[Music] hey everyone my name is gal shafir uh and I lead our Global Security architect team here at Google Cloud Security in in our demo today I'm going to show you how our groundbreaking Chronicle security operations platform uh enable security teams to detect investigate and respond to cyber threats with the speed scale and intelligence of Google the platform overall is built out of Three core pie pieces Sim sore in applied thread intelligence all of which are natively built into a single unified solution that is easy to set up and use uh and it really supports
security analysts and Engineers through their entire journey of collecting the logs normalizing and enriching them with more data uh detecting threats and searching through them to the operationalized uh side of operationalizing them making them actionable through case management collaboration Auto aut at playbooks and triage to really the decision- making process uh and and ending up in a resolution uh and to make things even better we supercharge our Chronicle secops platform with du AI which is Google Cloud uh Cloud uh AI collaborator that provides generative AI powered assistance to make things even easier for people to
adopt and see uh quick value out of it so on the you know Flow Part of of the platform um this is kind of what it looks like right on the Sim side I'll say that Google certainly knows a thing or two about scale and searching through large amounts of data is you know literally what Google uh is known for doing en lightning speed uh Google has applied the same scale in speed to Chronicle so it can ingest huge amounts uh of data uh and analyze it uh from you know multicloud environments stas environments and
on- premise environments um to detect an invest instigate threats on the sore piece uh Google Cloud's you know uh recent acquisition of simplify uh you know for security automation orchestration respond um and it's designed to enable security teams to collaborate manage their sock and to automate workflows and respond to threats within minutes instead of hours or days on the applied threat intelligence side which really goes across this entire platform throughout the entire Journey I think that many security vendors can say that you know can talk the talk but very few of them can really walk
the walk and I'm sure a lot of vendors out there can claim that they have great in thre Intel but very few if any can claim that they're actively protecting billions of users and mailboxes and devices and browsers on a daily basis uh and as a result Google has built its own thesis around what good threat Intel should look like now combined that internal knowledge that Google has with virus toal which is the world's largest crowdsource thread Intel Observatory with mandian thread Intel which is one of the world's leading QA detection intelligence sources that exist
today in the world and you get what we' like to call the largest threat telescope in the world uh which is now available to customers and Infused into our SEC Ops offering as part of this platform so um let me put my junior security hat on uh and start by diving into this case CU which is really the place where analysts spend most of their time all of those cases that you can see here on the left were created by alerts that were ingested by detection rules uh including our outof the-box curated detections and out
of the box UA detections uh or really by any other supported data source like monitored fishing mailboxes or other thirdparty SIM vendors that can be plugged in ETC of course that the Automation and respon B has been processing this queue already closing out a lot of noise and false positives um so the queue that you see here includes only the alerts that still need my input on um some of these alerts have mature playbooks and merely require analyst validation uh to finalize remediation and some alerts and cases here uh have completed triage and enrichment and
are ready for us to dive deeper into communication and Remediation so let's just open this this uh cryptocurrency uh mining case the first thing that we'll see is that Chronicle uses patented technology to group rated alerts into threat Centric cases this way an analyst handles a threat oriented case as opposed to individual uh alerts and events uh that would probably go to different analyst that are actually probably a part of the same Potential Threat so I'm about to to start investigating this cryptocurrency mining case uh which grouped two seemingly unrelated alerts um the First Alert
tab is noticed as the malware detection from our outof the boox EDR detection rules uh and the second alert tab uh notifies me of a crypto mining activity that has been detected by Google's security Command Center this is probably indicating malicious activity and I'm being asked to take action and contain the end point but before I take that action I want to further understand what's going on normally uh in order to understand this case uh and what's going on here I would need to take some time to figure out what the threat is um and
how it affects my organization I would also need to probably go through all of the alerts grouped in this case one by one and check all the events and entities and enrichment from The Playbook that are involved here and I would also probably need to go through the case wall and see you know the Playbook results and outcomes and decide uh if any further steps should be taken however now that I click on the case uh tab I see that duet AI has automatically collected all of the full context and then summarized the case for
me front and center in fact based on the guidance here I see where things are at why should I consider looking at this case with a higher priority plus recommendations on what the next steps uh to respond to the threats um further by clicking on the explore button here on the top right I can see the entities graph correlating the common entities involved with this detection for the alerts and in this case I can see it's you know involved with an asset labeled as Lin minor1 so going back to the top of the alert here
um I see that there's a Playbook um that was designed for the scenario actually and was automatically triggered for this alert and it actually has a pending action right we'll explore playbooks in more detailed but for now um I can see right away uh that by you know clicking on The View Playbook tab I can actually pivot to my playbook um and when I do that I see that the Playbook has sent some emails and rent some thread intelligence performed enrichment made some decision um and also gathered contextual data on the Endo from crowd strike
in this case this is really helpful for me uh so far but really before taking the further action here of containing the Endo or escalating the case I just want to have a further understanding of the type of malir that has been detected by chronical um curated detection rules um with leveraging the the thread Intel that we have here from viral and ment and then I want to scope out the impact of this malare to my environment so um I'm going to start that uh process by clicking on the overview tab from The Playbook and
pivoting here once I'm in the malware detection overview here I scroll down uh to review the malware verdict right with 46 out of 70 um engines as positive provided by virus toal alongside the malicious confidence rating which is 100 as you can see here provided by the Mandan thread intelligence by the way both of those thread Intel sources are included as part of our Enterprise Plus SEC Ops uh package for customers so at this point I understand that I need to quickly scope the impact of this malware to my environment and start moving forward with
a response to learn more about this threat that I'm facing I can see what the virus toal Community is saying about this threat uh in the attribution tab right so I see all the comments here from the community and now um that I verify that the crowdsource intelligence suggests me that I'm dealing with something probably malicious here I can decide to Pivot into mainan curated detection and see what the mandiant Intel analysts have curated around this threat uh to learn more about the risk for my industry for my organization thread tactics and targets here um
so I can click on the ment link right here um to see what the analysis is in the man and Advantage platform it really gives me much more visibility into this threat so I can quickly quickly see uh what are the threat actor attributes in malare associations I can figure out quickly who is targeting uh why and what are other ioc's that are known to be related to this threat so I can later add them potenti essentially to my chronical investigation and extend it by hunting for them in my environment I see that this hash
is linked to a threat actor called ap43 and clearly if I click on that I see that there's a lot of attributes and articles and associations and ioc's related to it um that really refer to it in the mandian advantage platform um but in order to see all of them I can actually you know decide to run a search on that term ap43 to get to all of them normally um I'd had to you know maybe write a report about this threat that's targeting my industry but normally I'd have to parse through 11,000 plus results
to you know spend time figuring out which thread intelligence uh reports and thread Intel objects are related to my mission and decide which core takeaways are relevant but now with do AI I see the content on this thread actor in recently summarized from ment massive corpse of Intel data plus this model is grounded which helps reduce uh LM hallucinations and means that I have accurate summaries to use in my reporting uh that I might want to create for my team including my ceso and sock manager I can immediately see here in the report and in
the summary um that this threat Intel uh this threat uh is deploying crypto miners uh and is targeting Financial organization um Android op developers and journalists and now that I understand all of this context I can pivot back to my case with all the new understandings that I have so when scoping out a malware like uh case like this you'd need to access uh some historical EDR data to confirm if there are other assets that have been observed and associated with the malware uh hashes for example um and you need to be able to search
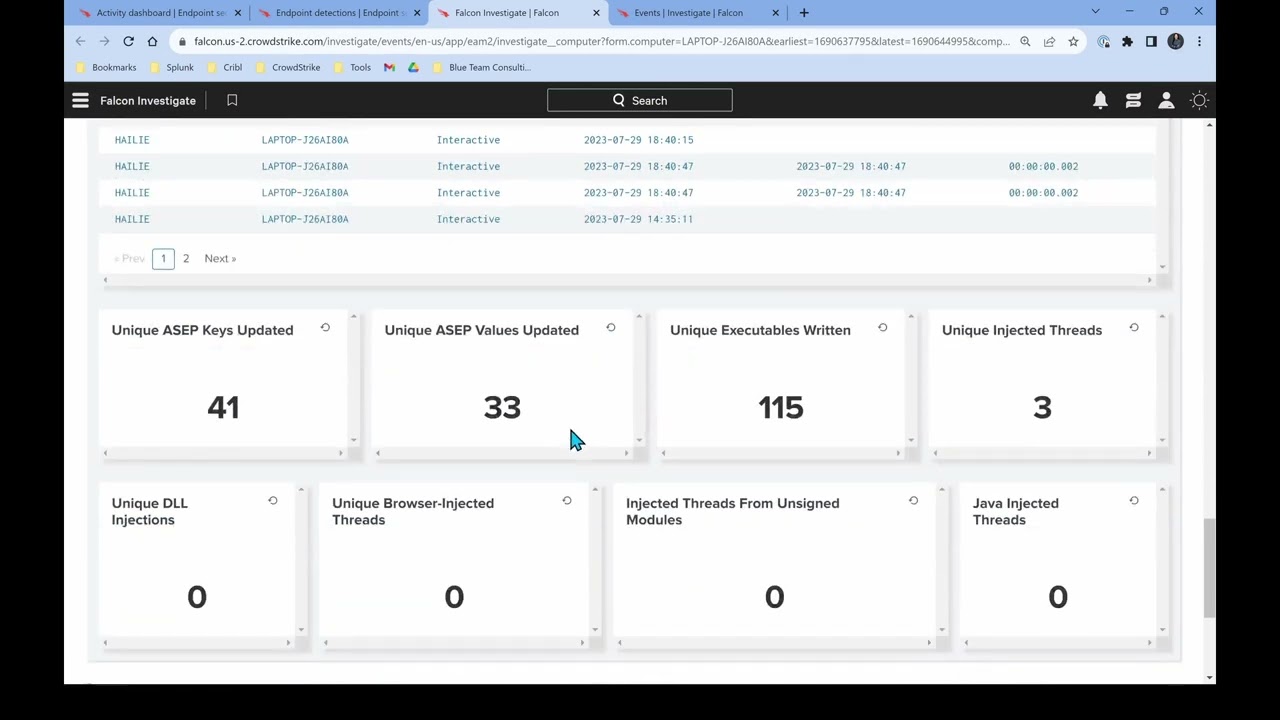
the historical EDR data very quickly regardless of of the data volumes and and the formats of the data the beauty about chronical Security operation is that it's enabling you to do that across huge amounts of data sets with a single click so let me show you by clicking the explore button here right next to this um red file hash to see if there's more context around this hash once I click explore I immediately see that there's three distinct assets that have been observed with this crypto minire uh hash right related to them in past events
so my scope just went from one asset to three dating back to August 22nd to uh to 2023 with potentially Lin minor 03 being patient zero most likely this maler at the time was unknown and maybe have gone undetected but this is a great example of why organizations should return retain their EDR data for long long period of time with Chronicle our default retention period for all data is one year and that's all hot and actionable Chronicle also automatically stitches together multiple data sets into investigative views such as hash views or asset views to increase
the anus productivity and enable them to quickly take actions on saw cases so one example is by clicking the first observe button here with a time stamp Associated to to lean minor 03 um and piecing together the event timeline of really what happened on this case just before and after the malware has been seen so uh we can really see the full story so we quickly see within the event timeline that the user has logged into their PC and maybe opened an Excel file sheet could be uh you know a macro that's been running and
immediately after really opening the the Excel the malicious uh activity has started another way to run investigations through all of the chronical data is through the Sim search or what we like to call the udm search which stands for unified data model um so I understand uh and and really to decide to run the search through pedabytes of data I can run a search for maybe crypto mining attack Google Cloud last week to see if there's any other alerts in my Google Cloud environment that could potentially be related to my investigation usually in order to
conduct the search I have to know what EDM uh udm Fields uh to use I need to know and type very specific Syntax for my query and frankly I need to be patient since queries can be large and challenging to create uh and to deliver exactly what I want to see but now with du AI it automatically translate my search query to Chronicles unique data model so I can run that search here or even add it in line and update the search in real time so my query has resulted when I rent it uh in
finding related events and I can click on the event to get more information about it including the raw data if I need it the severity and risk score from Chronicle and I can see that there's also an active investigation and case running for it uh which is really by the way the case that we started from in this case so I can just click this button uh to easily pivot back to the existing crypto mining case for summary we just walked through a unified sock workflow from initial case triage to understanding the malware intelligence and
then scoping out the potential impact to my environment in a matter of a few minutes I now feel confident about taking action um and really make you know to make things easier for me um The Playbook summarizes all the remediation actions um that I may want to take in one central place I can see that I can contain the endpoint and escalate uh the case to my sock manager uh for further response Etc what's great about Chronicle uh is that there's many hundreds and hundreds of built-in Integrations so I don't even have to open another
console or be an expert on my EDR platform just clicking on the done button will execute the remediation sequence uh and contain the endpoint for me simple as that thank you all for watching see you next [Music] time