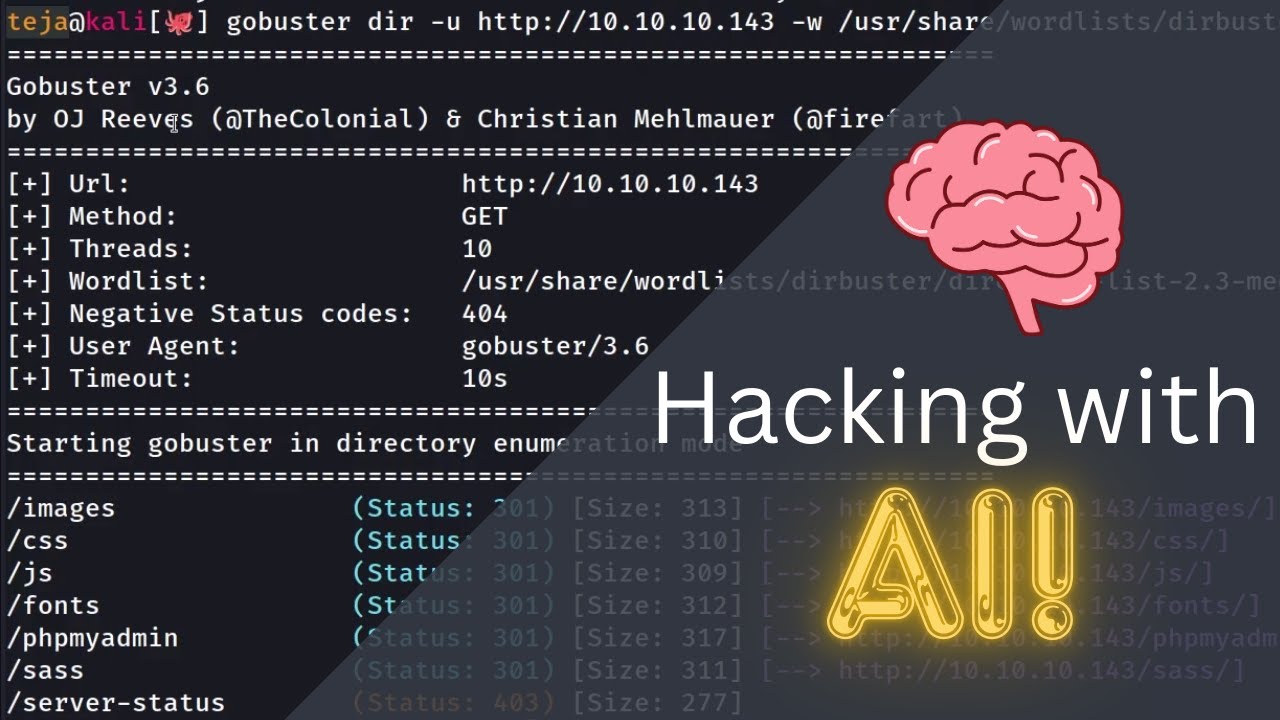
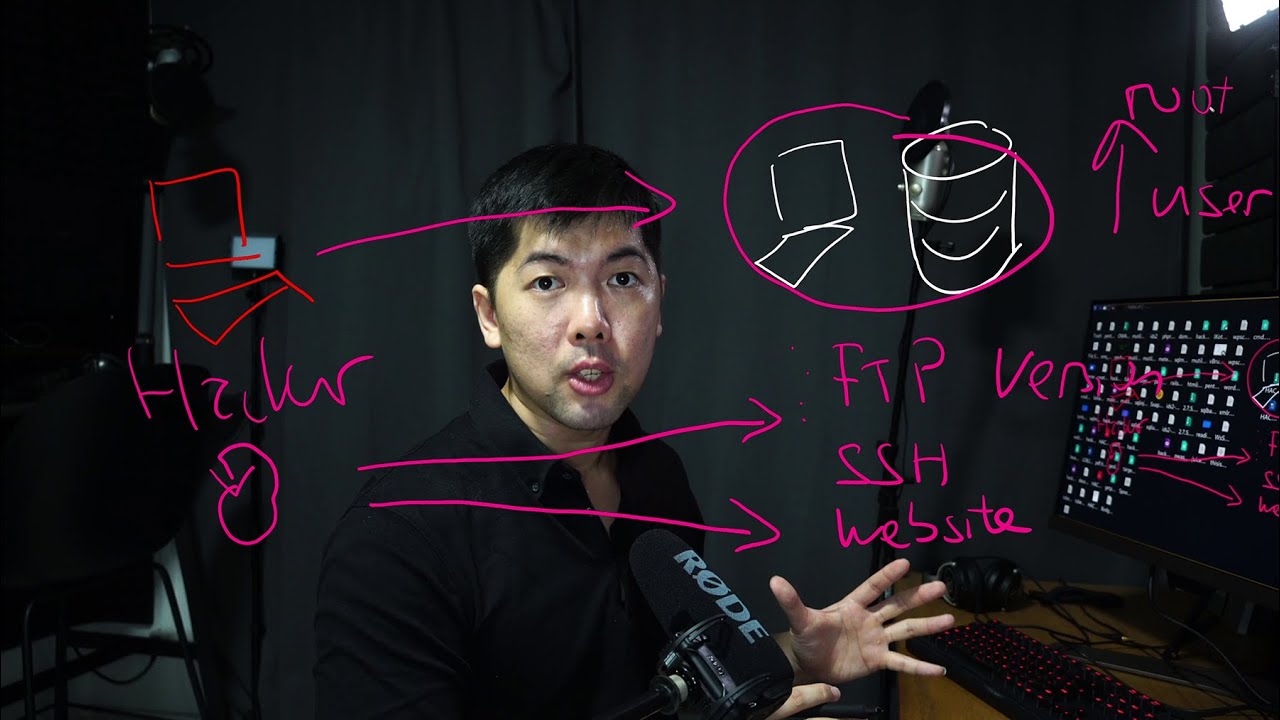
so today we'll be learning about how to take advantage of an application service vulnerability that allow us to run code on it that gives us remote control of the entire computer before we get started hacking kids remember hacking is illegal remember to ask your mom for permission first before you start hacking the first thing you need is a target computer and again in this case we can't have any IP address as long as we're able to connect over to it at other times it can also be that this is a website you're targeting and it leads you to the IP address in which we can run our scanning and your BFF Mrhacker law is going to be right here targeting this specific site scanning it using say things like end map be able to look up for application vulnerabilities or entry points that we can Target which will then allow us to execute C Cod which gives us full remote control of the entire computer before we get started remember to smash the like button and turn the notification to this channel so that you get notified the moment I hack into you so right in front of us we have col running and this is going to be your favorite ticle hacking operating system in fact it doesn't really matter you can be using Windows XP and you could still hack into the machine as well so once you're in here you have the website name and of course in this case could been hack aog. com example. com whichever and the next thing you want to do is just scan this machine and you can see here I have terminal running and all I got to do is enter things like nmap which is our Network mapping tool against the target IP address in this case 1821 16801 60 so you do this scan and it will tell us what are the Services that's available so most of the time in a computer in a machine there are things that are running like different types of services it can also be agents which may be open or in other times there could be some other services that help them understand or manage backend databases back and active directory and so on so forth whichever the case is and we want to uncover that so that we know that there are more services that we can Target so you can see right here we sever ports and in this case we're targeting Port 9,200 which is for a elastic search service there are also many others that we can Target for example port 8080 is likely going to be another web server or web service in this case if we go ahead and open up the browser and we enter the additional port in this case 8080 hit enter on that what do we get your server is now running all right to replace this page override index.
html there is a administrator console and so on so forth so again these are additional services that can be running which means more potential opening points entry points for us to gain access into the entire operating system now of course in this case we're targeting Port 9,200 which is for elastic search and I can see here we have the result status 200 name we have the version number and so on so forth and elastic search is basically an analytic service you Control Data edit and you're able to query those data and what I'm going to do now is use burp stre as an Interceptor to look at the different types of malicious payloads that we can send over into this specific specific service so in this case go ahead and enter burp Suite Follow by and to random go ahead and click next on it click Start burp so we're starting up the burp Suite Community Edition now which is going to be our Interceptor so we can see here under the proxy tab we have intercept is on all you got to do is go back over into the browser go in the top right corner and click onto enable foxy proxy burp Suite so done I hit enter on this we have the interception right here you can see the fing on the left get SL http oneon-one send this over into repeater and I'll be teaching you both ways the first way is going to be the automated way where we use mploy to help us inject those payload but that's not good we are not script kitties so number two way is going to be a manual exploitation of the specific vulnerability I'm going to teach you just that so yeah you got to watch to the end if not I will find you I will track you and I will get your password and I'll find everything about you I'll take over your whole computer and your mobile device we want to look up for vulnerability specific to elastic search of that version so in this case we have the version of 1. 1. 1 go back over in terminer enter search SWAT enter the following of elastic search it enter on that and we have several options here and you can see right here elastic search remote code execution 2014 3120 so this is the one that we can using good news it's available directly in mploy so the first way is going to be the script Kitty way and all you got to do is enter pseudo msf console go ahead and enter your password and you are now starting up mploy and with that all you going to do is just search for elastic search right in this case and use that exploit to run it against the target site and it's really straightforward so now it's loading all you got to do is enter the following of search elastic search hit enter on that there are several options here and the option that we're going to be using in today's tutorial will be the first option all right which is script mvel remot code execution all you got to do is enter use zero hit enter on that and show options and once you're ready go in and enter set our host 1821 16801 160 so this is the target site that we're going after set Target URI in this case the URI to elastic search is going to be of the following all right so we have the target of the following so everything is on default so we don't have to set the target URI and we are ready we ready to launch the attack and all you got to do is enter exploit hit enter in that and you see the following we have started the reverse TCP Handler trying to execute arbitary Java remote OS is Windows server and da da da done we're in all right all you got to do is enter the following of shell and then you enter say for example who am I and we have anti Authority system where I can answer di it's done it's game over it's as simple simple as that now To Be A Serial hacker we have to use some interception tool and if I click on to send you can see right here on the right side with the response directly from the service next up you can see that I've added the filling of underscore search pretty additionally I also have the content type application Json which will be inserting into the body now here comes the juicy part and this is the one that we're going after you can see right here with following of java long runtime get runtime and we execute on following cmd.
exe which then uses certain . exe to download a specific file and we drop it into a directory so usually we drop it into Tam directory but I want to make this look a little more cinematic so you have the hacker Loy and c. ex and we're hosting a Nat cat.
exe from col Linux that the target server is going to download from and then we'll execute on that so once you're ready go ahead and click Send boom done the file is now a available inside that machine changing the code up a little right now you can see the following we're using cmd. exe but right now we are going to execute on through that file that we have downloaded and then heading over into con Linux IP address port number and a running cmd.