By the end of 2012, American cyber security experts understood that there was a rat in their midst. To find it and its home base, Kyle Wilhoit, another expert in the field, attempted something of a social experiment. He built a water plant using advanced industrial techniques in the town of Arnold, Missouri.
Actually, he didn’t. There was nothing there except virtual signals sending fake data back and forth. Once the “plant” was connected to the internet, malicious actors attacked it from all sides, including some located in North Korea and Russia.
However, the most sophisticated attack came from exactly the source Wilhoit expected. His server was bombarded with a series of knowledgeable emails with legitimate-looking attachments. However, these were phishing emails, with malware embedded in these innocuous documents.
Wilhoit downloaded the malware. Again as he expected, his data was being stolen. He was soon on the chase, tracking where the information was being trafficked.
Fortunately for him, the attacker made no effort to hide its point of origin. It was a server in Shanghai, China. Wilhoit not only tracked the location, but was able to infiltrate the server, too, and it was full of government and corporate secrets, revealing the largest and most successful cybernetic espionage campaign in history.
Wilhoit had confirmed all of the suspicions that had been going on for years. He had uncovered Operation Shady RAT. In this video, we will take a look at China’s Operation Shady RAT and its military espionage in general.
We will also see how despite the undoubted success of its campaign to steal American military secrets, it has failed to copy them with complete efficiency. But what secrets did China manage to steal from the US* And how was it ultimately stopped in completing this mission? Stick around to find out.
A scandal in the Chinese military may have exposed some of its problems in late 2023 and early 2024, but there is still no doubt that it is much more capable than it was when Xi Jinping took power in November 2012. Building a world-class military that can contest America’s traditional superiority in the Indo-Pacific region is one of his highest priorities. Xi will stop at nothing to ensure that he achieves that goal by the year 2049, including outright robbery.
The then-outgoing United States Director of National Intelligence, John Ratcliffe, described China’s general approach to intellectual property theft as “rob, replicate, and replace:” “China robs U. S. companies of their intellectual property, replicates the technology and then replaces the U.
S. firms in the global marketplace. ” China has attempted the same approach to military technology.
The two are part of the same campaign through Beijing’s strategy of Military-Civil Fusion. According to the US State Department, the strategy aims to bring down barriers between commercial and military technological applications. The robbery of civilian technology, particularly in the emerging field of artificial intelligence, is something China wishes to apply to improving the People’s Liberation Army as much as it wants to use it to replace Western firms at the center of global commerce.
Espionage is therefore an all-encompassing strategy for the Chinese in their ambitions to emerge as the world’s leading technological and military powerhouse. State-sponsorship of hackers is one of the most important tools of espionage in China’s arsenal. This is the origin of the hacker group alternatively known as APT 1, Comment Crew, Comment Panda, GIF89a, Byzantine Candor, and several other Chinese language names.
The attacks by this group are known collectively as China’s Operation Shady RAT. APT 1’s known activity began in 2006 and first targeted a South Korean construction company. Targets since then have ranged from commercial enterprises, government agencies, non-profit groups, the United Nations, and even the International Olympic Committee.
These seemingly separate attacks were first identified as an organized phenomenon by Dmitri Alperovitch, the VP of Threat Research at McAfee, in August 2011. By then, he had confirmed over 70 targets, 49 of which were in the United States. The method was the same – a series of spear phishing emails sent to those with a good level of access in the target entity.
These emails closely emulated colleagues or other people who were knowledgeable about the entity being targeted. The only giveaway that something might not be right was that the emails sometimes seemed to be written by someone who had a less than perfect command of the English language. These emails would contain an attachment that housed malware.
According to Alperovitch: “That malware will execute and initiate a backdoor communication channel to the Command & Control web server and interpret the instructions encoded in the hidden comments embedded in the webpage code. This will be quickly followed by live intruders jumping on to the infected machine and proceeding to quickly escalate privileges and move laterally within the organization to establish new persistent footholds via additional compromised machines running implant malware, as well as targeting for quick exfiltration the key data they came for. ” Crucially, Alpverovitch identified 13 defense contractors that had been targeted by 2011.
In 2013, cyber security professionals working with Mandiant, a subsidiary of Google, gave the group its name and discovered what it really was. A more recent report in December 2021 followed up on this conclusion. APT 1 was actually Unit 61398 in the People’s Liberation Army.
It and APT 1 are identical in location (near Shanghai), mission, and capabilities. This unit is known to carry our information and electronic warfare, ranging from cybernetic efforts to more mundane tasks like posting propaganda on social media. As early as 2009, it became known that stealing military secrets was one of APT 1’s highest priorities.
A young Chinese hacker first got on the unit’s trail through discovering that his client, an American defense contractor, had found malicious programs on its computer network. APT 1’s attempts to steal military technology go from large pieces of hardware that we will look at in a moment to far less spectacular components. For example, known targets have included 29 chemical companies and 19 other firms that make materials for military use.
The theft of this information gave China data on how to construct the finished products it was attempting to steal. The similarity of many of China’s new weapons to American designs leaves no doubt that the work of APT 1 and other Chinese hackers has found its way into the PLA. Examples abound.
One of the most obvious is the CASC Rainbow drone. This UAV is almost an exact replica of the American MQ-9 Reaper. The Rainbow can carry six weapons, a payload between 250 and 340 kilograms, and has a ceiling of about five kilometers.
Likewise, the Reaper can carry six weapons, has a 380 kilogram payload capacity, and comes with a service ceiling of about 15 kilometers. China’s HJ-12 Red Arrow portable anti-tank weapon is another blatant example, as it is an almost exact knockoff of the American FGM-148 Javelin design. The Red Arrow has an effective range from 75 to 2,000 meters, extendable to 4,000 meters with TV guidance, can penetrate 800mm of armor, and launches a Tandem HEAT warhead guided by infrared or TV imaging.
The Javelin has the exact same attributes. Then there is China’s Harbin Z-20 helicopter, which looks almost the same as the American UH-60 Blackhawk. It has a length of 20 meters, a 16-meter main rotor diameter, and a 5.
3-meter height. It can carry up to 10 tons and may be armed with machine guns, rocket pods, and various missiles. Likewise, the Blackhawk can be armed with similar weapons.
It is slightly smaller but has otherwise similar dimensions and can carry a little more weight, at 11 tons, but there is no doubt that the Chinese design was “inspired” by the American one. China has not been as successful in creating exact replicas of other weapons stolen from the United States, though. However, the stolen American weapon designs have nevertheless been critical in strengthening China’s military.
In a move that left little doubt about Beijing’s intentions, Lockheed Martin was one of the first targets for Operation Shady RAT. Lockheed Martin is the manufacturer of both of America’s fifth generation fighter aircraft – the F-22 Raptor and the F-35 Lightning II. As early as 2007, APT 1 compromised Lockheed Martin’s network in a major way.
Not coincidentally, China’s first fifth generation fighter, the Chengdu J-20, had its maiden flight only four years later. Another fifth generation fighter in development, the J-31, had its first flight in 2012. At first, the US military denied that it and its contractors had suffered a major data theft, but documents later leaked by Edward Snowden confirmed that Chinese hackers had indeed stolen sensitive information on the F-35.
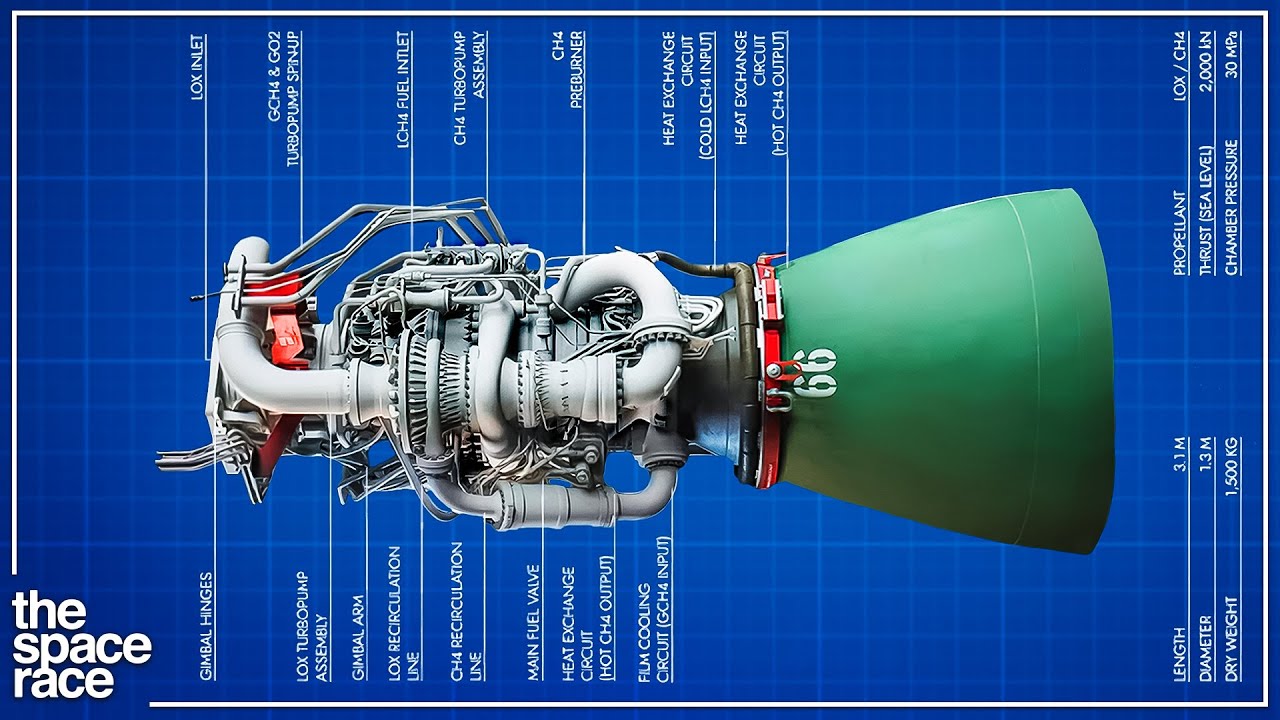
The documents revealed that Chinese efforts particularly focused on getting the plane’s radar design and engine schematics, among other secret materials. Terabytes worth of data on the Lightning II were taken. The hackers with APT 1 also succeeded in stealing information on the F-22, the B-2 Spirit bomber, space lasers, missile navigation and tracking systems, anti-air missile designs, and material on nuclear submarines.
These were only the more notable examples of over 30,000 hacking incidents which included 500 “significant intrusions” into the US Department of Defense, over 1,600 DoD computers compromised, and 600,000 user accounts infiltrated. 50 terabytes of data were stolen; equivalent to five times the total information content in the Library of Congress. The damages were estimated to be at least $100 million.
The Chinese government has denied any involvement in these incidents. At the time of its maiden flight, aviation experts noted certain similarities between the Chengdu J-20 and the F-22. While the Chinese plane is bigger and heavier, suggesting an emphasis on long range and heavy weapon loads, these authorities noted that the stealth body shaping of the J-20 was like that of the F-22.
Both planes had flat body sides aligned with the canted tails, clean wing-junction bodies, and sharp chine lines around their forward fuselages. Notably, they noted that the can't angles were greater than that seen on the F-35 and the J-20’s frameless canopy was similar to that of the F-22. The weapons bays were also noted to be like the F-22, with the J-20’s landing gear retracting into body side-bays.
However, even back then, these aviation experts saw that the J-20 might have been a less than perfect replica of the F-22 if stealth was what its engineers had in mind. Notably, the aircraft’s rear features, like underwing actuator fairings, axisymmetric engine exhausts, and the plane’s ventral fins were suboptimal for stealth designs. Writing for Aviation Week in January 2011, Bill Sweetman came to a predictive conclusion: “There are two possible explanations for this: Either the aircraft seen here is the first step toward an operational design, or China’s requirements do not place as much stress on rear-aspect signatures.
” The latter has proven to be the case, whether through China’s intention or not. While the J-20 is a major step forward for Chinese aviation, most of the plane’s stealth features are indeed concentrated in the front. The sides and rear of the plane are comparatively lacking, meaning that if it needs to turn, the J-20 is much more detectable by radar.
The J-20 also has a few features of the F-35. It has an active electronically scanned array (AESA) radar potentially boasting some stolen technology from the F-35’s AN/APG-81, which makes some experts believe that it has the potential to act as an airborne early warning command and control (AWACS) aircraft. It mounts electro-optical and infrared sensors on its frame to provide 360-degree situational awareness to the pilot which can be shared with other friendly assets.
Despite the stolen technology, though, the J-20’s radar is still likely an early AESA radar originating from the J-XX program in the early 1990s, one which cannot quite match the flying supercomputer capability of the F-35. Some Chinese security experts have also quietly admitted that even the new engine for the J-20, the domestically designed and manufactured WS-15, is at least a decade behind the F-35’s Pratt & Whitney F135. China’s infiltration of other American defense contractors is also made clear by the advent of the stealth strategic bomber it has in the works, the Xian H-20.
Although this bomber has never been put on public display and has missed its maiden flight scheduled for 2022, available evidence from a PLAAF recruiting ad that came out in 2021 suggests that its design is similar to the B-2. Like the Spirit, the bomber’s design seems to be based around using stealth, rather than speed, to penetrate an enemy’s air defense zone. It is a flying wing design with a blended wing body, embedded engines, and a lack of vertical features, all of which make it less detectable to radar.
As for its own radar, the H-20 will likely boast an improved Chinese AESA system to better observe lower-detectable threats and identify targets at longer ranges. The internal and external design of the revealed H-21 seem to confirm that China has infiltrated the B-2’s manufacturer, Northrop Grumman, and stolen data on the Spirit, as the Snowden documents suggest. American intelligence officials believe that China’s stealth bomber program began in the early 2000s, with Chinese aviation experts studying the feasibility of both flying wing and supersonic delta wing versions.
The early 2000s seems to have been a time before the advent of APT 1 and Operation Shady RAT, but another date provides a clue about the influence of the PLA’s hackers on the effort to create the H-20. The project team at the Xi’an Aircraft Industrial Corporation’s 603 Aircraft Design Institute seems to have settled on a subsonic flying wing aircraft frame with four engines in 2011, years after the launch of Operation Shady RAT. It is possible that the PLAAF and XAC originally began with the idea of a supersonic delta wing bomber but after receiving APT 1’s data, went with the B-2 knockoff idea instead.
The dimensions for the two planes seem similar. The H-20 even likely uses four engines, just like the B-2. Around the same time as this change, the USAF began laying plans for the coming replacement for the B-2, the B-21 Raider.
It is unknown if any of the details on the new bomber were stolen by China’s state-sponsored hackers, but Operation Shady RAT was designed not only to retrieve existing data, but to keep malware on infected computer systems to steal future data. It is possible that APT 1 had malware buried deep within Northrop Grumman’s network and lifted data on the B-21 as it was conceived in the early 2010s. However, despite China’s clearly successful theft of information related to at least one of America’s stealth bombers, the H-20 is likely not a perfect knockoff of the B-2.
Although we cannot be certain until the plane is actually revealed to the public, the H-20 has a few features that seem to make it more detectable to radar than its American inspiration. Available evidence suggests that the H-20 may be able to adjust its wing angle. However, the seam required to do this makes the plane more detectable.
If the wings are angled at any point, the plane will be much less stealthy than if it had a smooth design like the B-2. This reality leaves one wondering why Chinese engineers decided to build such a feature if stealth was the intention. With both the J-20 and the H-20, China has shown that it may have been able to lift data on stealth aircraft, but it has a less than perfect understanding of why America designed those planes the way it did.
Data can be stolen, but institutional experience is a lot harder to replicate. China has also been keenly interested in stealing naval secrets. Building a navy strong enough to challenge America’s maritime dominance is vital for it if it wants to break the containment of the First Island Chain, which is the chain of islands encompassing Japan, Taiwan, portions of the Philippines, and Indonesia, and become a military superpower.
The Snowden documents revealed that China had indeed stolen technology related to America’s nuclear submarines. This is an item of particular importance for Chinese naval strategy, as America’s nuclear submarines are well-protected against China’s arsenal of ballistic and cruise missiles, and therefore can bypass its anti-access/area denial strategy in the First Island Chain. Countering them and getting equally advanced submarines is therefore a high priority for Beijing.
China has only a few nuclear submarines, and even the ones it does have are noisy. The existing submarines are noisier than Soviet-era nuclear submarines from the 1970s, which makes it almost impossible for them to bypass the First Island Chain’s choke points without being detected. The PLAN has two new submarine types in development to make up for this shortcoming.
These are the Type 095 nuclear attack and the Type 096 nuclear ballistic missile submarines, respectively. Both of these submarines should be significantly quieter thanks to the presence of a single hull, a shaftless drive, and electronic noise-cancellation technology. The new submarines will also be larger than their predecessors, which will help keep noise lower because the diameter on the previous ones was too small to provide enough space to insulate the steel exterior from the interior vibrations of the vessel’s machinery.
The exteriors will also have anechoic coating to make them less detectable. China has also used Russian technology to make its submarines quieter, as seen in the latter’s Akula-class submarines. The influence in stolen American designs might be particularly seen in the coming JL-3 submarine-launched ballistic missile, which is expected to have a range of about 9,000 to 10,000 kilometers.
Each of these missiles might carry multiple warheads delivered through multiple independently targetable reentry vehicles. This feature may have been inspired by the US Navy’s Trident II, which can carry up to 14 warheads with Multiple Independently-targetable Reentry Vehicles or MIRVs. However, the Center for Strategic and International Studies still believes the JL-3 will be less payload-heavy, with up to about three warheads per missile.
It is also notable that the Trident II still likely has a longer range than the JL-3, at 12,000 kilometers. Despite some remaining shortcomings, experts expect that China’s new submarines will be operational by 2030, and pose a much more formidable threat than the current submarine force. This is partly why the United States and United Kingdom decided to share nuclear submarine technology with Australia in the AUKUS agreement of 2021.
China’s military still has rough edges. The recent scandal revealed that corruption remains a persistent problem. Nevertheless, it is no longer the military backwater it was 30 years ago, at the time of the Third Taiwan Strait Crisis.
Beijing has built a military machine much more capable of offensive power projection, and one whose weaponry and technology is still improving. Gone are the days when China fielded outdated second generation fighter jets and had limited naval capability. The improvements in China’s military technology have at least as much to do with its state-sponsored espionage campaign as it does with its domestic defense industry.
China is much more careful about its cybernetic efforts today and the cyber security of American governments and defense contractors are far more sophisticated. The brazenness of Operation Shady RAT is now a thing of the past. However, its impact will be felt for many years to come.
China’s rise as a military power is in large part thanks to the extensive set of secrets that APT 1 was able to lift from America’s premier defense contractors through the use of innocent-looking phishing emails. Although its ability to completely replicate and replace American military technology seems less clear, China’s hackers have demonstrated their ability to rob, and sometimes, that is all you need to make yourself powerful enough to undermine the international status quo and the efforts of the ruling power to maintain it. PLA Unit 61398 is still active.
What do you think of China’s Operation Shady RAT? What other military secrets might it have stolen? How will Unit 61398 operate in the future?
Don’t forget to let us know in the comments. Also make sure to hit the like button and subscribe to the channel for more military analysis from military experts! Now go check out Real Reason Why China's World Domination Plan Failed or click this other video instead!