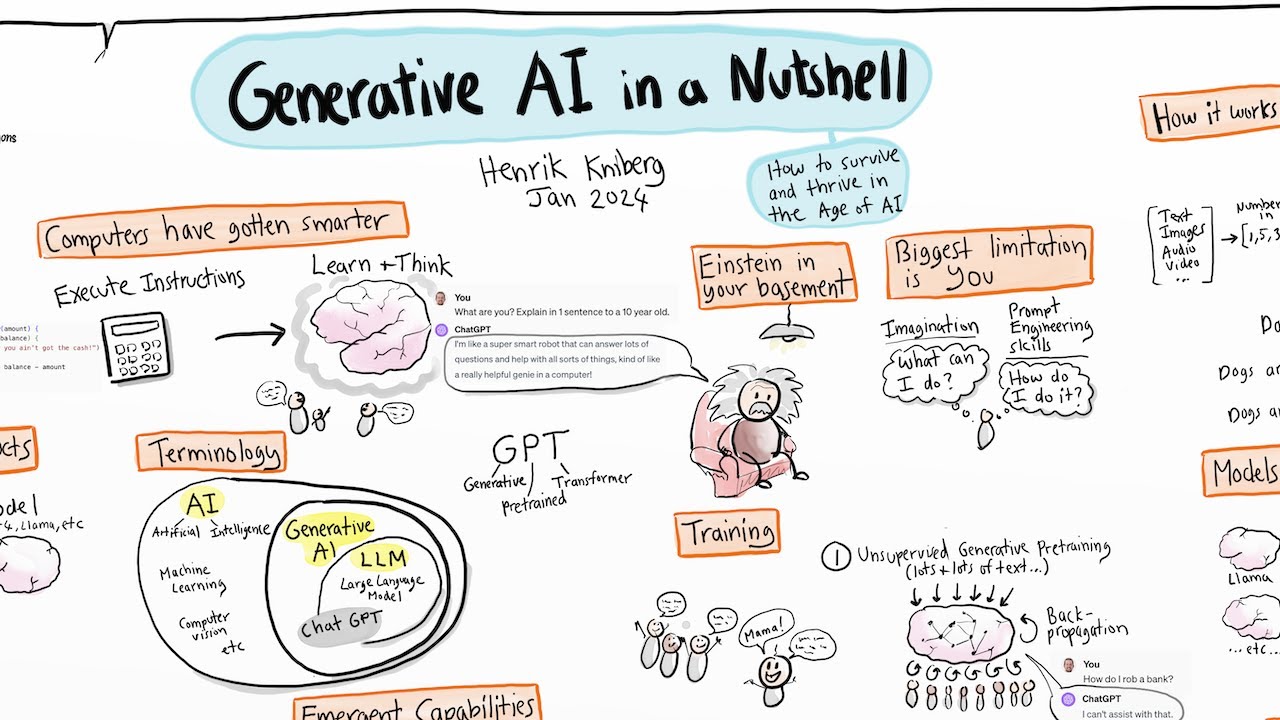
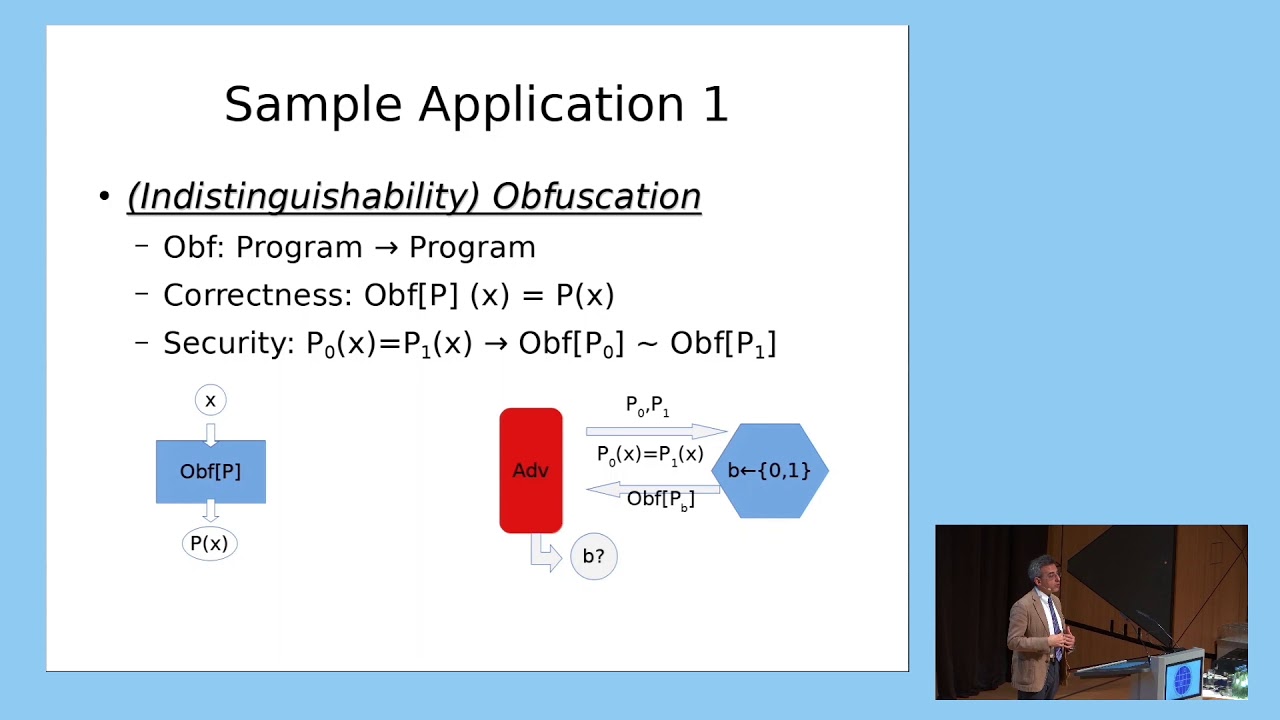
you [Music] so I'm going to give an introduction to homework encryption my job is to give you enough background for you to fill up following sessions I will mainly use the PFC scheme as example is a simpler way of explaining homework encryption you can visualize some of the things as examples and then after my talk will be after lunch we have young soos talk talking about another scheme gets into more details about how to use the home of encryption and then after that we'll be Kim's talk about you can see some real code and maybe
try to follow his typing and you can write your own examples too so that get started some of the contents are already covered by Christine I think that was like a homo encryption introduction of mathematicians perspective and here I'm trying to give you something like maybe a programmers practice perspective something as I say less math involved we've been trying many years to reduce the portion of the mass in explaining of all these schemes these methods so at the beginning so I recently got this question from the US border check actually what do you work out
what's your field I said homework encryption and apparently they say oh this horrible name is even hard to pronounce you need to explain about the basic idea about this technology to him and you can just say it's a new type of encryption and I compute an encrypted data without decryption and no one sees the result so it covers all the stages when you explain to the officer a lot of you probably are from oversea or not US citizens you might get that questions in future and and we met a lot of problem and talking to
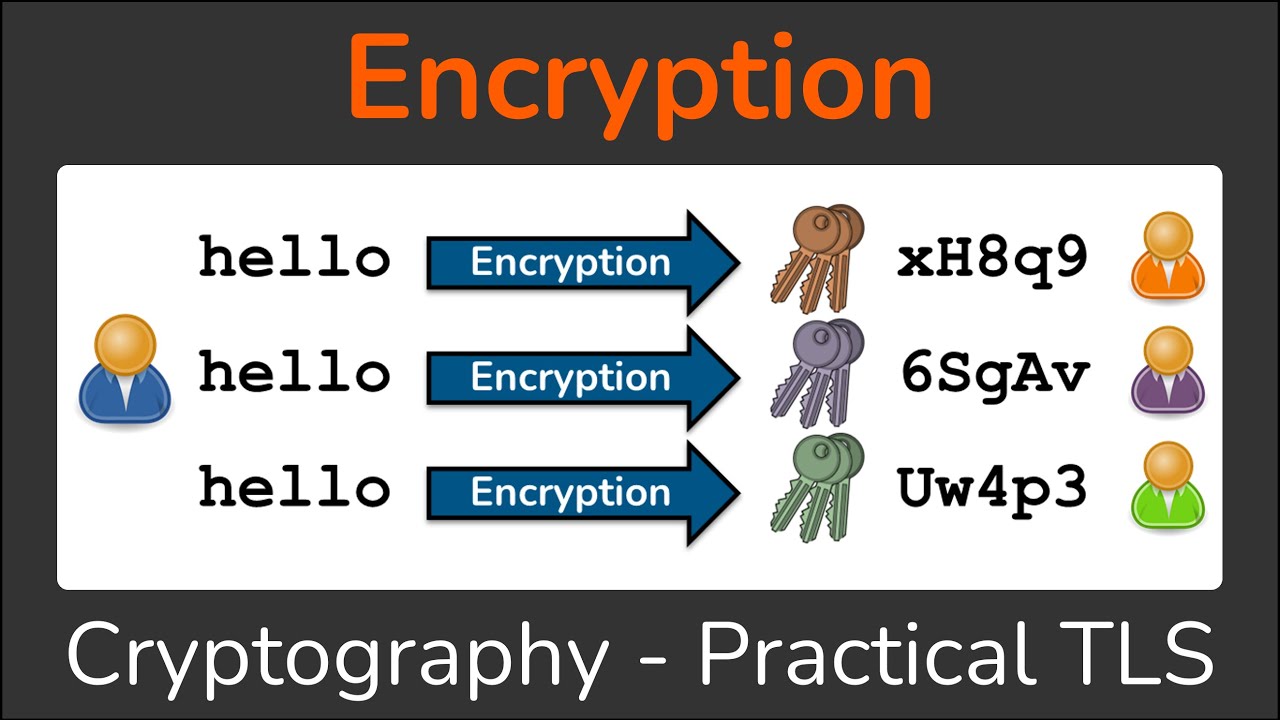
people really new to this field that they don't they cannot distinguish encryption from hashing the basic thing is just encryption you can say increases and you require the secret key to decrypt without a secure key you cannot revert it then they might go into more details I has to bother at late night so they might ask you like why people start working on these because this wasn't available until 2009 this is a fairly new field I was kind of lucky to get into this field in 2012 my advisor picked this new area and that was
just the beginning of this thing and ever since 2009 we witnessed like one order of magnitude every year kind of right now we have 10 to 9 times speed up compared to the first construction 2009 and these thanks to all the researchers and developers from company at emia and they ask you what do you work on what does all the researchers work on we brought up new constructions new schemes theoretic improvements even optimizations on the hardware targeting special hardware's and we bring the slowdown down to 10 to the 10 a 10 to 3 or 10
to 6 there's a slight different depends on how you use a sheet maybe you are you're a bad program or if you didn't understand it well then you get that 10 to the 6 times slow down sometime and final thing is the target application scenario is if she has a killing app for online secure storage and computation good examples that you want to keep your DNA data secret but you still want to use some of the services that you say find your relatives and you can just upload the encrypted version of your DNA to the
database and they provide matching those service for you and return you the result and even whether you have relative or not you get some result encrypted back only you can see the result maybe someone get empty result maybe someone get the full list of relatives they are all encrypted the service provider knows nothing about it so this is the ideal scenario and there might be some real-life application of these and for example if you want to follow the I - condition spell I da SH they focus the test on genomic data sometimes there might be
some good solutions and there are papers to follow up so here are just very frequent questions we got like say first we assume that there are two zones one is a safe zone it's on let's say when you do decryption you requires a safe environment for example your laptop that's where you hold the secret key and it's a consider safe all the data outside this safe zone should be encrypted I mean encryption doesn't have to be doesn't have to be done on your by yourself it can because there are public key encryption that use a
public key so I can do encryption for you every one of you but data outside that safe zone are always encrypted even the results and you can see even if you compute are not encrypted data and an unencrypted data the result is still encrypted it's like a it's like a virus it's once you get the encryption there everything will become encrypted and which is good and accommodations never done like you don't need a secret key to do encryption without a secure key you cannot do decryption that ensured the safety of your data and there are
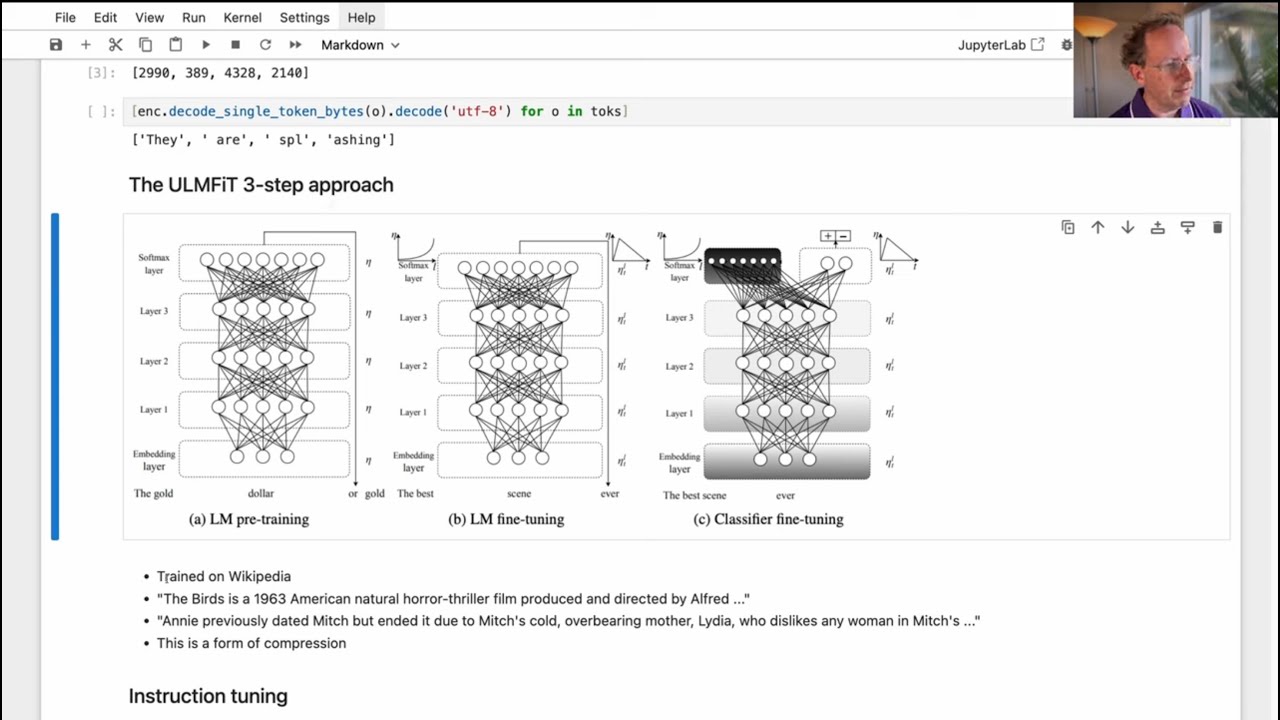
a few popular schemes these are the most efficient schemes nowadays I think some of you have worked out if she related schemes are they focused on logic gates on Petes it's like redesigning logic circuit that's one scheme and then we have B GBM bfv they perform exact arithmetic on vectors of numbers so first it's better than just a single value is perform vector of values and then it give you the exact result you don't see any error you don't see approximation city cares is a new scheme we've introduced in the next session it does approximate
arithmetic because at some time you don't want to keep the full precision if you're in banking you want to calculate the whole SS of yourself you want to get like the full precision but what if you're doing they say some floating-point arithmetic I say you are doing your training or inferencing you only need maybe a bit precision then Sica gas is a better choice is there's approximation involved Microsoft CCO implements pfv and CES and those two will be the ones we are going to focus on so there are usually five stage in HD you can
see that in every paper covering a she so the first one is to set up here I lay out everything in the in the order when it happens so first thing is to set up you need to choose the scheme you need to choose some security parameters and there are some performance parameters for functionality I actually I uploaded this slice to github so I will show you the link afterwards at lunch time so he can download or look at it in time and probably it was this will apply to all the following slides in our
top technical talks and then after we set up the parameters you can do the key generation and here this secret key is the one that you know you need to protect it and the other three are generated from the secret key and they are all considered public so you can send these three to anyone and they can never compromise your data and these three these two are required for computation this public key can be used for encryption secret key can be used for encryption and decryption and then next step is to encrypt your data so
here a high-level view we encrypted a vector of numbers I'll go into more details about what the numbers are look like but just a vector of numbers many of them and it becomes a ciphertext which is two polynomials I'll get that get to that right after this slide so we can I want to start with encryption and evaluation stage at the beginning evaluation is where you really write your program so let's say I give you a test for to do like some aggravate the algorithm using homo' encryption or they say I just give you some
similar tests like a polynomial evaluate the polynomial you can write it down with some of encryption and these all happens in evaluation and other way to say is just a computation and secure data and this is what really matters as you can see it happens on the four stage but we can get started here because it's more intuitive to define your algorithm how to write a code and at last you decrypt your data after competition is done you decrypt the result so there's getting through the encryption so I need to introduce this seam D computation
a lot of you probably know Cindy a lot of you don't a single instruction multiple data that means when you issue a single instruction or operation he applies to all the data independently scissors we cut single instruction multiple data we use that the home hormone-free encryption when you have a message for example the message is a vector of values one two three four a lot of them and there's one encoding happening here that gives you a plaintext remember the plaintext is a polynomial for example encoding of one two three four and look like these it's
a polynomial this is our plaintext I need you to remember what is message what is plaintext and what is ciphertext cipher deck is the output of the encryption so here is what security really got guaranteed before this encryption everything are just plain text like in clear state I give you the plaintext you know the decoding algorithm you can get it you don't need a key but here is very security start to matter and the cyber attacks will have a random looking I it's totally meaningless you don't see anything you don't get any for me well
me suppose you're just encoding a single number it's just become like constant polynomial this is just seven and the still the encryption give you a random looking polynomial you cannot really distinguish whether you're encrypting one message or a lot of message because you know the cyberattacks are always random looking and how do we do the contagion so you have one two three four encrypted you have another one two three four encrypted I want to do a addition the result will be the encryption of two four six eight the addition is done coefficient wise element wise
same with some application it becomes 1 4 9 16 so we are clear on how the competition electors are done here home morphic encryption just preserves these addition and application so you can see we are operating on cypher text but the arithmetic is done on a plain text we will get into more detail about what's the number of message slots so a high level idea it got released it is related to the degree of this polynomial the more at the higher degree you have you have more message slots when you are having more message slots
you have more parallelism and one one operation here operates on thousands of message slots that gives you a thousand to ten thousand times speed-up amortize timing and this is what matters in the last stage when when I say the perform is ten to the three to ten to the six that three orders of magnitude gap is introduced by these you should always use these whenever possible because otherwise you get a kind of a slow program and it's not efficient so enough on the plain plain text and message side and let's talk about what what are
those polynomials you need these in the in slice we try our best to match the notations so let's define what's the point Oh me ring we use this ring in home of encryption so it means a point o mio whose coefficients are chosen from the integers and the polynomials are a computed module X 2 n plus 1 so it means you in this ring in this are all the polynomials have degree at most n minus 1 if you have a if you ever have a term which is X to the N or X to the
n plus 1 or X 2 n plus 2 it will be reduced modulo X 2 n plus 1 for example module reduction X to the N equals to minus 1 in this rain you just wrap around and flip the sign so X to the n plus 1 is minus X well X to the 2n becomes 1 so this is a basic polynomial arithmetic in the ring and then further we have this quotient ring as the coefficients are now computed modulo Q so your coefficients are no longer just an integer they are represented with a set
of integers for example let's say Q equals to 5x example coefficients can be chosen from these five numbers they are zero balanced which is good and competition are done modulo 5 for example let's say you have 2 plus 2 you get 4 but 4 is not an element of this group in this set so 4 cut related got the image of 4 becomes here is minus 1 in this arithmetic so everything is time module 5 but you know you just mesh them into the correct element you can also think these as from 0 1 2
3 4 you can use those five numbers to just it's not 0 balanced it might be easier to understand but it's not zero balance so we don't normally use that and less to do in efficient programming like a regular code so here is a short example on the polynomial arithmetic modulo X to the n plus 1 and module Q so assume you have our 5 and a degree n equals to 3 here is the arithmetic if for those of you who haven't liked getting to this part you can try to calculate this thing basically you
just multiply them term by term you get this high diminish high degree polynomial and you start doing reduction let's say X to the 4 goes to minus X minus X X to the 3 goes to oh a costume minus 1 but the coefficient is 0 so is disappear and I eventually will get minus 5x and modulo 5 give you 0 the end result will be just minus X bar plus 1 this is the basic way how to do play know me or my patient and polynomial addition in our queue we will see our argue a
lot in the following discussion like if there's some application it follows these rules if there's addition it follows these rules the most important parameters are n log Q so the size of this Q and degree those two defines were security as Princeton has mentioned that almost all the efficient schemes based on the Ring learning this error problem is mathematical problem and we try to pair me ties the the security level I say for 128-bit security what parameters you should choose by parameters we basically mean in and lock you let's get into how the decoding and
encryption is done first you know the math I'm taking be Fe as example but just for you to understand how it works so your mess which can have a certain form your message can be chosen from complex numbers or it can be chosen from integers modulo T T is your plain text modules they say normal computer work sounds integers modulo 2 to the 32 which is a single word size you can think this is just the plain text modulus to the 32 or something else and it's a vector it's always a vector for efficiency what
encoder does is it Maps this message vector through a polynomial if you are using vfe which we have messages modulo T then your plain tags will be module T as well if you are using silky case you will have messages chosen from complex you get just a polynomial in 60 case some they might have larger in coefficients and here that the encrypter maps this plain tax polynomial into a ciphertext we should a pair of polynomials what does what it does is actually as noise to mask the secret which is the message or plain text and
then it randomized the ciphertext after it in each encryption so that encryption of the same plaintext give you different ciphertext always otherwise you just you can read the message anyway so this is how to make it secure and additional application these two operations are preserved in all three forms message plane tags or cipher texts you can do additional application on all three of them they always preserve your computation this is what Krishna mentioned by the completion encrypt condition canoes with encryption and what operations we can use in homework encryption the basic wines addition so addition
simple since you have two sided X a and B just add each point no meal together let's say you add a 0 is p 0 add a 1 with P 1 you get results in 0 and C 1 this is your addition result this is how the home effect addition is done and the if you decrypt this message if you decrypt these ciphertexts and decoded the message is the addition of you know a and B so it's quite simple for in for addition and in a case when P is a plaintext you just add B
to the first part which is even faster just half of the complexity computation these actually have code examples in Co Kim will explain that later you can see from the code that we have multiplied and multiplied with playing those functions in Co that very understandable and plain tags are computed modulo T if you're in BF e I just want you to know that these plaintext operations are not what you define you add 1000 with 2,000 you might not get 3,000 it's defined over these module T or define in the sick case how much precision you
want to preserve for example if you are doing module 1001 product a read reduction if your T is 1001 you add 1000 with another 1000 you get what you get 999 something like that so remember that there is there Mattox not just playing addition is modulo addition a module application these gray Gradle stuff are just for future reference if you want to refer back to this slice they explain the cost of these operations in terms of you know point nominal degree those things and here we also have a morphic multiplication it's a little bit more
complicated application actually give you 3 polynomials as a result you can see all 8 0 and B 0 are used in see in this computation you come here you computed 3 parts and this is your result this is ciphertext I'm ciphertex if bees a plaintext is much easier just multiply beads who post parts that is son you still have a two part polynomial help two part ciphertext however this becomes a problem when you have three polynomials in separate X if you want to do another multiplication what do you do there will be a lot more
completion and end up with more polynomials in the new ciphertext we don't want it to grow because when you're cyber cyber attacks get larger at the end you get like a huge result as the return result you don't want that so there's a step called linearization followed please also have a function in Co you need to call it what it does is very simple it just convert these three polynomial ciphertext to a new set of text with just two polynomials it's just a tool to convert it you can think it this way it's very simple
we just call it it converts it back to the 2.0 mio shape and it requires a realization key and this is just a public key if this is done during public key generation you can send it to anyone anyone doing the homo application can have this key and we need this key to reduce the ciphertext so so far we have three steps three functions and extra dolls are five functions because it also involves separate I explained Tecna patient so these five functions should be enough for you to build all s a polynomial evaluation or some
basic our prism and in fact most of the schemes are just built based on those five operations we actually have one more since we are encoding a vector of numbers you might want to rotate the Schloss of those numbers let's say I give you one two three four but you also once we have two three four one or some other kind of rotation there's a faster way to do rotation on encrypted data in Co you can find function like a rotate rotate column rotate matrix those functions rotate vector and what it does is just change
the sequence order of these slots and it requires something called the Galloway's key it's also public keys like a realization he is just required for the computation to be done anyone I have it no secret he want ability and as a room mention in his talk this key can be a little bit large and you might want to consider the storage of this device that was very interesting talk when people don't usually think about 50 megabytes public key is a problem a home of a home of encryption world because we start with gigabytes of public
key now it's just 50 megabytes it's super tiny in fact when you are doing like event for example you know competition you need to think about real-life example you want to think about users case I say someone has a computer offshore you need to send a lot of data to it you need to consider data size and this is something to consider like this key can be large and now you also have rotation kind of we have the complete set of operations we have if you're thinking about computer arithmetic you can think that we first
define addition multiplication and bit shifting so based on those three you actually have the modern computer and here's the same with these operations we can build very complex our prism let's combine some of them and rent it to code so suppose I want to evaluate Y to the 4 minus 2 y squared plus 1 for this sequence for this vector of values what you do is first you create a slot of n slots of 0 filled with 0 and put 1 2 3 4 at beginning so we have Y then you just encode Y to
a plaintext encrypt plaintext whites we encrypted Y and that's done with encryption and the following they say I have a to a vector of all tools we have a vector of all ones to you know just to mark these two constant terms they can be encoded through plaintext - and plaintext 1 so they become polynomials and they can compute with the separate XY best our is computation first you have squared Y you call this multiplied to himself so multiply Y and Y becomes Y Square and realization is required because you want to reduce it from
3 polynomial to 2.0 mules and then I want to multiply Y squared is y squared so I get Y to the fourth and also reduce the polynomial to only 2 and you multiply plaintext so this is encrypted Y is now Y square oh sorry this should be y square oh yeah that's recording debugging so I didn't write this code so this should be Y square you multiply this plane to you should get to Y square and let's say the result is stored here and you can subtract it from Y to the fourth so here is
subtracted this value from encrypted Z so in see now you have Y to the 4 minus 2 y square and then your furthers add 1 to it so get final result sure yeah later I'll explain it later so I'm trying to get get around parameter selection because so I write down this code you don't need a parameter selection you see you can just write down the code with nothing for me I didn't even run a cold you caught me so actually there's a better way to do this contagion is cut you require some circle optimization
to get a better algorithm so both size achieved the same thing compeition however with the right hand side is much simpler you see we have much you have two less operations we need to explain the definition of circuit here so give you a polynomial or some function there are many algorithms to achieve that function and one of the algorithm might have the minimal depth by depth I mean the layer of multiplications several decks multiplications so these solid box means ciphertext ciphertext medication these just this is just a vertex plaintext notation which we don't care that
much these separate several texts multiplication is very important we always want to minimize the maximum path of these multiple 'mom applications for for example in this graph this is the depth to circled this is the first level this is the second level so you will hear the level at the tabs and circled a lot I don't want you to get confused this is also a depth depth to circuit but it's simpler because you have less competition this is some optimization that usually cannot be done by a compiler you are responsible to write a better code
using these because this requires a polynomial factorization you need to go from alpha which is not part of the any compiler right and so far you kind of know how to write a simple code and what else we can do for completion we can have linear functions scalar vector matrix additional applications those are fine easy in homework encryption you can have polynomial evaluation k DB polynomial usually requires but K depth equality check can be tricky there are algorithm to achieve that in BFE is not possible in C KS because because is approximate you don't get
kind of equal you know you always want to get equal comparison is hard comparison is hard because when you're comparing negative 1 and 1 modulo 5 it doesn't make sense you're comparing 0.99 and I and 0 and 1 it they look similar you don't even know where they are Ecore now how do you know which one is larger which my smaller so these are this comparison is kind of hard but it's not undoable you can approximate the result with some high degree polynomial to achieve like approximation of the result that technique applies to a nonlinear
function tool this is Sigma inverse tangent or other functions you can always approximate these nonlinear functions with a plain Gnomeo if any one of you has ever used the MATLAB you have the curve fitting those things to give you a like a seven degree polynomial to feed the curve so you express a approximation of the curve with a seven degree polynomial which is a she friendly so fundamentally a she can do all the competition just be different cast with different effort if anyone asks you that can actually do something or I heard that a she
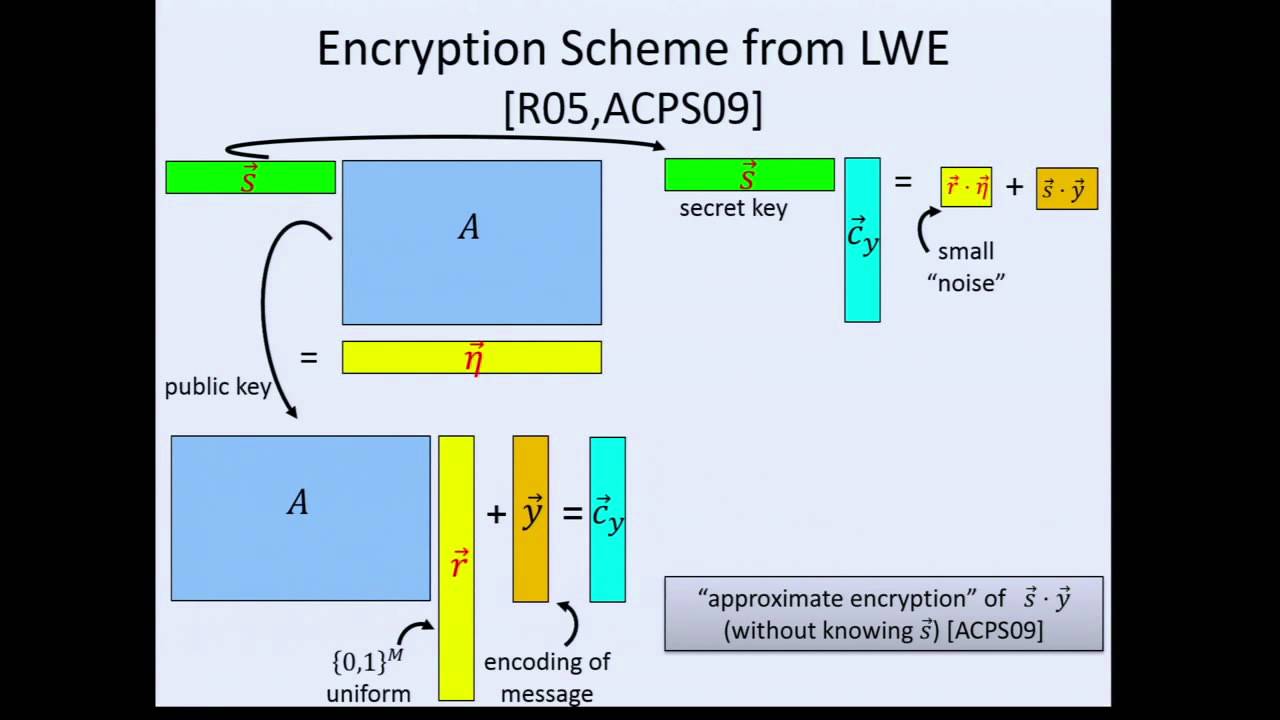
cannot evaluate nonlinear function is it that's not true and finally we get decryption and decode decryption and D coach's first decryption map the pair upon Gnomeo to a single polynomial which has plain text and then decode it to the vector and there's your result so we decrypt Z calling these you decode plaintext three colonies you get retail store in Z so super simple two lines how does the encryption decryption work we can get a little bit more in detail basically you generate a secret key which is as it's a polynomial from ring then you usually
secret key can be just a ternary polynomial means the coefficients are minus 1 0 1 they are very simple polynomials you can read it actually we for for example we can support symmetric encryption of 0 you just generate an error e is also polynomial from a discrete Gaussian distribution is give you a random looking cyber attacks they also sample a which is uniformly sampled from our queue so a is module Q polynomial you publish this thing this is minus a times s plus e some polynomial arithmetic happening here you get the result and the second
polynomial is just the a so these parallel point Gnomeo is the side products it's a symmetric encryption separate X of encryption of 0 we can use these as the public key so public key and severed X actually you can you cannot distinguish them you should not be able to distinguish them for example if you want to do a symmetric encryption of 0 that means I give you the public key I want you to encrypt something and work with my encryption and you can do that is a symmetric encryption what you do is you take the
public key which is two polynomials PK 0 and P k1 you sample you from the same distribution here is a point Gnomeo ternary you multiply two two polynomials here and you add two new areas and this is your s metric encryption of zero and when you want to encrypt some true value you just add the plaintext to this part with some modification then you have the cipher text encryption of sum together another view is that this is your plain text this is the mask module q for example a times s this part is removable with
the secret key during decryption but it's a huge noise so horizontally this is degree 0 to degree n n minus 1 vertically this is the say the least significant bit towards the most significant bit so here you should have lock you.here accuse bit and this is the 0 speed of your coefficients so let's assume this is a polynomial and you can see this is like a large error you are just masking the whole message space the other information are randomized a mask with this thing you also have some initial noise which is introduced with the
e this are considered small what you do is you lift your plane tags by some constant factor they say this is a PFA encryption what you do is you calculate Q over T something close to that I say your T plain text modules can be easy 1,000 or a small value the Q are usually large a few thousand bits you get a very large ratio here you scale your plane tags up by this ratio to raise it from the lower bits to the higher bits and you add everything up you get these you can see
there's a safe zone here they separate the message from the noise and this gives you correct decryption if you lose these if the plane tags and the initial noise cannot start overlapping you start to lose information in PFE you just decryption will fail in secure case you lose Precision's and along with the competition this noise will grow these masts is not a problem because they are always removable with the secret key but this noise will keep growing and she'll eventually will destroy the safe zone at that moment you're a decryption will fail multiplication introduced the
most noise that's why we want to minimize the depth cyberattacks every time a patient cause a lot of noise are you want to do them like in a tree shaped rather than in a chain let's say if you calculate the Y to the power of 4 by doing Y times another Y times another Y times another why you end up with depths for circuit if they have more noise my code might fail the decryption might fail because the depth is much larger however you cannot always do things with to that so you need to have
more depth you just encrypt N and Q once you know the dabs you should increase and hue to meet those computation need and I will explain how to choose an hue security to mean security need here are just some basic terminology you might got confused a lot of times I just leave it here you can check it online so how to set up these security parameters that's we are going back to the beginning if you want more depth you should increase Q because you need to draw the plane tags or the ceiling away from the
noise so you increase the vertical space by increasing Q while you're increasing sure I usually require some attempts it's hard to just calculate the minimum Q there are a lot of papers doing noise analysis is very hard to do and usually the best way is just to start with a Q try to evaluate the circle if it fails increase Q and if it fails increase Q that's the easiest way and then after you decided on Q you need to also increase n because the security definition is one for a given n the larger the Q
is the less secure the scheme is so to make the larger Q secure you need to increase n as well you can always choose parameters according to home own fake encryption security standard on this link you can find that for example in the table 1 you can see you have classic security Turner a security 128-bit security suggested pairs are and it's 1k and the lock Q is 29 you just need to find a 29 with Q and these are just four lines to set up the security parameter is first you choose the scheme then you
choose the degree and you choose the default queue using Co I mean luck you queue to be a power of two they see two to the twenty-nine for example you can take you to the power of two you can use a power of two but I need to explain the futures next I think a few slides more you will see that we don't use that so this is very easy to set up secure perimeters if you want to use some default parameters from see oh wow this is a better view to choose your parameters and
they say this this n this is log Q Y axis is vacu this blue line marks the 128-bit security stretch threshold above it is insecure for certain depths or certain function certain circuit this brown line marks the correctness when your when your Q is larger than these you get correct decryption you are looking for parameters from these triangle and usually when Q and n got larger the program gets more inefficient so this is the optimal choice how do you according back to the questions you probably will start with a Q here and turns out is
not correct you increase Q to something here turns out is correct but there's a space to reduce it then you reduce Q to somewhere here here are okay using the same n you reduce Q to somewhere here then you get the optimal parameters decryption will fail you can get the correct decryption result mm good question most of time thing you probably using that you can find another brown line here that give you a guaranteed correctness which also give you a little bit worse parameters we can further find parameter B's in this letter shape area so
I'll start explaining what's the form of Q we are using so the previous code you only choose the default parameter to set up the coefficients co compiler oh that's our plan actually so for example I think you know and we can talk about that we are working on a compiler that optimize these all these procedures for Co focus on vector instructions you have met Roshan right Roshan intern that's here so we've been working on that and we can get rid of a lot of these parameter settings just you write your code the compiler can work
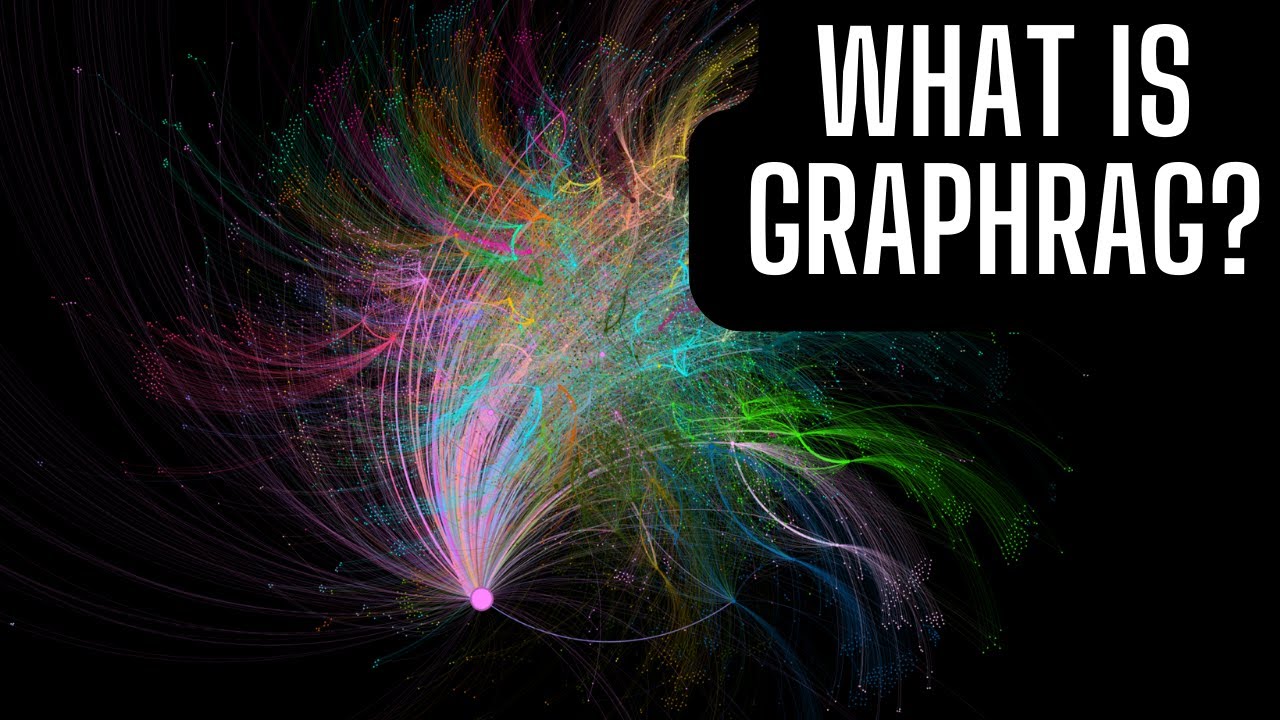
it for you it does not get you the optimal but in most of scenarios is pretty good parameters but again that doesn't include polynomial factorization so then how was the form of Q so we need to talk about these four RS variants we need that in later talks so RNA is residue number system or like it's similar to Chinese remainder theorem basically you represent a large integer with a set of smaller integers for example you if you have co-prime moduli 3 5 & 7 you can represent numbers from 0 to 124 and each one will
be represented by a three tuple of the remainder divided by three of them so for example 8 becomes 2 3 1 6 module 3 module 5 module 7 20 becomes 2 0 6 edition are done element wise by doing this form here you get 1 3 0 if you just calculate the mapping of 28 you also get 1 3 0 so this applies to additional map tation by using these we break large interiors meting to a set of smaller integer arithmetic and gives you a lot of speed up and this is very important most of
the RS schemes are better than their original schemes consequently we choose Q as a product of smaller word size prime numbers as you can see before from these parameters q can be a few hundred is large the computer cannot process that without like a number theory library or high precision library but we can use our Ness system to achieve that and it's very efficient the consequent is we need to set up Q - Q is and P there's also another operation here during the competition that you can discard something a prime from that Q so
your subtext got smaller in terms of coefficients it's a safe operation you can discard some of them your competition get faster the SafeZone is preserved and is very beneficial to get better performance and we net we will need that in the future like slice in future sessions so then how to set up the performance parameters before we are just using less a set co-op modulus PFE default there was the previous example but you can do something better by giving for prime numbers you can either write in for prime numbers here as a vector or you
can just tell the CEO to create for prime numbers and these for pro numbers have what a bit for a bit for a bit and 50 bit it is very simple you just tell CEO okay the queue size cannot be more than 320 they say cannot be more cannot be more than 170 bit so I choose for Prime's in total of 170 bits and you just passed these four values to the function and increase for primes for you there are some requirements the last one is with largest so that you have less worry about noise
during some operations just always make it the largest if you four of the same side I remember CEO will choose largest for you to put here so that from here we don't need to worry about what the primes are it shouldn't need to worry about their bit size and this is important to use in C key KS for efficiency this is just some basic idea to summarize everything let's go back to same correct order you start with an idea in your mind to do some algorithm and application function you need to write down write it
down as a circuit HD friendly circuit you just think you should think a she has new hardware rather than some encryption or or arithmetic spy so CPU works on instructions and good at branching and integers module to the 32 or 64 GPUs are better at half price in single precision double precision following points and bf ages is good at integers modulo TR arithmetic CK's is good with fixed precision or truncated approximated completion we just write your algorithm in a different way and then you express express the algorithm with these you get them in more depth
based on a tabs you can choose your parameters and there are some limitations here of course you cannot do complete conditional branching based on the ciphertext because you don't know the ciphertext you don't know the secret but there's an another way to achieve something similar which is a practice question you can solve it later also these two also nonlinear functions or also not polynomials they require some approximation which will be explained in the last talk today by how and then you set up the secure parameter set up the performance parameter this is not required if
you are calling some default parameters and then you're done is parameter settings you will construct some classes and in Co but those are simple simple you show that in demo in two sessions after this and then you can define your competition you can write down the code when you write uncle you need to remember that each function I have different cost here is just a synthetic view of the cost based on the number of prime numbers we have and the degree in you can see them application is the multiplication m and the realization notation are
kind of heavy so you might want to avoid using a lot of them if you can get rid of one of them by introducing two additions you should do that and here are some practice problems and you can just try to solve these questions if you have questions just ask me and these slides will be available online actually before that I want to quickly show that how to measure performance parameters performance benchmark result in Co so I'm running a silly example oh it doesn't present okay so here I'm running Co Co examples if you just
call the six example he was once you select a way to measure the performance let's say I want to measure CK's with the custom degree he asked you to type in a degree they say 2 0 9 6 it just print out the cost I'm measuring it on a Linux sub system which is not the best platform to measure performance but you can see gives you all the results in terms of milliseconds and micro second you can just use them to estimate the cost and you can see what patient realization are fairly slow compared to
additions there's everything in my talk I hope you have a lot to process during lunch time and we are going a little bit over time so let's quickly go outside to take a group picture and then we get back to lunch I hope you all can you know sit with your teammates so that you can talk more on and then afternoon session will start at 1:00 maybe a little bit after 1:00 all right [Applause]