foreign topics of the block Cipher the block Cipher modes of operation as usual let's start the session with the outcomes upon the completion of the session the learner will be able to outcome number one to understand the need for Block Cipher modes of operation outcome number two we will know how does the block Cipher work in real time and outcome number three we will know the various block Cipher modes of operation before knowing what all the various blocks are for modes of operation we want to understand why do we need this concept when there are
some block ciphers like this or EAS or any other block Cipher so firstly we will understand why there is a need for Block Cipher modes of operation so far we have seen two important block ciphers the days and the AES why we are calling these as block ciphers because they work on block where each input block is of 128 bits in case of AES 64 bits in case of this so we are clear that they are block ciphers say for example we want to do some encryption for our playing text if the plain text is
computed just calculate how many bytes it is if every character is taking one byte obviously we have 8 characters so 8 bytes 8 bytes means obviously 64 bits suppose we want to encrypt this particular plain text using Dash it's easy because this takes 64 bits input obviously we have 64 bits here if you want to perform the encryption for the same plank text using AES also it's not an issue because we have 64 bits here and AES takes 128 bits you can append 0 so that you can construct 128 bits of data so this is
perfectly okay think if the playing text is larger enough so when you have a lengthy message to be encrypted or when you have an image file as an input where you need to encrypt this particular image file or you may have a multimedia file to be encrypted this multimedia file may be containing an image or an audio clip or a video clip or text or animations whatever it is sometimes you need to work on the real-time data which needs to be encrypted so obviously when we have a larger text or a big playing text so
obviously we need to have modes of operation it's not simply the block Cipher is doing the complete encryption in real time in real time we need the modes of operation where these modes of operations are working on the Block ciphers like this or AES or other block ciphers we have now understood what is the need for having modes of operation let's understand this formally as well so it's clear that we are not going to run just an encryption algorithm rather we are going to have the modes of operation so it's clear that we don't run
just a cipher a cipher means an encryption algorithm so we are not going to run only a cipher rather we are going to use a mode of operation so this mode of operation is going to be working on a block Cipher like this or Eis so we are talking about blocks Cipher so obviously we'll be having a fixed length block this uses 64-bit block as the input and output whereas AES uses 128 bit block as the input and output suppose we are inputting B bits input and obviously we'll be getting B bits output say this
takes 64 bits input and produces 64-bit output I mean 64-bit playing text is converted into 64-bit Cipher text in this whereas in AES 128-bit playing text is converted into 128 bit size vertex so obviously B bits input is converted into B bits output but the real challenge is we cannot exactly give B bits the length of the message may be lesser than b bits or B bits or greater than b bits so the situation is if the amount of the playing takes to be encrypted is greater than b bits say for example in case of
AES we know the input block size is 128 bits suppose we want to encrypt a file which is of 1 MB so 1 MB means what 1024 kilobytes so 1024 kilobytes of data have to be encrypted here we have 1024 kilobytes of data obviously which is greater than b bytes which is 128 in this case so how to handle this so we want to break the plain text into B bits in each block because that encryption algorithm is going to take B bits input for example AES takes 128 bits input here B is equal to
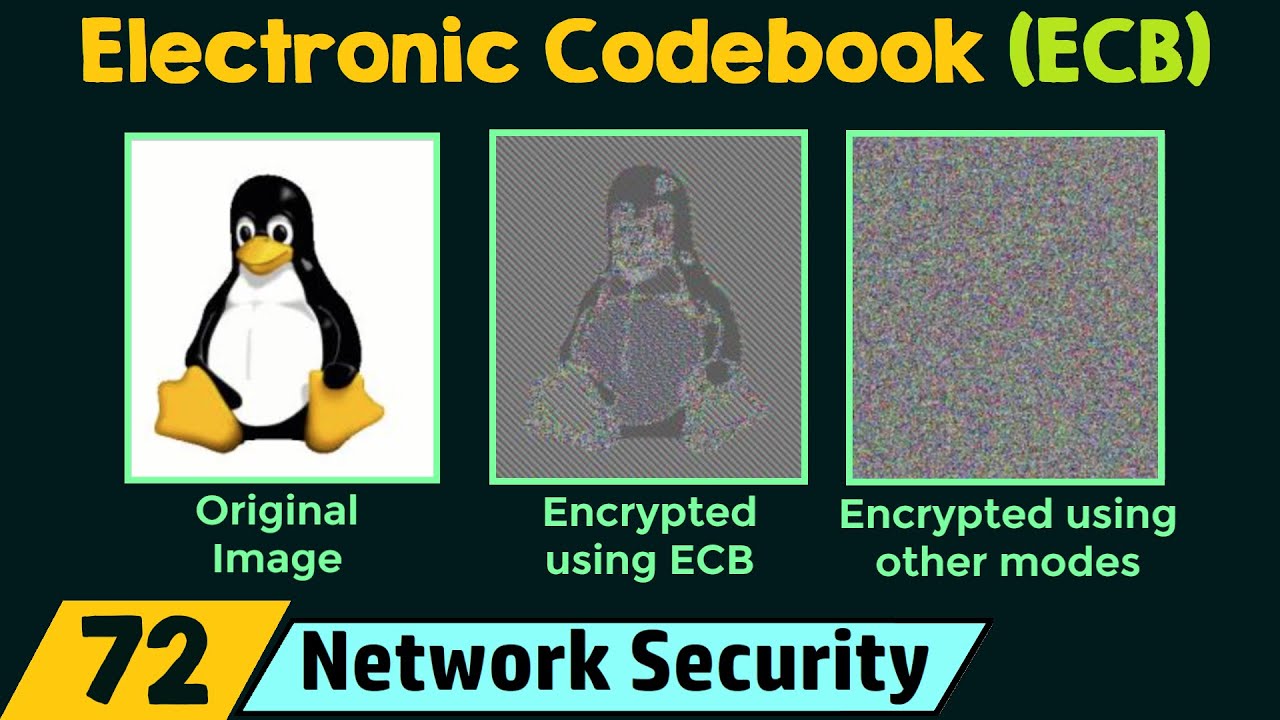
128 since we are in a need of encrypting a plain text which is greater than b bit so obviously we need modes of operation and there are five modes of operation defined by the National Institute of Standards and Technology what are they let's see that shortly so it's clear that we definitely need modes of operation at the same time we need to address this the security issue arrives when multiple blocks are encrypted yes we need to focus on this also suppose if we are breaking a plain text into multiple blocks and we are encrypting all
multiple blocks obviously we need to focus on the security concerns as well so we need to focus on these areas also anyway in the coming lectures we are going to elaborately see all the five modes of operation defined by nist at the same time can we have the same mode of operation for variety of applications certainly it is not possible we may be having different applications say WhatsApp may use a different mode of operation whereas a web application may use a different mode of operation other applications may use a different mode of operation So based
on the need the mode of operation is going to be differing we may be preferring EAS as the encryption algorithm because we trust AES which is really secure and powerful enough but the mode of operation need not be the same for all the cases so for different applications we can go for different modes of operation based on the need and based on the security aspects we are done with understanding the theoretical aspects of block Cipher modes of operation let's now know what all the various modes of operation Nest Define and basically five modes of operation
number one the electronic code book simply called as ECB number two the cipher block chaining which is called as CBC number three the cipher feedback mode which is CFB number four the output feedback mode which is ofb and finally the counter mode these are the five modes of operation defined by nist and that's it guys I hope now you understood the need for having block Cipher modes of operation we know how does the block Cipher modes of operation work in real time and we also have come to know the five block Cipher modes of operation
I hope the session is informative and thank you for watching [Applause] [Music] thank you