This is live footage of scammers fully panicking. Let's give these scammers a phone call and record their live reactions to a hacker revealing their true identities. Yeah, my name is Sanjie.
Your name is Sanjie and your friend next to you is wearing a brown shirt. So Sanjiv, why are you scamming people? Sanjie Sanjie.
[Music] Oh yeah, this is definitely it. They're taping it forever. All right, so I'm going to explain to you how I found these scammers.
I was doing my usual look around for scammer phone numbers when I came across a list of websites that looked very scammy to say the least. The website looks fairly tame and legit on the surface. But in reality, it's all a scheme to get you to pay for useless drivers or security.
But who are the people coming across a fake website that's offering Alexa support? Well, someone who just purchased themselves a brand new Amazon Alexa device and when they tried to set it up, the instructions inform them to download the Alexa app. So, they go on Google and search something up like download Alexa app, but instead of coming across the Google Play Store or the App Store, they get those fake sponsored scam links that I showed you previously.
Now, on the website, the victim is given multiple options of download. I'm using Windows, so I go ahead and initiate the download for Windows. And I get this fake looking progress bar.
And after it loads, it gives me the exact same error message every single time reading network error. We couldn't complete your download. Please chat with us for more info.
And under that, a little option to join the chat. At this point, I know exactly where this is going. As soon as I join the support chat, the scammers will ask me for my name and phone number for a call back to my cell phone.
Once they have me on the phone, they will convince me that I need to install remote access software for them to fix the issue. And I do the one thing that you are never supposed to do. I let them remotely gain access to my computer, but while they attempt to connect to me, I am actually connecting back to them, reversing the access onto their computer.
What is that? Let me just show you. I don't know where the ID is.
Look over here. Do you see that here? What is that?
These are the people who are connected with your computer, sir. They're connected with my computer right now. Right now, the scammer is connected to my computer, but I've actually connected right back to hers, and I'm watching her computer screen as she attempts to run the scam with your devices.
Yes. And in order to do that sir, in order to install the device drivers and to make sure that they work fine on your computer and there'll be no trouble in the future, uh you how long you want the driver. So you want it for the 2 years, you want it for the three, five time.
Now while the so-called issues on the computer are actually completely normal and everything the scammer has told me up to this point has been a lie. You will now try to pitch me one of their bogus support plans. Oh, okay.
And what's it called? Okay. So I see the price here says $299 for two years.
Then I see 300 for the protection of your phone. Yes. For thus it is the protection on your devices as well.
For example, if in the future somebody gets connect with a computer or your IP address and they try to do anything bad activity on the devices of yours. They won't be able to connect with you. So okay, wonderful.
So that's all. All I have to do is pay for the security and all those problems will stop. Uh yes.
But there was not a single problem in the first place with this fake virtual computer that I created 10 minutes ago. And honestly, I wasted enough of this scammer's time. So, I decided to confront her about the scam.
Yes, sir. Do you want this driver? Do you want this security or you don't want this, though?
I don't know. Some of those services were supposed to be running there. Some of them are supposed to be stopped.
Some of them are supposed to be running. And you're telling me there's something wrong with my computer? I'm starting to think that you're a scammer.
Are you a scammer? Why would I be scammer? It sounds like you're a scammer.
Why are you disconnecting from my computer? You fake scammer. That's what you think, sir.
But that's the truth. You know you're a scammer, right? That's not the truth.
All right. So, where are you located right now? Where are you located right now?
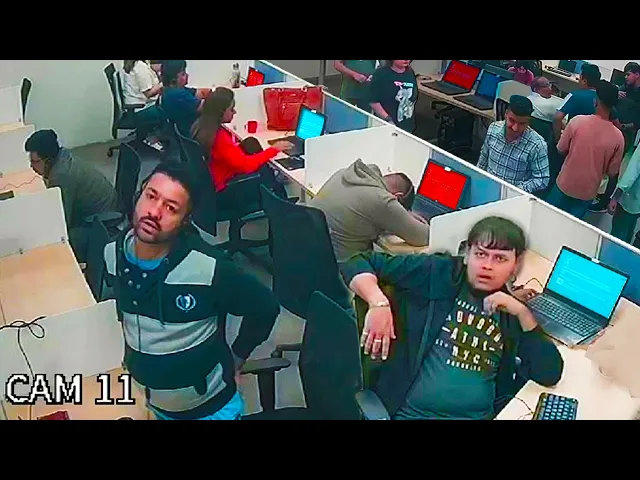
So, while that was happening, I was silently taking a look into this scammer's network. And that was actually when I found the set of CCTV security cameras, guess the password, and could see everything that was going on inside of this massive scam call center. These cameras gave me an insight into the day-to-day lives of these scammers and gave me a good sense of what the call center looked like and what the layout of the building was.
The first thing I wanted to do is make a mini map of the call center. In total, they had 12 camera views and by doing a simple headcount, I could see that there were around 15 to 20 agents usually on the floor at once. I spotted them many times eating and socializing just like in any normal job.
Now, while I gained access to only one machine in this call center and just breached their CCTV security cameras, I didn't know how I was going to further advance my investigation in proving that these people are guaranteed scammers. I had access to their cameras, but they didn't have a feature that allowed me to listen into the audio. And even if I could listen into the audio, it would be very difficult for me to record any scams.
The scammers were actually nice enough to have call recording on their phone system switched on. But even better yet, they had an application on some of their machines by the name of Flashback Recorder, which is an application that not only screen records the actual desktop display, but the microphone connected to that computer. Now, yes, I can match the timeline of the audio to the timeline of the CCTV's internal playback to watch scams that have happened in the past.
But the scammers have made it even easier for me by not using any traditional phone systems, but rather virtual ones. I ended up getting access to a couple more machines in this call center which allowed me to get some rock solid evidence of their activities. Okay, that is also not working as giving me the same error message.
Can't re can't reach this page. Ma'am, I'll do one thing for you. I'll guide you some steps on your computer.
Please follow it. Let me connect with your computer remotely and I'll set it up for you. Would that work?
That's fine. That's fine. So, this victim followed some random stranger's instructions and installed a remote access tool on her computer.
Now look at here ma'am can you see there are number of services which is stopped right now network connectivity network assistant by any chance did you stop it ma'am most of your services are down right now that connect your smart devices together and that's the reason you're having this trouble uh with the network ma'am so let me do one thing for you let me put a proper scan on it so we can get the result why it's saying it okay I think I've now heard enough of this and it's now time for me to warn this person about the scam hi Hello. Hello. Yes.
Yeah. I just wanted to ask you, were you on the phone with a gentleman that sounded Indian a second ago? Yes.
I wanted to tell you, ma'am, that person wasn't from actual tech support. I deal with fraud. Like he was a scammer.
He was trying to like ask Yeah, I took that when he was trying to download stuff on my computer. Yeah. Yeah.
I just like I wanted to warn you for the future. Like if someone ever tells you to install something like that on your computer, it's like 99% always a scam. Okay.
Thankfully, I was able to successfully warn that person about the scam. But there were many more people who had previously been scammed before I had a chance to intervene. This was evident from the many photos I downloaded from the scammers computers showing payments made via credit card and checks anywhere from $100 to $1,200 or even $3,000 for absolutely nothing.
This photo in particular that made me really disgusted with these scammers, showing how they forced an elderly looking man to open his webcam, write a check for them, and send it off to some random shell company in the United States. This is not only why I wanted to identify the heartless scammers in India, but also the people facilitating the laundering of money because processing checks internationally is far more difficult and could arouse suspicion. The scammers will instead have their victims make them payable to shell companies in United States.
There are many such companies involved in the scheme and I've blurred their names because I've reported all them to US federal authorities where they're being investigated. The information on those checks contain the types of details that are very suitable towards data brokers. Data brokers sell your information to scammers and anyone else who may want to target you.
Your full name, email, home address, health records, your relatives. It's all out there. That's why I've been using Aura, the sponsor of today's video.
Aura shows me which data brokers are selling my information and automatically submit optout requests for me. Cleaning up my information not only helps reduce the amount of spam I get, but it protects me from hackers who could use this information to help them access my social media accounts, bank accounts, or other sensitive information. I don't know if you saw this, but AT&T revealed that over 73 million customer records, both existing and former customers, were released on the dark web.
They recommend those affected, use strong passwords, monitor account activity, and consider credit freezed or fraud alerts from credit bureaus. Well, Aura does all this for me. And best of all, I don't have to download several different apps just because a company couldn't keep my data secure.
If my info was compromised in the AT&T breach, I wouldn't worry because Aura is always on and always doing the hard work of keeping me safe. I value my privacy and I value yours, too. So, you can head on over to or aura.
com/nano on any web browser and my link will offer you a 14-day free trial, which is risk-free with or a 60-day money back guarantee. Anyways, I can't show you the business names that I reported to law enforcement, but what I can do is try to get the identities of every single person working inside the call center in India. My first approach was taking a look into the scammers files in their computers, but this would turn out to be unsuccessful as they mostly only stored scam related documents and not really any personal information that led me to identifying who they were.
At this point, I didn't really know how I was going to get the information of all 30 of these employees. But that's when I noticed someone on one of the camera views in a separate cabin. This individual is a she would turn out to be one of the HR managers working in this call center.
And my proof of this is that the room she operates in literally has a sign that says HR room. And this is where I actually used the CCTV cameras to my advantage. I simply watched the cameras until Omnit would come into the office, waited for her to take the laptop out of her bag, watched her connect to the hijacked internet that I had access to, and then I was able to pivot to her computer directly.
On her computer alone, I downloaded over 500 files containing confidential data. I can tell you this because the first few files I clicked on had things like employee resumes, photos of their ID cards, even pictures of the scammers themselves, and finally a spreadsheet that contains all of the agents and managers personal names, phone numbers, email addresses, and the exact location of where they live. This is a big leak into the company's employee data.
And the reason the HR manager would store the scammer's ID photos on her computer was because these scammers don't use traditional keys to enter the call center, but rather access cards. Here I can see the HR manager using the portal to request a new access card for one of the agents. It says she's using an account owned by someone with the name of Beu.
And we can see a company name on the left side that reads Skyailer Ventures Private Limited. And if I do a quick Google search of that company, the first thing that comes up is a scammer. info post that was created back in November of 2021.
The information listed on that post were things like the director's names of the company, Beckat Rora, and Rajatma. And where have I seen those names before? Well, I saw it 10 seconds ago on the HR manager's laptop when she logged into the portal to submit the access card.
And at this point, I already found public records of these two scam fraudsters registering Sky Sailor Ventures Private Limited back in 2019. This would turn out to be the real Indian company. So, here I could confirm that Raj and Beck were at a scam call center in Punjab, India.
And if you still don't believe me, I went and found Rajat's LinkedIn account, which showed me a photo of how he looks like. And what do you know? The HR manager has a photo of someone on her hard drive that looks very similar to the profile picture on LinkedIn.
This is Raj. Now, it was time for me to pivot my access to the people who actually manage all of the finances and bookkeeping. Okay, so these agents, when they reach the finale of their scam, they open up their remote land chatting tool and pass the victim information over to someone by the name of Chavi.
I'm pretty sure this guy manages all of the financial data in this call center. Let's put his name onto Google and see what comes up. Okay, so I see a LinkedIn profile.
Let's click on this Javi. Yeah, that's definitely our guy. Look at that photo.
Okay. Yeah, he's the operations manager. We definitely need to access his computer.
So, after a couple of days of me just waiting and waiting, I finally got access to his computer. I won't tell you how I hacked this computer since I want to use the same methods in the future, but I pretty much got the keys to all of the financial information that you could imagine. I'll talk more about that in a second, but I realized I didn't even need to gather more information on Shiai because when I downloaded those 500 files worth of confidential employee data off of the HR manager's computer, I got all of his info in the process.
I have his personal information sheet, his Indian identity card or Aadar card and multiple snapshots, including this very clear photo that matches up perfectly with his ID card and his personal LinkedIn page. Finally, it was now time to extract all of the data on his computer. And let me tell you now, this guy had access to everything.
I could see the payment databases, the Stripe accounts, and even the scammers creating the invoices on PayPal that they would directly send to their scam victims. Of course, if the scammers were already dumb enough to let me see all of this, surely they would be dumb enough to not set passwords on their confidential spreadsheets, right? Well, let's find out.
Okay, let's open this. Ah, dang. Looks like we can't access their master tracking spreadsheet.
Oh, wait. I suppose if I have access to their internal cameras, I could just watch them type the password to the spreadsheets live on CCTV. H if only it was that easy though.
Actually, it was that easy because I exported over 250 clear text passwords from the scammers their computers. This gave me direct access to all of these accounts. And the first thing I did was log into these accounts and silently export all of the transactions that had been initiated on Stripe and PayPal.
That's when I noticed these scammers are even dumber than I originally thought. Raj, one of the directors and key players of this operation, used his real name, phone number, and personal email address to set up this fraudulent PayPal. This guy who thinks he's tough with his call center and illegal scams put his real name on this PayPal.
Congratulations, you played yourself. This allowed me to trace the scam payments right back to his Indian bank account. Finally, I gained access to their simple invoice page, which revealed how much money they have stolen between the years of 2021 and 2024.
Each month, these scammers on average steal around $100,000. And in the time span of just one year, they steal over $1. 1 million.
If we do the math of how much money they have stolen over the course of three years, it would be exactly $2,785,728 just from US and Canadian citizens. So, if I had all of this information, what else was I missing? Well, I still had no idea where the scam call center was located.
I had access to two outside angles on the CCTV that gave me a look into the entrance of the call center. On one of those views, I could see a security booth and a little road, but this scam call center has Wi-Fi in and outside of the building. And by using the names of the wireless networks as well as their strengths relative to the scammer's computers, we can precisely determine where the scam call center is located.
And when I put those coordinates into Google Earth, I get zoomed into this location in Mojali, Punjab. When you enter street view, you can see Villa Verde residential tower Cork City. And then this text over here is too blurry for me to read.
Uh and then some more Cork City and then the atrium Cork City. So, I thought this security booth right here was the same one, but if we actually compare it to the one on the CCTV, they're actually just completely different. So, at the beginning, I thought this building on the right was the actual scam call center, but it's not.
So, the actual location of the scam call center is towards the back of the building. So, if we do a quick zoom in, we can see on the left side over here, that's the the security booth. So, let's take a look at the CCTV, and that's the same.
And if we look on the right side, we can see the parking lot. And on the left side, we have that turn. So I believe the scammers are in this building right here.
So these scammers are located in the atrium Cork City building of sector 74 phase AB Mojali Punjab. When I put that address into Google, the first result is the official corkcity. com website which is the exact same website I saw the HR manager using previously.
I very quickly found this YouTube video giving a tour of the building and at first I recognized the entrance from Google Street View imagery. But when they brought the camera to the back of the building, I was 100% able to confirm the location of the call center. In this frame right here, they even got a shot of the entrance, which matches up perfectly with what we can see on the CCTV cameras.
So, these cameras are located in this very high-end building. As stated in the description in this video, the building has a ton of amenities like a massive swimming pool, a full fitness center, CCTV security cameras, and a 24/7 on-site security team. I wanted to identify if any other people have dealt with this call center in the past.
And while looking at many reviews made by previously scammed victims, I actually remembered that I picked up a password to the scammer's Better Business Bureau account, allowing me to have full control of all of the reviews. No, I want to like respond to every be like, "Oh, this is a scam company that we Oh, we we actually Sorry. Want your money back?
Go to your bank and ask for a charge back. I'll actually give you the director's name while I'm at it. " Yeah.
Here's his personal phone number. Here you go. So that's exactly what I did.
I replied to all of the people agreeing with their statements and even confirming that they are indeed a scam company. And at this point, I had gathered pretty much all the evidence I needed. I had the names of the bosses and most of the employees.
I had their exact location. And finally, I was able to trace the scam payments right back to the managing directors. Instead of just watching them and doing nothing, let's rather engage in some sabotage.
The first thing I did was report the scammer's Google AdSense account so that nobody can find their website anymore. Then I decided to report the website itself to GoDaddy so that no victims can access their chat support and phone numbers. Thirdly, I reported the scammers their service agreements to DocYsine.
Next, I sent all of the scammers any IDs to my friend Matt who works at Anyesk and he managed to ban all of them permanently off of the platform. And Rajat, I reported all of your personal information to the FBI as well. Good luck trying to scam now, buddy.
Finally, I logged into the scammer's PayPal account and manually started to refund each one of their victims. Of course, this process would take way too long, so I reported their fraudulent accounts to PayPal themselves, who then responded by banning their PayPal account. No more direct debit payments for them.
In late December of 2023, the scammers actually removed the CCTV cameras off of the main network that I had access to, ultimately killing my visual view into this call center. But the scammers forgot about one critical thing. I could watch them through the laptop webcams.
Well, kind of. These scammers actually taped up most of the laptop webcams in this call center. So, I unfortunately wasn't able to call any of the scammers directly looking at their face, but maybe I can confront them from a different angle.
No one really uses this computer right here, and the closest people sitting next to this computer are these guys. So, let's give these scammers a scare by revealing their true identities on a phone call. Yeah, you speak to one of my superiors.
Okay, hold on. Okay, let me speak to him. Yes.
How may I help you? Yeah. So, I I bet I can actually guess your name.
Yeah, my name is Sanjie. Your name is Sanjie and your friend next to you is wearing a brown shirt. So Sanjiv, why are you scamming people?
Sanjie, what? Yeah, your name is Sanjie. Yeah, your name is Sanjie.
Yeah. Yeah. You know Chavi Go, you know Chavi and Rajat, you know Rajot.
Rajat. Yeah. Yeah.
Ait, the HR manager. So Shan Sanjie, let's let's talk for a bit. You know I can see you right now.
Wave at the camera. You see the CCTV camera. You see the cameras right above you.
Look up. Look up at the CCTV. Sanjief.
Sanjief. Look at the CCTV. Look at the CCTV.
Sanjie. No. No man.
You are wrong. No, I'm wrong. So, you're running scams, right, Sanjief?
You're running scams. No. Yes, you are.
Yeah. What? I can tell you your job.
Your job is to manage all of the chats. So, like the people send you the chat and then you give it to the So, so how are you not the scammer? Explain to me how you're not the scammer, Sanjief.
Explain to me. No, no, no, no, no, no, no, no, no. You are wrong.
Are you panicking? Yo, the HR manager is right next to you. Hello.
Yeah. Yeah. Can you please pass the call back to David or not?
I am like I mean you are already talking to him. Oh, I'm speaking to David right now. Yes.
Oh, okay. So, David, you're wearing a brown shirt right now, right? You're wearing a brown shirt.
Like, look behind you. You know, so you know Skyfair Travels. Look at the CCTV cameras behind you.
Like, you know, like look behind you. I don't know what you're saying. Turn around in your chair.
Turn around. He turn around like I'm looking at you. Turn around in your chair.
No, bro. Turn around. Oh, he's getting someone.
He's getting someone right now, I think. At this point, Sanjie, the scammer that I just confronted, decided it would be a good idea to tell the boss Rajot what just happened. Earlier that day, the HR manager conveniently left her computer in Rajat's personal cabin, which allowed me to grab this webcam footage.
You are you are I know human is all chat You all chat. [Music] I said [Music] you are Sanji. [Music] After this conversation, the HR manager entered the cabin and she unfortunately grabbed the laptop and took it back to her office.
When she made it back to her room, they finally told her everything that had happened. Due to a technical issue, I wasn't able to get audio to this portion of the confrontation, but we can see the HR manager, ANT, looking visually concerned when she notices her webcam light is on as well. Of course, she doesn't know anything about computers, so she leaves the room to grab someone with more experience.
When she comes back in, we can see her point directly at the webcam. Sanji, the person we can see right here, tells her it might be a good idea to put some tape over the webcam. Fortunately for us, this is the HR manager and not the IT guy.
So, instead of taping the actual webcam itself, she taped the webcam light instead. As for the main room, everyone was sort of in a panic mode with a ton of people looking pretty concerned. Here we can see Chavei, the operations manager, holding a piece of tape and then pointing straight at the webcam.
I assume you can guess what's coming next. Shut down. Oh yeah, this is definitely it.
They're taping it forever. [Applause] Why are you guys smashing the laptop or they're smashing the laptop? and the scammers lived miserably ever after.
If you guys did enjoy this video, make sure to like and subscribe before clicking off.