Foreign thanks everyone for joining in for this webinar on data privacy certification preparation and it's a continuation of yesterday's session uh where we discussed on the cipp E certification and today we'll be discussing on the cipm which is certified information privacy manager so we'll be discussing on cipm the uh today's session is on the preparation for data privacy Certifications and focus of today's session will be on certified information privacy manager and so about infosec train so we established in 2016 and we are one of the finest security and technology training and consulting company uh uh
so we are happy to announce that we are the official training partner with iapp and with this partnership we'll be able to provide all the official certifications from iapp which Includes cippe which is certified information privacy professional and there are four different variants to that which is cappe Europe and cap us cap Capp Canada and Capp Asia and these are four different variants basically uh targeting the specific law of the land which is the gdpr of Europe and we have Canada specific pipda and then we also have Asia variate and uh and the US1 which
is focusing on the regional laws so this is the first uh certification Which we discussed yesterday which is cappe and there are two other certification which is cipm and cipd our Focus area for today's webinar will be on cipm and infosec train has now partnered with the world leading information and data privacy organization IEP and this this gives us the opportunity to provide our audience with a few of the most on-demand certification which is presented here This is our trusted clients some of the big names over there and uh one important question like why infosec
green uh so we have certified and experienced instructors including me and flexible modes of training access to the recorded session at any point of time you can go back to your own pace and uh and revise the content post training completion we always support you with your queries and we are always there to help you out with exams So coming to the agenda uh today we are targeting on the CI pm and uh we'll be looking into all the 10 uh chapters which is which is prescribed part of the curriculum of cipm and we'll also
look into the exam exam prep discussions and data privacy interview questions and uh plan for preparing and clear cipm inside two months cibm course materials so the first chapter one so just to make it very clear uh today's session will not be Able to go in entire depth of all the 10 chapters and what we are going we are going to give a precursor of what you can expect during our course okay and during the session I'll try to give you overview about certain topics and uh it it is making you understand what you will
be expecting in the course and what are the contents at the overview you will be uh you will be able to understand during the uh during the actual course which is planned later on So the first chapter is about introduction to privacy program management and uh just to uh just to again recollect today's session is on cipm which is privacy program management and yesterday was uh cappe which is privacy professional targeting the gdpr and once you have gdpr uh understanding now we are moving towards how do you manage privacy poster of an organization and the
first and foremost is understanding in in any privacy program Management is these key features which is what is the responsibility of a privacy program manager and what are the accountability requirements which any privacy manager needs to fulfill for an organization and Beyond laws and compliance what is your day-to-day responsibilities how do you how do you add value through privacy for an organization and why does the organization needs a privacy program that needs to be very clear and and Privacy across the organization because privacy is going to cut across multiple products and services where the Privacy
requirements needs to be embedded and awareness alignment and involvement so in chapter one we are gonna see uh some of the fundamentals of privacy program management and uh with that I thought we'll touch upon certain very important topics as a Basics okay so a lot of people still have a question on what is privacy right Privacy itself has variance okay privacy can be about the data about a body and sometimes it can be specific to specific to what you are dealing with right and here we are more focused on data privacy and the Very definition
of privacy itself is not defined anywhere and that is the reason uh and the the specialty of privacy because you cannot confine what is privacy because the roots of privacy are coming from Human Rights international human rights and it varies Depends on the situation depends on the context of where we are referring privacy right on a higher level just for everyone to understand what is privacy it's a right to be left alone and not into including someone's personal and family life so the origins of these statements starts with your United Nations uh convention on human
rights where they where they came up with all these uh specific human rights related to data privacy and that's all Consequence of the second world war right and uh specific to data privacy it's it's a right of individual to control and protect this personal data processed by an organization so this is our Focus area for the entire course and we'll not be dealing any other aspects of privacy so data privacy is what we are going to focus on the entire cap and capm perspective okay so uh now the interesting question is what is data privacy
and data protection sometimes uh A lot of people uh mistake the synonyms between privacy and information security or privacy and protection but there is definitely a lot of differences and deviation although there is they are they are interrelated in a lot of ways but they are two different concepts uh so data privacy and protection uh is often confused terminologies and as I said privacy uh routes back from the rights uh human rights specifically and uh and as I said it originates from the Loss and it originates from The Core Concepts of human right uh so
we were at data protection and data privacy terminologies as I said data protection is a key enabler for data privacy and in data protection we are more concerned in terms of how we how we will protect the data and ensure the confidentiality integrity and availability of the data but in data privacy we'll go One Step Beyond it uh we will be looking at why are we collecting this data and what are We going to do with this data what are the rights and control that we are going to give to the data subjects from whom
we collected the data so this is how you actually explain data privacy concept to anyone so it is your data and how you have control over your data and how do you ensure that uh you your control is being maintained by the uh has been ensured by the organization the organization respects uh your uh your your value of the data right and that is That is a core concept of data privacy itself and coming to privacy program management so privacy program management is is a whole uh framework or uh uh a method in terms of
combining a structured approach of combining projects into a framework and life cycle life cycle to protect the personal data and the rights of the individuals so we have lot of Concepts embedded with data privacy and protection but uh if you ask privacy program management it's nothing But a structured approach of how do you embed privacy at at the data life cycle right from the onset of collection uh in terms of processing the data in terms of archiving it in terms of deleting it or in terms of uh in terms of disposing it completely and how
do you embed the data subject rights into this entire life cycle is all a structured approach of privacy program management and it's one of the enabler to comply with legal and regulatory requirements meet the Expectation of the client or customers while at the same time prevent and mitigate privacy risk so that's a sole objective of any privacy program management of organization so a clear differentiator is that you don't always look privacy as a compliance perspective it is also one of the key enablers in terms of uh meeting the trust of the customer getting the getting
the customers trust is one of the key objective of ensuring data privacy and That's going to be the differentiator between companies in next 10 years whoever is not respecting data privacy in their Core Concepts are definitely gonna get a lot of problems losing customers trust and also getting the uh legal and Regulatory penalties moving on what is a framework framework is a skeletal structure that is needed to support the program management people who are familiar with the framework look like covert and and other Frameworks Which are there available in the market essentially uh will use
the same concept here and we will create a data privacy framework and each organization privacy program framework will be created by analyzing its applicable loss the regulation and best practices that are tailored for the goals of each organization so creating a framework is completely depends on the law of the land in terms of the company subjective companies uh companies practices and That is how you create an effective data process framework and privacy life cycle it is a series of stages of personal data passes through in any organization the Privacy governance life cycle includes assess protect
sustain and respond basically you're gonna you're gonna determine what is uh determine the personal data aspects in SS and you're gonna implement the controls to protect it and you're ensuring uh the controls are protected and the rights are Respected and sustained and then finally respond is your if you if you come across any threat how do you respond so this is uh this is how the capm course is also uh uh is being sectioned and uh the courses uh actually divided into these four parts which is assess protect sustain and respond okay so these are
General introduction I just wanted to brief you about these aspects and You by uh people who have attended today's session uh will Now Understand sorry yesterday session uh would Now understand how the uh the course is completely different from what we studied yesterday because yesterday session was completely into gdpr uh Focus which is into laws and regulation now we are moving into how do you protect uh personal data in any organization without understanding Cape directly come to coming to cipm is going to be challenging because that's where we study what is a personal data Sensitive
personal data always a controller who is a processor who is a joint controller so that's the uh that's a key differentiator I've been telling to a lot of people a lot of people had this question cipp E versus cipm and I always give the same advice have your foundation very strong and that is done through uh targeting CIP E when you have gdpr a strong basis then you can build on top of it with cipt and CIP so that's a natural progression that uh that I Always suggest to all the candidates who want to take
up a career and data privacy so moving on uh so done with the sort of fundamentals or basics of privacy program management uh in general I uh I wanted to introduce you for the responsibility of privacy program manager again this interesting question a lot of people came up with this question yesterday like what will be my day-to-day responsibility what will be My work in any organization if I take up this particular career so this is even part of the curriculum as well right so your your job role will always starts uh from as a state
for example if you are starting this program from scratch okay uh then you need to understand the business landscape right and understanding business landscape varies from sector to sector operations to operations right so every particular sector has its own Nuance of operations Right so in that case understanding the business landscape becomes very very important because uh a General application of a control will never be effective unless we understand the gravity of the operations that is there different types of data collected the data is processed in a different way to multiple sector for example a school
collects personal data of students versus a hospital collecting the sensitive personal data of uh of the Patients have a different set of controls to be implemented the range of the range of sensitiveness is very high in a hospital so the amount of controls which needs to be there has to be very high that is where you need to understand the sensitiveness of the operation that is the first step of any privacy program management to understand as a state and understand the business uh understand the business landscape and there are different types of data that Is
dealt by any organization or identity it could be your customers data it could be the employees data and it could be your Windows data as well a lot of people don't sometimes uh understand when does data could also be a personal data right if your organization having vendors then possibly their personal data is also collected some of the vendor Management Services or vendor management transactions you do their personal data is also brought into your System so you should be aware of all these nuances to have a effective privacy program management and the second important step
is to identify a legal Regulatory and contractual requirement this is a fulcrum and basis for any uh program management Let It Be information security or data privacy you need to have a thorough understanding of your law of the land your regulatory requirement if you are for example if you're operating in a banking uh in India you will have your sebi and you'll have RBI requirements all these things comes part of a regulatory and contractual requirements again you will have contracts with different vendors from different service providers all these contracts needs to be also respected and
documented so these requirements will also become very effective and the requirements needs to be monitored periodically and implemented and that is where you will Also understand one of the key responsibility whether the organization you're working is a controller or a processor or a join controller so there are three different variants where you will take the rules for example I Define I am an entity and I Define the purpose of collection as well as the ways and means of collection then I am a controller of the data and a good example is for example your as
a bank bank I am asking the data of all my Customers while opening a bank account so I take up the role of a controller but there are services within the bank and that can also work as a joint controller for example a credit card department is there the credit card department together with the savings account uh Savings Bank Department jointly Define the purposes they both become join controllers so for the same purpose we have a card printing facility as a vendor and the vendor only works on The instruction given by the bank to just
print the card but in this process there is a personal data being transferred to them and they work on that personal data they assume the role of a process so this is how a controller processor and a joint controller uh the responsibilities have to be identified and it needs to be identified for uh separately for each and every process for uh instances some places you might play the role of joint controller in Some instances you might play the role of a controller so that is where this understanding needs to be very clear and identified and
documented so the next important step after identifying the requirements are performing The Gap assessment and identifying the existing privacy risk so it's a gap assessment basically and every Gap assessment the idea is that you will see your legal Regulatory and contractual requirements and see uh Whether we are complying at the current poster what are the gaps and then just document it so that Gap assessment give gives you a clear poster in terms of how do you plan the Privacy program rollout as well as the controls needs to be that needs to be implemented the next
step is that review update and develop Enterprise privacy framework along with designing policies procedures and templates so once you've done did your Gap assessment and by then you would Have understood either there is no policies or the policies are inadequate or they are not reviewed in a periodic fashion so all these are privacy risk and you need to address them by either creating the policies are fresh or updating them and keeping it up to date and then finally reviewing it period periodically and getting getting it signed by the appropriate authorities within the organization so this
is the next important step and then identifying The Privacy organization structure again a very important uh point because without resources without having organization structure managing this complex data privacy issues will never be feasible because you are gonna have uh the the concerns coming from different Corners one data subject can be rising issue which is your data subject rights which needs to be fulfilled within a period of time for example within if your work if you're Operating in European Union region it needs to be it needs to be responded uh within two months okay the initial
period is one month plus extension of one month is provided so maximum two months so these things are very sensitive issues and that means we need to focus on resources if you do not have adequate adequate resources in managing the issues that is coming from internal as well as external then there's uh we cannot actually fulfill the organization Objective of protecting data privacy of customers right so identifying the different roles the rules can start from analyst then you can have your privacy Consultants you can have the legal department supporting the Privacy Department privacy team in
terms of the contractual requirements data privacy contracts and also understanding the legal requirements as well and then finally uh we we have someone as a data privacy manager and data privacy manager Will be reporting to a data Protection Officer or the relevant terminology which certain organizations use so in short it it it can be uh sort of replicated from information security organization structure as well like we see the different people aligned with information security team a similar structure is also there in data privacy right we have a CSU see so uh ciso has a team
within with within the structure which is your information security Manages and also you have information Security Consultants and you will also have people within the team assuming different roles managing the poster like your network security be your app set you will also have different people supporting the different requirements of information security similarly is what we have in the Privacy organization structure and next important element is conducting privacy awareness Workshop this has to uh has to start with the top Management if the top management is not aware about the privacy and the risk associated with it
if not managed properly we are gonna once we are once we are done with the Privacy awareness workshops in previous avens Workshop as I said making the organization understand the roles and responsibility of them because every employee has their own roles and responsibility in terms of privacy it's not just the Privacy team that needs to be communicated with the Organization if they don't understand it then whatever controls we have it's not going to have the benefit that's what I have seen in my personal experience if you don't people if you don't make people accountable for
their day-to-day personal data handling then any any control any sophisticated control we bring in an organization is not going to be effective so that communication that training has to be provided imparted into the organization and that will Definitely change the culture of the organization and we we look at personal data right A lot of people still don't understand the value of personal data for example if I go to any organization at a reception I see a lot of personal data collected part of the physical security but we don't really understand what happens to that paper
which with with our identity personally identifiable information which is given to them what Happens to that paper not many organization actually take that seriously right so this is where a cultural change is required this is happening in Europe at a large scale this will also happen this is going to happen in other countries as well but if you start this early and we can definitely have a lot of positive change with that so okay and next important step is in terms of developing a personal data inventory and data flow Diagrams and data protection controls once
this is done your half of the data privacy task is completed because understanding what data you have in an organization is one of the most important and difficult task as well because the personal data is coming into an organization through multiple channels right one example is I gave is a physical security and you can have data coming from your web it can come from chat it can come from emails it can It can come from so many sources for any organization it depends on the organization business model right so understanding the data flow understanding the
channels where you collect the data understanding the data flow within the organization is very very important because the data is moving from one Department to another department if you do not have a clear flow of this data you actually cannot fulfill the data privacy obligations one One classical example is a data subject has raised a request to erase his data because the the processing was based on consent and now the since the data subject wants to delete his data this data needs to be deleted across the system and which means we are going to have
a lot of problem if we do not have a clear data flow of the personal data within the organization right we just cannot go to each and every system at that point of time to trace the data That is how that is why having a clear inventory and data flow mapping very very important these uh particular topics are gonna have a lot of value in next five to ten years because there is a lot of solutions which are coming up in the market Focus focusing on this particular aspect right if we have a clear inventory
half of your headache is taken care that is what I see in every organization right so this is a very challenging part to start with but once You have a clear inventory then you can definitely uh uh take care of other parts in much quicker and easier way uh moving on uh connecting a data production impact assessment uh this is mandated if you are especially operating based out of the European Union region the terminology of bpia is coined from the gdpr term before that we used to have a terminology called Pia which is privacy impact
assessment we will see the differences during our course actual Course in terms of what is the difference between a Pia what is the difference between a dpia what triggers a dpia and how do you actually conduct a DPI so during part of the course we will be uh happy to help you in a practical way of giving you a DPI template and how do you actually conduct those dpia means I'll show you the results of a dpia as well so which will help you to understand uh how this is connected and you can replicate the
same In any organization you are taking it up so as I said our course is not just a theoretical course we'll try to bring in all practical aspects of the data privacy program and I'll be helping you with whatever experience I've gained through the course of my tenure and I'll give you those examples from my day-to-day practical experience which I am facing okay and we have uh data subject rights and which we need to manage part of the organization Obligation for that we can we need to have a system in place we need to have
people resources managing it we need to have slas defined and we need to have Ways and Means defined in terms of how DB communicate back to the customers and how do we handle that complaints in effective way so all these things are to be fulfilled by the Privacy program manager and then the last two important parts which is your data breach management and Reporting and which means This is the most critical part any big organization will always have an incident management but that doesn't always fulfill the requirements of your data breach management especially focusing on
personal data because the obligation especially if you're operating in European Union you have a mandate of 72 hours within 72 hours once you're aware of the beach you need to inform the regulators and if the breach is gonna have a high risk on the data Subject you need to inform the data subject as well this is a legal requirement so Incident Management is little different to the data data breach management concerning personal data which you need to properly structure it for any effective data privacy program management and the final step is implementing continuous compliance program
and monitoring with metrics now this looks lot of tasks isn't it so that is why I Said the the importance of this particular aspect in an organization is going to grow exponentially from here one person may not be able to fulfill even three to four tasks which is mentioned here that is why we need a dedicated privacy structure and a team so someone will be just focusing on conducting the assessments someone is focused on maintaining the inventory and someone will be focusing on the breach management someone will be developing The policies procedures and looking after
the changes and running the running the periodic audits so there is multiple Scopes within this entire Journey right as a privacy program management manager or a data Protection Officer Your Role is not to have your hands dirty at each and every task of this but to have a entire accountability for this all these tasks you need to ensure the work to be done and to be done in an effective way but you will Not be able to do each and every task which is mentioned here in any organization that's that's if it's a very small
organization maybe it's possible but in a large organization it's definitely not possible that's why you need to have a clear understanding what a data Protection Officer can do and that is why we need to always associate data Protection Officer versus accountability a data Protection Officer is not gonna go reply to a data subject Rights but rather he will ensure in a minute he is going to review the metrics of how uh subject data subject rights are responded in a month and review if the if they are meeting the SLA and provide the guidance to the
team that is what is the role of data protection manager as well as data Protection Officer okay so these uh nuances are very very important for anyone who's starting this data privacy program manager Journey a lot of questions that Was coming yesterday to understand what will be my day-to-day work I hope that is the purpose I kept the slide and the reason I explained it in this depth is because I I wanted you guys to understand and get the flavor of what we do part of our day-to-day job and as I said clearly it's not
one man's job it's entire team which will be focusing on different areas of your data privacy program management okay uh so I hope you got the flavor of uh Responsibility of privacy program manager as well as uh data Protection Officer moving on with chapter two chapter two is again focusing on the Privacy governance uh now the remaining chapter is nothing but dissecting whatever we saw in the roadmap right the the SEC the chapter 2 is gonna focus on the policies procedures having a dedicated privacy team okay and uh part of this Charter we will see
how to uh why it's important to have a dedicated Vision and Mission and having the objective these things will be derived from the overall organization objective right the overall organization objective will drill down into your dead uh into your dedicated privacy vision and mission statement right and having a privacy strategy for the organization customized to the business models and having a data privacy framework is very very important in terms of addressing uh addressing the privacy concerns in a Holistic way and we also have to define the Privacy team and the model which we are gonna
use for example as I said if you see on the right hand side we have different models of privacy governance one could be a centralized model or second could be or local or decentralized model there is one more model which is hybrid in centralized model you have one person dictating the entire uh rules and responsibility even everything that comes from a single Point and it is being cascaded into the team and that is how it is like one person deciding at a whole and it is all being followed by remaining team that is called centralized
model this is this is effective uh sometimes at at a larger organization where they feel that having different branches different indeed sub entities taking decisions will create a lot of confusions so what they do is they have a dedicated function at a central level and they decide whatever Is the required environments and they just pass the instruction it has just been followed by remaining all the subgroups and if you have a local or decentralized this is a very flat model and uh and which means a smaller organization is best to adapt these things because uh
it's a flat hierarchy everyone works together and uh and they interact with each other and it's more like a bottom to top approach and this helps uh in terms of uh more into like a Agile model where you uh try to discuss collaborate and make the changes and everyone will have certain uh certain powers or certain uh decision making Authority so they they fine tune uh the effectiveness of the Privacy program so there is a sort of discretion which is Allah which is which is there with the responsibility of the people in the team so
this is these are the different models uh which you need to understand and you need to choose the one which is Appropriate for your organization as I said in data governance you need to have a vision mission statement which will be drilled down from your organization objectives or organization vision and Mission you'll have a dedicated data privacy policy roles and responsibility defined and the subsequent process so this is a sample data privacy framework this again touches most of the areas which we saw in the roadmap uh I'm not going to go into each and every
part Of it but if you see these this is how you come up with the data privacy framework you create your target operating model your uh your program governance and you also Define the different aspects of it and this is how you ensure there's a holistic view of the data privacy requirements as well as the risk of the organization managed effectively okay and so people who are already in the information security domain you would have seen such a Framework for information security and it's it's almost the same flavor but the the way we do it
is much much different that is the that is the only that is the only uh differentiation Point okay so structure of the Privacy team uh the Senior Management this could be your board of directors or your CEO uh that could be the Senior Management and uh if for example in in gdpr you need a data Protection Officer directly reporting to the board or to the highest uh Management which could be your Senior Management right and he is a sea suit uh uh officer and you cannot make a data privacy officer as same as a chief
information security officer these These are definitely you need to have a segregation of Duties implemented there see so cannot be a data production officer if there is a requirement of data production officer by law in the gdpr region I'll discuss those new answers in detail while we take up the Course because the law says when you are doing certain actions you need to appoint data Protection Officer as a mandate in in that cases having a CSO performing a data production officer is not acceptable okay and we will also have different functions reporting to the data
protection office which we have like a communication team and uh we'll also have a team to handle the data subject rights we'll also have a team Focusing on the incident response and we'll also have a dedicated team which is focusing on the controls perspective and there are support functions which is the typical internal audit team will also cover the data privacy audits which will be mandated whenever we have law of the land mandating it or the regulator requirement or the legal requirement all these things will also will will now start focusing on privacy audits so
privacy audits can also come through Certifications for example we have ISO 27701 so that certification will now uh will become will become sort of a de facto in the market maybe next four or five years uh not after four or five years for the next four or five years it will be very hot because a lot of organizations are certified with 27001 and what they might think us how to how to ensure data privacy uh how to give that sense of a trust to the customer is that maybe they may go for 27701 right so
then the internal audit department will become an important tool in terms of managing those audits obviously they need to work in collaboration with the data privacity and we'll also have the legal team the legal Team Works on uh uh your contractual requirements you uh inferencing the legal requirements whenever you have queries in terms of interpretation of the law all these aspects are handled by the legal Department it's always best to have their opinions regarding certain complex issues especially in terms of interpretation of the law or in terms of handling certain specific complex issues like a
problem with the customer or a problem with the vendor and what is your legal solution to it all these things should always be should be consulted with the specific legal department okay so that is all about chapter two and uh we are moving into chapter three and Chapter three is about the next aspect which is privacy program management in privacy program management as I said uh you need to have a dedicated privacy framework or sorry uh the chapter 3 is privacy program framework and part of the framework very important aspect is to understand the laws
and regulations right especially if you are a global organization being a global organization you are going to operate in multiple uh geographies understanding the Cross-border data transfers is very very important what are the applicable international data transfer tools for example if you're operating in gdpr region European region you might have a standard contractual Clauses SSC and you'll you will have a consent as one of the mechanism and we also have adequate adequacy status which is given by the European Commission and you also have certification schemes which also is a instrument to do international data Transfers
so understanding these aspects part of your privacy framework is very very important documenting them and periodically monitoring the changes with the laws and regulations and informing the concern team about the role regarding those changes in the logs so this is very important especially if your organization is working on a global scale uh just an example of uh so in this chapter we will also look into the uh a gist of different data privacy laws That exist in the world and their Essence in the organization but we don't need to memorize each and every aspect of
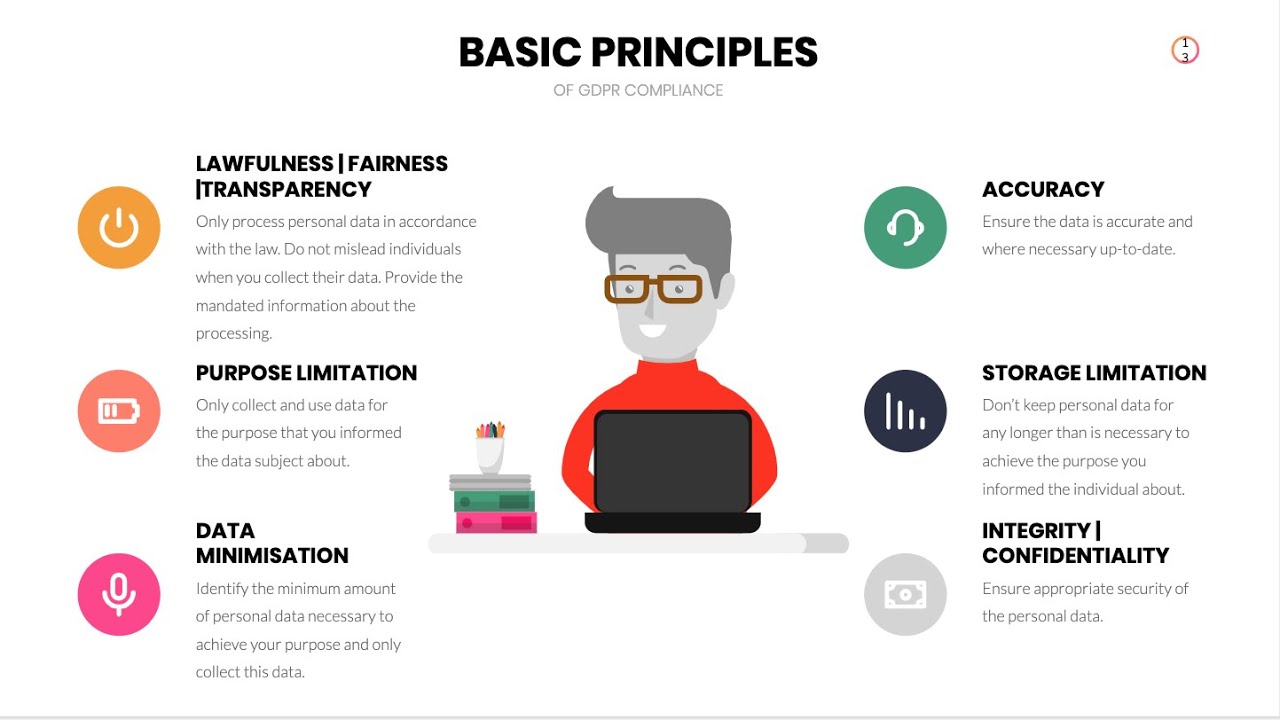
it but we need to have a good understanding and as I as we as I usually say if you understand gdpr uh uh to a good extent it's only a matter of inference with any other law because 80 percent of the global data privacy laws are the same their uh differences could be in terms of the rights which are available the penalties which are Available the principles might slightly change and this is it but 80 percent the Crux of any data privacy laws are going to be the same that is why it's very very important
understand one uh law and regulation in complete depth and then you can easily manage the other requirements it's only a matter of inference okay so it's just for your view if your company is operating in a global level you can see there are multiple laws which you need to Incorporate and look after okay as I said if you are doing uh international data transfer and uh there are uh this this slide is focusing on the uh you European union gdpr and as I said there's adequacy decision which is focused on uh special status given by
the European commission and with that status you can uh go ahead with the international data transfer and also having appropriate safeguards which includes your standard contractual Clauses approved code of conduct and privacy Shield right now privacy Shield has been invalidated and there is a special agreement between the U.S and the European region they are coming up with a new framework so part of a curriculum we also discuss on these elements what are the recent changes which are happening how do you handle for example your company is based out of us and you are working for
uh data privacy requirements right you Definitely need to know the current changes which is happening within this particular sphere between Europe and U.S what are the current changes happening in terms of their instruments to do a data transfer okay and next uh instrument is binding corporate rules this is another important element if you're a global organization and you want to do intra group transfer important word is intra group it is only within the group You're gonna transfer the data but the group is present across the geographies for example a Indian based company uh as as
multiple branches across the world but every Branch will also be considered as a sub entity and they will they are registered in different countries which means they need to be bounded by that law of the land so in this case what happens is if you have a binding corporate rules which means it allows the intra group or data transfer but all These things are referencing to gdpr framework okay I'm just giving one example because if you understand one concept clearly you can then just infer to that particular law of the land okay and exemption exceptions
are clearly the uh you need to get the consent or maybe uh contractual obligation to the individual or the vital interest so these are some of the legal basis to do international data transfer and the focusing on gdpr So those those are the elements of your privacy framework especially focusing on the cross-border data transfer so the next chapter is going to be focusing on data assessments so data assessments uh again is going to be uh two parts one is your uh which is mandated by gdpr which is your dpia and if you're operating in different
geographies it could be a requirement of Pia which is privacy impact assessment and there could be other assessments which is also required Part of a data privacy management which is your vendor assessments Okay so a part of these elements you need to have inventories and Records you need to have a ropa which is especially a specific requirement article 30 of gdpr which we call records of processing activity which is called the ropa which is nothing but a data flow mapping with an organization okay and so these are assessments part of chapter four and this is
just an overview of tpia Which is data protection impact assessment which is specifically called out in gdpr and where we need to do this assessment is whenever any processing activity is gonna process a high risk in that case you would definitely need to do a dpia assessment and gdpr clearly calls out what are the things that needs to be called captured part of dpia we have different uh Regulators who are like the Ico information Commission office from the UK and we have aepd from Spain uh we have different Regulators in the GDP in the European
region especially coming with uh uh specific templates how do you conduct a dpia or they help you to uh incorporate the Essential Elements of DPI okay so we will be looking into these elements in detail whenever we are conducting our sessions and so just to make it very clear DPA foreign just to make it very clear dpia is Always a terminology associated with gdpr do not confuse it with Pia pia has been long been existing in the data privacy relin and it is it is there long before uh gdpr was there and dpia is always
associated with the gdpr okay and uh there are a lot of differences associated with it also because there are certain triggers that calls for dpia and there are certain triggers that calls for a pi during our actual course we will look into these aspects in Detail I'll also share the templates of how what are the elements that needs to be captured part of these assessments and can also show you a filled assessment which will make you completely understand how do you carry out this activity on your own whenever you pick up these rules Okay so
as I said this this entire uh course I have uh we are I'm gonna do in a very practical way not just telling you the theory aspect So this is ropa records of processing activity uh records of processing activities basically you're gonna record every data life cycle event of personal data right from capturing the collection of data how do you capture it and what was your lawful basis to capture it and what was the purpose for collecting the data right and what are the categories of personal data you are collecting it and you are also
gonna see what are the security measures uh what are the Retention rules applied and if there is a transfer of data to processor or international data transfer or involved in this case so in this case we are gonna look into the recipients who are going to receive the data all these aspects are uh important part of the records of processing activity so I can also show you a Roper template part of this course you can you can understand and appreciate it so this will be one of the Very important activity we'll be doing part of
the data privacy manager root and uh so very important activity which you need to understand what are the essential elements to be captured part of the records of processing activity this is this is nothing but your data inventory but specifically focused uh which is coming from the gdpr okay a part of the same activity which is DFD which is data flow diagrams so this is just the inventory of your personal data Now you show a personal uh data flow of the personal data right so this is again just for illustration okay if you see there
is a data subject information which is collected through website there is a collected through retail point of sale phone orders or mail orders and uh so again this if you are available swim Lanes how to con how to actually construct a data flow this is very similar to that just that we have certain Essential Elements to be Captured part of the personal data flow which is your stages where collection storage are processing access or transfer and then archive or destruction we need to capture them accordingly right part of the processing you collected the data and
you are storing the data in the inventory and finally uh you are still uh having the data uh stored in part of the crms which is your customer relationship management databases uh and Enterprise data virus And finally they are uh transferred to vendors if there is any transaction in board and then you archive and destroyed so this is how you do a data flow diagram for a particular process right and uh this is there are multiple tools which are available in the market like onetrust security.ai big ID lot of solutions are there which allows you
all these are proprietary softwares they are not free to use but these Solutions uh had help you really in terms of uh Having this data flow diagrams okay so this is how you do it and this is required for each and every process for you too complete so with that we complete chapter 4 and chapter 5 is about protecting uh personal information this is the cycle which is protect and here we will be looking one of the very important requirements of data privacy which is Privacy by Design privacy by data production by Design and default
and the information security controls how they supplement data privacy and the technical and organizational measures part of this I'm just showcasing you the Privacy by Design concept privacy by Design concept was first proposed by Anna chuwakin and this has seven important principles this is very very important for you to understand as a theoretical concept and then you can use Them in your personal data life cycle in an organization so we will not be going at the depth of explaining each and every principle here because they take their own time and you need to understand at
a concept level what they mean and how you can appreciate that in a implementation of your privacy program in an organization okay and they are very very important and that is also now mandated in gdpr to invoke privacy by Design in in your privacy program Management and data protection as I said uh security is one of the key enablers of privacy and so security when I say security controls uh you will have encryption network security access control activity monitoring breach response data leakage prevention and then you have your privacy oriented controls which is your Discovery
and classification access rise access rights consent concern management third party Which is vendor management data removal which is your data disposal and policies right and uh these are a very important to understand how security complements privacy you need you cannot uh Implement privacy controls in Silo and Security will always be associated with data privacy controls because they are always a key enablers to in enable us for data privacy implementation right and uh so that is where you will uh understand the Correlation and how each team has to complement each other to achieve the end objective
which is protecting the customers data the next chapter is about policies and when we say policies we are going to look into different components of policy because when we say uh policy a lot of people uh mistake it data privacy policy can be a section of information security policy but it's actually not you need to have a dedicated data privacy policy Because there are some specific components within the data privacy policy which you need to address right and uh when we say data privacy policy we also need uh need to look into uh have you
address different important questions which is required by the gdpr as a law as well so just showing you a glimpse of what are the things that you generally address what type of personal data do you gather because there are personal Data sensitive personal data and there are there could be criminal records which could be also be handled so all these categories have specific requirements of processing and uh and why do you gather it the you need to understand the purpose are you uh doing only the purpose which is being defined by you or you uh
doing it in any other un undefined purposes all these things to be captured and you need to clearly Define it because this becomes your Baseline basis the Baseline only all your process and the tools can work do you regularly review the data for accuracy yes you need to ensure the data is accurate you need you give a chance to the data subjects to make the corrections and rectification how do you store it and uh do you do you retain the data do you show do you store it encrypted or unencrypted way do you store it
in a cloud and what are the controls associated with it all these Things need to be captured part of your privacy policy how long you keep it retention period and what does what is the retention for each and every aspect of the processing because the retention could vary based on the processing operations uh there could be legal and regulator requirements which defines retention for certain activity good example is HR records that needs to be maintained maybe for five to ten years but depends on the country depends on The regulator requirements right so it did you
need to understand those regular retention requirements and then Define it in your policies and finally how can you readily comply with the individual's right to access Erasure and portability so do you have a system in place do you have a mechanism uh to address the data subject rights and how do you effectively do it uh because if you violate data subject rights that's a straightforward penalty under gdpr so Again these are some of the important questions that needs to be answered and also these are the components of the data privacy policy which is your privacy
policies procedures part of the governance the security controls which is going to protect them uh the information life cycle management which includes a collection uh which is uh your archival your disposal contracts notice inquiries compliance and dispute resolution how do you handle these Aspects uh finally the data handling procedures for departmental department so these are some of the important components on the right hand side I'm just displaying a mobile notice so uh this is a mobile channel for example if you are browsing through your mobile and you are accessing uh certain websites in this case
you need to provide the specific notice and the notice should be in a concise form for example the notice are a different structured there could Be a layered notice uh there could be a dashboard they could also needs to be customized according to the channels for example a mobile file notice should always be structured and layered and it cannot be a lengthy privacy notice isn't it because uh your your display size has to be taken into account and at the same time you also need to provide the most important aspects of the of the notice
in the in the first Glimpse right so these are some of the important Parameters which you need to take into account while uh while uh documenting your privacy policy right and these nuances needs to be uh to be documented so that it regulates into your design of the system as well as the tools and another important aspects is your employee personal data life cycle because a lot of time we discount the employee personal data we always focus on the customer but employees personal data is also an important aspect because Employees uh sometimes are not there
forever and sometimes an employee leaves an organization they might come back asking the organization to delete the data right so in that case having the data clear repository of the data and the flow of the data is very very important because lot of times this used to be a lot of incidents where disgruntled employees try to raise this particular option with them to erase all the data Right so especially when you are handling employee personal data you need to have a clear inventory and we so whenever there is any concerned data subject rights we can
we can handle it in the right way a and this is an example for example someone is applying for a job your CV cover letters and evaluation test results all these things contain personal data during recruiting your marital status contact info family status Bank details all these are Personal information collected during recruiting workplace access schedules assignments medical exams and your absence record and uh payroll payroll again has your contributions expenses benefits and all these things are personal data personal assessment your training aptitude skills development departure certificates official letters documents and end of contract so lot
of personal data is actually spread across different uh Events that happens in the employee life Journey so having that uh in a clearly captured so whenever there is a data subject rights we have to fulfill them as well so just giving you a glimpse of a practical aspect what we do part of the personal data life cycle of an employee in the next chapter is monitoring and auditing program performance part of this chapter we look into the data privacy Audits and monitoring as I saw As I said data privacy audits are gonna be the next
uh important thing that's going to come up in the market we see a lot of regulatory audits towards information security especially the certification orders or the Regal or the legal and Regulatory requirement if you are if you're operating in Middle East you would see the country specific cyber security standard or information security standards and if not you see in India ISO 27001 it's one of the de facto Or you are handling per payment card you have PCI DSS if you are handling uh HIPAA if you're a part of a Health Organization operating out of us
you want HIPAA regulation Bank specific regulations are there so audits are gonna be there to The Eternity right so they they will always exist and uh there will be one more addition in terms of data privacy orders which gonna be coming soon from different regulations especially gdpr is now coming with a Certification scheme which means that's going to come up very uh data privacy audits are gonna come up in full fledged right and this can also come up in markets like India when the pdpl comes into effect we'll see a lot of data privacy audits
come into picture as well right so to do audits you need to have a complete understanding of whatever we discussed so far and we will we will check the requirement from the law regulation and the contract and verify Whether the organization have fulfilled them right so control maturity assessment data life cycle management data processes review all these are some of the important aspects of the Audits and monitoring that organization need to comply uh chapter 8 is a training and awareness this is a good slide which I found in Internet uh which is explaining the concepts
in a very uh nice and simple way data minimization collect the Minimum data of data what is necessary to achieve the purpose when collecting personal data we often don't need everything right sometimes people just collect for the sake of collecting it and maintaining them is gonna be a big trouble because whenever data breach happens and it's been found that you had unnecessary data it's gonna have it's gonna just add the extra count of penalty which you're gonna face previously by Design if you are involved In designing products or Services think about the ways you can
build strong data protection into them data protection must be addressed at the beginning of the design process very very very important data privacy by Design is not a retrofit Theory it also it always needs to start whenever you are going to start any data privacy program or data privacy implementation right a good example is if the design is not right the implementation is always going to Have a flaw right so that is why privacy by design has to be in call Incorporated at the beginning of any process access and correction always respect the data subjects
rights and allow them to make those correction changes or exercise those rights international data transfer very very sensitive in the European Union region if you are transferring the data across the Glo across your borders be careful in terms of what was your valid instruments to Travel and you are expecting the requirements of customers as well as the laws and regulations and these are these are some of the interesting ways just you can make them people aware because it's not just confined to the data privacy team uh if each and every individual within the organizations are
accountable for data privacy this needs to be uh this needs to be uh brought in as a cultural change right and uh chapter 9 is data subject rights Uh very very important for you to understand what are the different rights which are available for uh individuals it varies from uh regulation to regulations and uh so it's not the same across different countries these are the reference coming from gdpr uh right to limit processing which is this is more or less right to restriction right to challenge the legitimacy of processing which is right to object transmission
or personal data and structure commonly Used is right to portability right to be evaluated based on automated processing you this is right to uh not uh right to be put not to put against automated decision making transparency controller must inform this is right to information uh and right to access right to know if data is processed B access this data so the first one is right to information the next one is right to access and it's right to be forgotten which is your Right to be erased right to Erasure and right to be forgotten okay
so we will see the the nuances of the for example all these rights are not absolute that is another very very important factor for example there are as I said the legal requirement always takes a precedence if I go and ask my company to delete all my data which means even my HR hrms data the company may not be obliged to do it Because they have their own legal requirements coming from the from the law of the land which mandates them to maintain these records for next five years or ten years so you need to
understand these aspects that data subject rights may not be absolute in nature that is where we need to have a Consulting process involved whenever you are in doubt please refer to the data protection office or the legal team to understand the intricacies involved as I Said right to object right to restriction all these rights are not absolute at all you need to see the facets of the request sometimes there could be a disgruntled employee who making an accessory request in that case how do you handle such requests all these things we will discuss the Practical
aspects of it during our course okay uh chapter 10 which is the final chapter of the course which is the data breach Incident Management how do you handle data breach and how what is the difference between your normal information security breach and your data personal data data breach because as I said there could be a legal requirement which is coming from European gdpr which is you have to report within 72 hours at the same time whenever there is a risk involved we need to inform the regulatory Authority and if there is a high risk for
the data Subject you need to inform the data subject as well all these decisions are very very important because these decision can be a make or break of the organization if you do not inform a data subject in time then the data subject is is bound to make a lawsuit against a company which could which could have a devastating effect both in terms of commercial as well as the reputation of the organization so it is very very important to have a robot first incident Management and data breach management practice within the organization as a data
protection manager you need to data privacy manager you need to ensure the the legal and regulated requirements are Incorporated the the process is set up and how do you how do you take up those communication because these communications are very sensitive and as I said these are typically the make or break decisions if you make a wrong decision here you could end up having Penalty at the same time you might risk facing customers lawsuits and losing the reputation of customers so and at the same time not every incident needs to be reported to customers not
every incident needs to be reported to the data protection authority so these decisions have those again intricacy for example I I'll always give this classical example A lot of people uh uh find it amusing because my data is leaked uh for example I lose my pen drive and my pen drive had Encryption okay and the data is completely encrypted but uh how do you handle the situation this doesn't need to be reported to a data subject because the data is completely encrypted I don't need to inform the data subject I already have the controls which
is required to protect them and and I clearly say there is no high risk involved here in terms of the data affecting my data subject so these uh these nuances we will discuss during the Session in terms of how do you handle such incidents and how do you actually draft a incident response plan so these are the uh the course chapters which we will be discussing during our session and I have completed the course content at a high level and we will discuss all these topics in depth whenever we We join our official sessions a
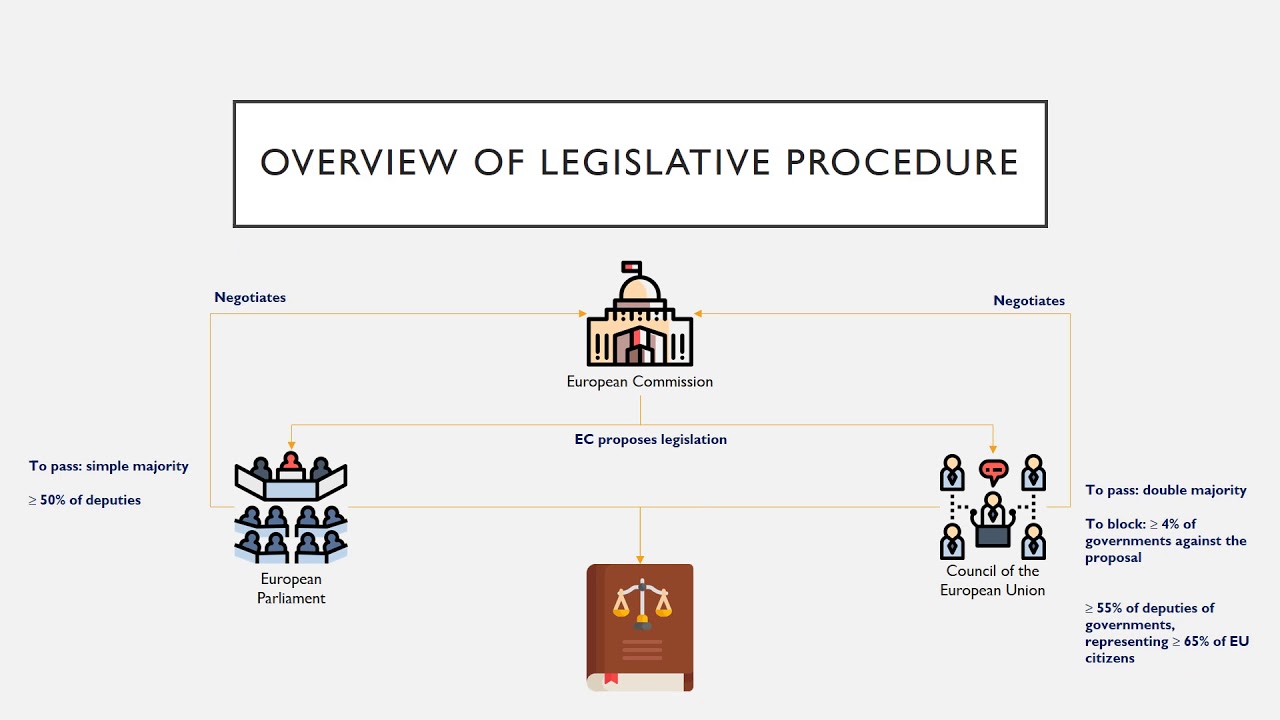
few interview questions are there which is like difference between a Regulation and directive uh so this was a request that uh discussed few interview questions I came up with uh seven different questions in the previous session as well uh different between regulation and directive regulation means it doesn't need a specific implementation this is coming from the European Union region uh gdpr is a regulation we have directives like 1995 directive uh or your e-premacy director which will leave the option of Implementation to the member state but regulation is being implemented at the European Union level which
does not require any other further implementation uh modification at the member state level what type of data lies beyond the scope of gdpr anonymous data is completely uh is not under the scope of gdpr but pseudonymous data is part of gdpr that's a clear differentiation what is layered data privacy notice uh data privacy notice as I said can have Multiple layers uh which means the first layer will be just defining what is the purpose of the collection and uh who is collecting it and uh what are the controls implemented so then you can go into
other details of retention all these things so that is layered privacy notice uh based on the it is it is in a very defined lot people can only read certain amount of information at a point of time if I show a 10 20 to 15 pages notice at the first instance no one is Going to read that isn't it that is why layered notice are designed in a way to uh it's mostly from the thought process of design thinking to make people actually appreciate the concept okay the regulation is gdpr example directives 1995 directive uh
regulations are for uh implemented at European Union level okay they don't need a national implementation uh mechanism directives are left for the national for the member State to decide the way of implementation okay that is the drawback of 1995 directive we will discuss all these things in detail when we go into the cipp course because in Capp we have a dedicated section one where we discuss the different directives and the gdpr what were the drawbacks of the directives that was rectified part of the gdpr which is the form of a regulation okay uh what is
the time time limit for complying data access requests It is uh one month and it can be extended for uh based on certain complexity we need to inform the data subject prior to that what are the available international data transfer instruments which we discussed which is the adequacy decision the uh additional safeguards which is your sscs which is your uh which is your contract which is your certifications and we also have binding corporate rules and these are some of The international data transfer instruments what is the time limit for informing the authorities about data breach
as I said 72 hours and what condition data subject needs to be informed whenever the the risk materializes into high risk for a data subject that is when you need to inform the data subject what are the categories of gdpr violation that attracts maximum penalty there are three to four categories which attracts maximum Penalty which is violating the data privacy principle violating data subject rights not obliging with the data protection authorities instructions so these are some of the categories that attracts maximum penalty the penalty is four percent of annual term annual Global turnover or 20
million euros this is the highest category the second category lowest which is uh two percent of the annual Global turnover or 10 million whichever is higher So these are some of the interview questions which I thought I'll just discuss with you and apart from that exam roadmap the course is designed for 32 hours which will spread a course maximum four to five weeks uh depends on the time slot we generally take three hours for a day which means we cover six hours in a week so it generally spans around four to five weeks uh then
you need to uh once you complete the infosec train course you need to start a self Study which is very very important because the material will cover all the requirements for the session but you need to spend your own time understanding these things again just by reading the official book as well as certain uh other materials which I'll be passing on right and this will require at least two to four weeks because you understand the weak areas during the session there are there are different concepts we are going to discuss someone Might be pick up
certain Concepts very easily certain concert will be difficult for you to digest so take that two to four weeks to identify your week areas focus on them and grasp all the concepts fundamentally correct and then the final one or two weeks is for practicing the Q and A's this is very very important because without doing a q a you will not be prepared for the exam please practice the questions which is there with the IEP 25 questions and and with that you Will you will definitely get the confidence that you are ready for the exam
and finally the exam day you can just uh do it a day before based on the availability and you can track the exam so in short you can definitely crack this exam two months maximum three months for people who are starting a fresh okay or starting the domain completely new and they are not from information security background then probably you can take a little more time There is no there is nothing wrong in terms of extending the course to three months or four months before taking the exam because the exam is bit costly so practice
well before giving the exam right and uh everyone who was taking up the course has very high chances of passing the exam I personally say this not just because I'm the trainer because you are getting not just the concepts uh but you're also getting the Practical Aspects as well as the exam training orientation right so you have a very high chance of clearing this exam as well


![IAPP CIPM Workshop: Your Roadmap to Privacy Leadership | What is Data Privacy [Part 1]](https://img.youtube.com/vi/HaofmRp2jE4/maxresdefault.jpg)