's click on the vm and do ssh into it it is transferring the ssh key to the vm and establishing the connection all right i am in let's clear the screen and do uh let's clear the screen and do ping on google. com i'm getting the reply from google.